Magecart Attack Steals Credit Cards from Website Customers Checkout
In 2026, a sophisticated web-skimming campaign targeting online shoppers has intensified, actively compromising e-commerce websites and extracting sensitive payment information during checkout...
In 2026, a sophisticated web-skimming campaign targeting online shoppers has intensified, actively compromising e-commerce websites and extracting sensitive payment information during checkout processes.
The attack, identified as part of the broader Magecart family of threats, represents an evolving challenge to online retail security.
Threat researchers have documented extensive infrastructure associated with this long-running campaign, which has operated since at least early 2022.
The malicious network targets major payment providers including American Express, Diners Club, Discover, Mastercard, JCB, and UnionPay, potentially affecting millions of customers globally.
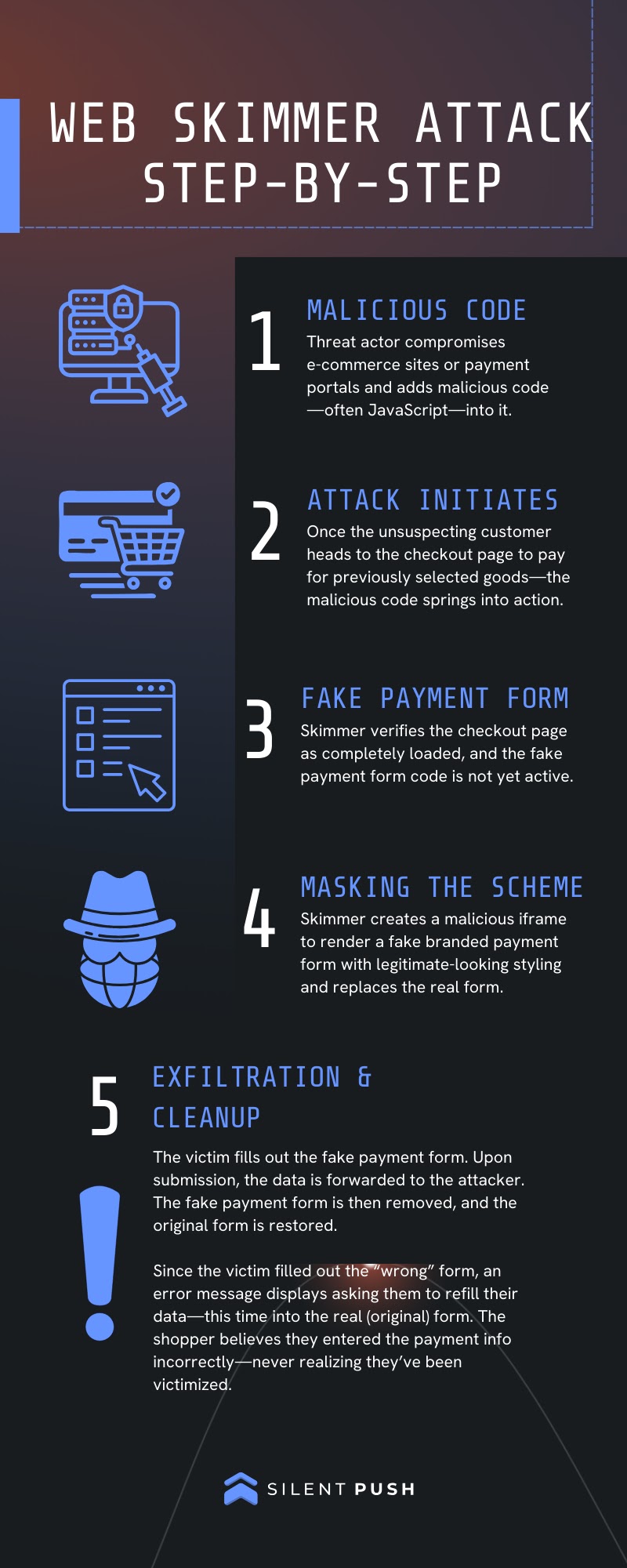
The attack operates through JavaScript injection, where malicious code embeds itself into legitimate e-commerce websites without triggering obvious security alerts.
Once injected, the code remains dormant until visitors reach the checkout page, at which point it initiates its credential-stealing payload.
The infrastructure relies on compromised domains and bulletproof hosting providers to maintain persistence and avoid detection.
