macOS Tahoe Feature Warns Users Against ClickFix Attacks
Apple has incorporated a new security mechanism into the macOS Tahoe 26.4 release candidate, specifically designed to protect users from social engineering campaigns known as ClickFix attacks....
Apple has incorporated a new security mechanism into the macOS Tahoe 26.4 release candidate, specifically designed to protect users from social engineering campaigns known as ClickFix attacks.
Discovered by users testing the latest OS build and highlighted in a popular Reddit post on r/MacOSBeta, the undocumented feature actively blocks the execution of potentially malicious commands pasted into the macOS Terminal.
This update addresses a critical security gap that allowed user-initiated command execution to bypass standard security boundaries. ClickFix is a deceptive social engineering technique that relies on user interaction rather than traditional software exploitation.
Threat actors present victims with fake error messages, often masquerading as browser updates or security verification checks. These prompts instruct the user to copy a provided command and paste it into their command-line interface.
Because the user manually executes the command, the malicious payload can easily bypass typical endpoint detection systems.
Attackers frequently use this method to deliver malware or establish persistent backdoors on targeted systems.
ClickFix Protection macOS Tahoe 26.4
In macOS Tahoe 26.4, the Terminal application now monitors clipboard activity for potentially dangerous commands, particularly those copied from web browsers like Safari.
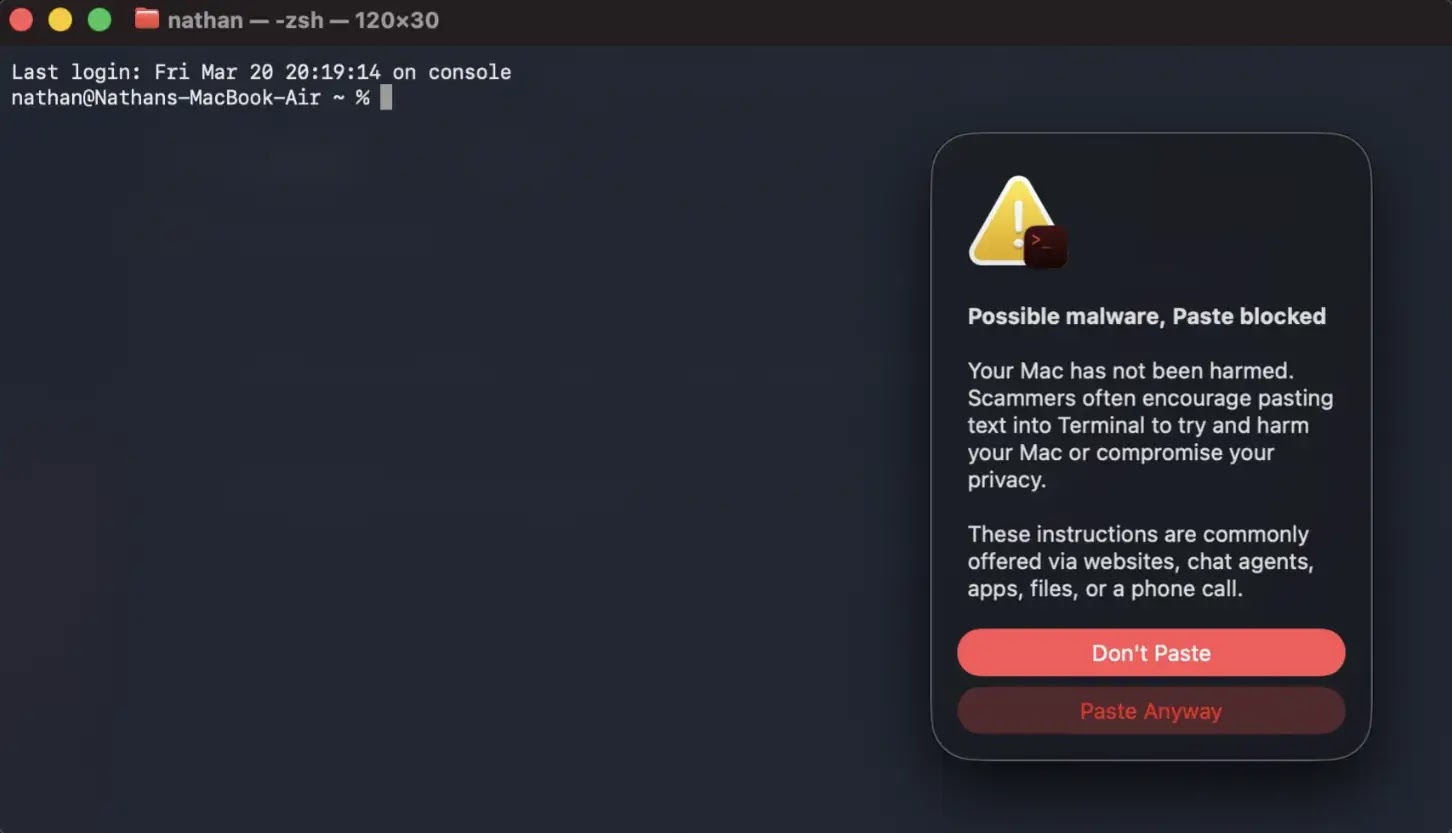
When a user attempts to paste a suspicious string, the operating system intercepts the paste operation, suspends execution, and displays a warning prompt.
Security analysts and Reddit users note that these warnings are designed to interrupt the attack chain by forcing the user to pause and read before the payload executes.
The detection mechanism specifically triggers when a user attempts to paste suspicious commands from external applications into the Terminal interface.
Reddit users speculate the Terminal application may scan pasted entries for typical malware signatures, such as downloading and executing scripts from untrusted websites.
Upon detection, the enforcement action immediately blocks the paste operation and delays any potential command execution.
The system then generates an alert header stating, “Possible malware, Paste blocked,” to communicate the threat clearly.
To provide further context, the warning explains that scammers often encourage pasting text from websites, chat agents, or files to compromise privacy or harm the system.
At this prompt, users are presented with two options: a “Don’t Paste” button to safely cancel the operation, and a “Paste Anyway” button to bypass the warning if the code is trusted.
To accommodate experienced developers and system administrators, the alert triggers only once per session, reducing notification fatigue.
Additional macOS 26.4 Developer Updates
Beyond the new Terminal protections, the official macOS Tahoe 26.4 release notes detail several critical updates for developers and system administrators.
Apple has accelerated the deprecation of Rosetta, reminding users that macOS Tahoe 26 is the final release to support Intel-based Macs.
Organizations managing enterprise devices can control these notifications using the allowRosettaUsageAwareness configuration key.
The update resolves a virtualization bug that caused new macOS Tahoe virtual machine installations to boot to a black screen on certain hardware configurations.
It also fixes a networking memory leak involving Automatic proxy configuration (PAC) objects. For software testing, Apple notes that the Address Sanitizer and Thread Sanitizer tools might hang when building with older software, requiring an upgrade to Xcode 26.4.
Developers using Background Assets can now programmatically check the local availability of asset packs while offline, improving app performance.
Additionally, AppKit receives a fix ensuring window resize pointers properly follow custom corner shapes.
StoreKit introduces new fields to track transaction revocation types and percentages, giving developers better insights into refunded purchases.
Finally, network administrators gain support for Network MIDI 2.0 sessions over local UDP transport, enabling legacy and modern protocol communication with improved wireless data reliability.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.