LockBit 5.0 Ransomware Attacks Windows, Linux LockBit’s Version
A new, highly potent version of LockBit ransomware, LockBit 5.0, has emerged, presenting a significant threat to businesses globally by targeting multiple operating systems. Released in September...
A new, highly potent version of LockBit ransomware, LockBit 5.0, has emerged, presenting a significant threat to businesses globally by targeting multiple operating systems. Released in September 2025, this iteration represents a major upgrade for one of the most active ransomware families in recent years.
This version supports Windows, Linux, and ESXi platforms, making it a versatile threat capable of attacking diverse infrastructure environments.
The ransomware operates under a ransomware-as-a-service model, employing a double-extortion scheme that encrypts files while simultaneously stealing data to pressure victims into paying ransoms.
The malware primarily targets the U.S. business sector, with private companies accounting for approximately 67% of recorded victims.
Other affected sectors include manufacturing, healthcare, education, financial services, and government agencies.
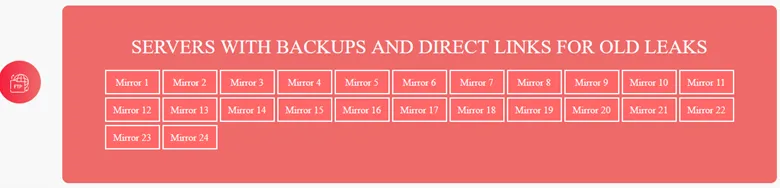
Since December 2025, the LockBit data leak site has documented 60 victim entries, demonstrating the widespread impact of this campaign.
What makes this version particularly concerning is its advertised capability to work on all versions of Proxmox, an open-source virtualization platform increasingly adopted by enterprises as an alternative to commercial hypervisors.
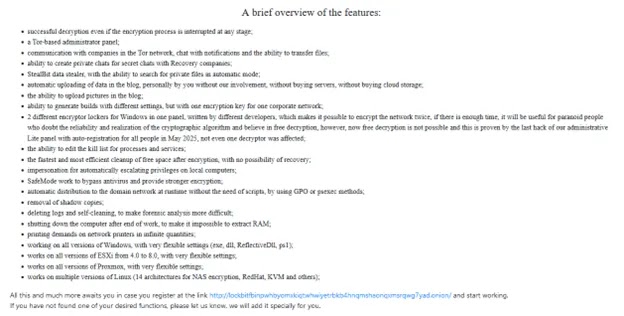
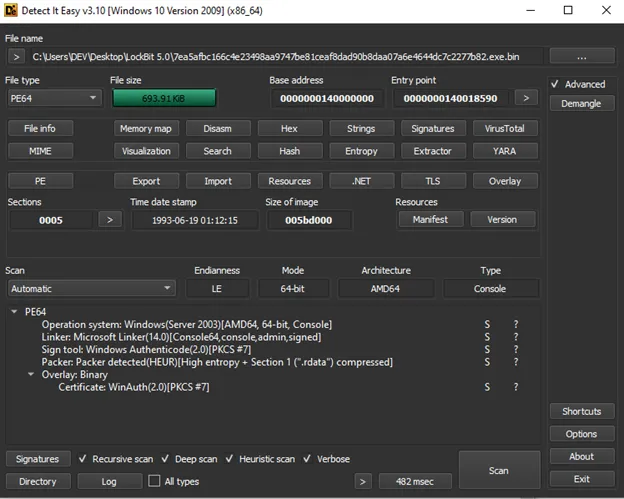
Acronis analysts identified that LockBit 5.0 shares similarities with its predecessor, version 4, but introduces enhanced defense evasion capabilities and faster encryption speeds.
The Windows variant employs the most sophisticated anti-analysis techniques among all versions, including packing mechanisms, DLL unhooking, process hollowing, and Event Tracing for Windows patching.
Additionally, the malware clears all available system logs to eliminate forensic evidence. The Linux and ESXi versions, while not packed, encrypt nearly all their strings to avoid detection.
All three platform versions utilize identical encryption algorithms, combining XChaCha20 for symmetric encryption with Curve25519 for asymmetric encryption. Each encrypted file receives a randomly generated 16-character extension, making identification more difficult.
The ransomware creates multiple encryption threads based on the number of system processors, ensuring rapid file encryption across infected environments.
Advanced Evasion and Persistence Mechanisms
The Windows version demonstrates particularly sophisticated evasion tactics designed to avoid security software and analysis tools.
The malware uses Mixed Boolean-Arithmetic obfuscation wrapped around return-address dependent hashing to conceal its true functionality.
It performs geolocation checks to avoid infecting systems in post-Soviet countries, a common trait among Russian-based malware families. Before encryption begins, LockBit checks system language settings and compares them against Russian language identifiers.
The ransomware employs process hollowing by injecting itself into the legitimate Windows defrag.exe utility, allowing it to execute under the guise of a trusted system process.
After completing encryption operations, LockBit patches the EtwEventWrite function by replacing its first byte with a return instruction, effectively disabling Event Tracing for Windows monitoring.
It then systematically clears all event logs using the EvtClearLog function, removing traces of its activities.
Infrastructure analysis revealed that LockBit’s data leak site was hosted on an IP address previously associated with SmokeLoader malware operations.
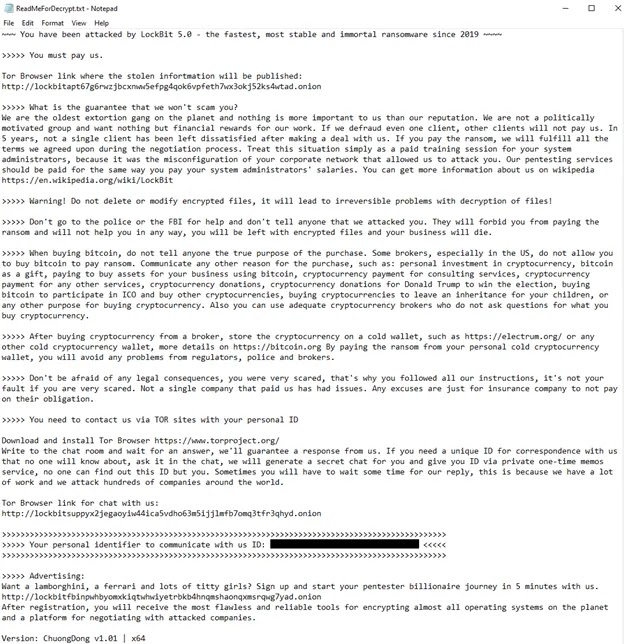
This connection suggests possible infrastructure sharing or cooperation between different cybercriminal groups, a common practice in underground markets.
Organizations should implement multi-layered security controls including regular offline backups, network segmentation, endpoint detection and response solutions, and timely patch management.
Employee security awareness training remains critical to prevent initial access through phishing campaigns. System administrators should monitor for suspicious process behavior, unexpected file encryption activity, and attempts to disable security logging mechanisms.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.