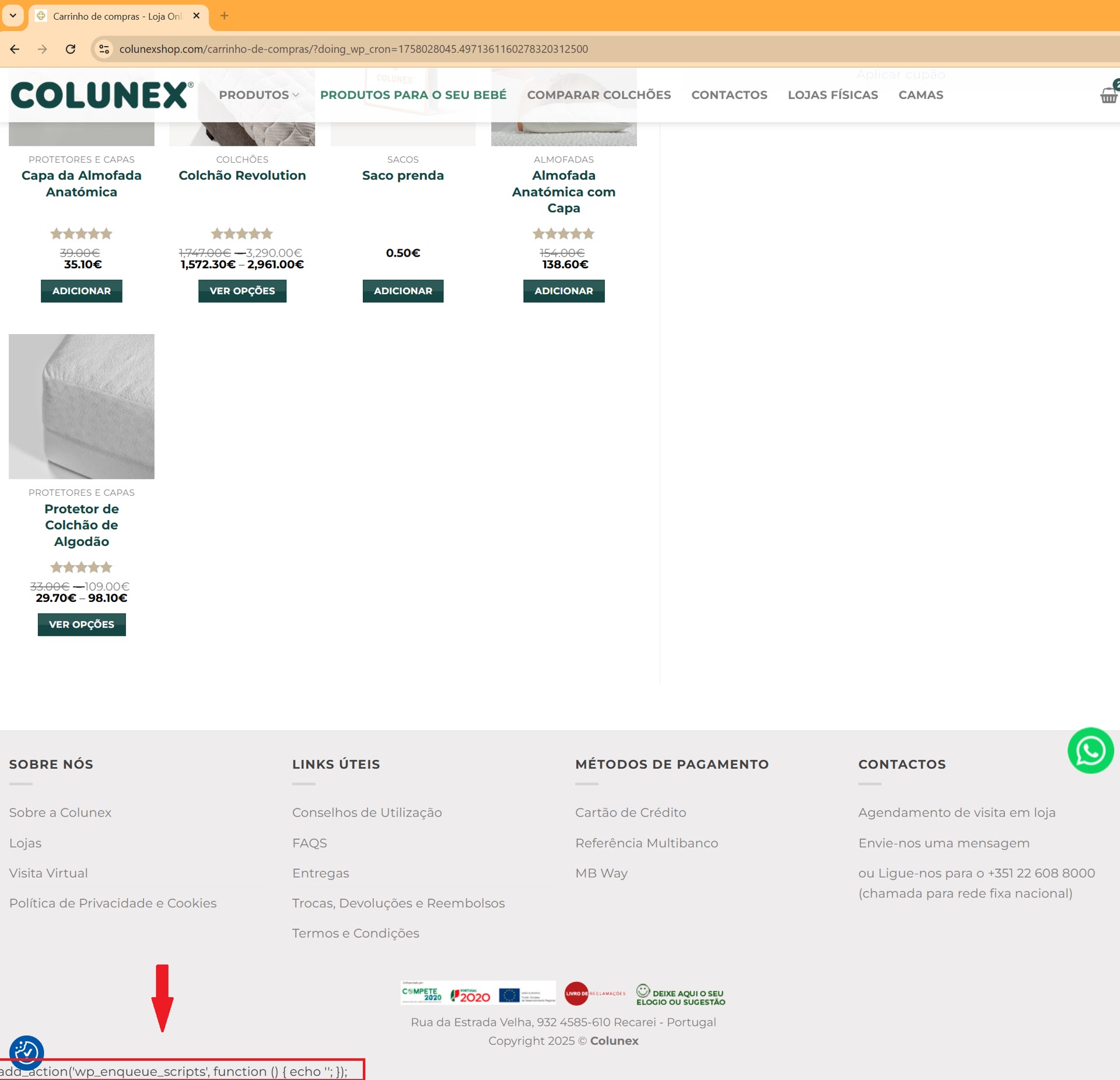
Silent Push analysts and researchers noted that the attackers have advanced knowledge of WordPress internals, leveraging lesser-known features like wp_enqueue_scripts action hooks to integrate malicious scripts into the website rendering process.
The technical sophistication lies in how the malware creates a convincing facade during the payment process.
The skimmer establishes a MutationObserver to monitor webpage changes in real-time, ensuring continuous monitoring of the payment form environment.
![Malicious file callout on the checkout page for colunexshop[.]com (Source - Silent Push)](https://hackersradar.com/wp-content/uploads/2026/01/content_1768384831_1216.jpg)
It then hides the legitimate Stripe payment form and injects a nearly identical fake form that captures card numbers, expiration dates, CVV codes, and billing information.
The fake form includes brand detection logic that recognizes card types and displays corresponding brand images, reinforcing legitimacy to victims.
Sophisticated Data Exfiltration Mechanism
The data collection process captures more than payment details. The malware monitors every input field on the checkout page, harvesting names, addresses, and email information.
Once victims complete the form and click the Place Order button, the skimmer compiles all collected data into a structured object, applies XOR encryption with a hardcoded key of 777, and encodes it in Base64 format.
The encrypted payload then transmits via HTTP POST request to exfiltration servers located on compromised infrastructure.
The attack exploits user psychology by displaying payment errors after form submission, misleading victims into believing they entered incorrect information.
Unsuspecting customers typically re-enter credentials into the legitimate form, completing their purchase successfully while remaining unaware their data was already stolen.
This psychological manipulation dramatically increases attack success rates by avoiding suspicion.
The malware includes evasion tactics that detect WordPress administrator status through the admin bar element and automatically disables itself when administrators view the site, significantly extending the campaign’s operational lifespan.
Security researchers predict this multi-year threat will continue targeting vulnerable online stores throughout 2026.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.