LockBit 5.0 Emerges: New Encryption & Sophisticated Anti-Analysis
LockBit 5.0 has emerged as the latest iteration of one of the world’s most active ransomware-as-a-service (RaaS) operations. This new version continues the group’s legacy of Sophisticated...
LockBit 5.0 has emerged as the latest iteration of one of the world’s most active ransomware-as-a-service (RaaS) operations. This new version continues the group’s legacy of Sophisticated Anti-Analysis capabilities that make detection and recovery exponentially more difficult for organizations.
The malware operates through a coordinated three-step attack process: initial system access through vulnerabilities or compromised credentials, lateral movement combined with privilege escalation, and finally, complete ransomware deployment across victim networks.
The financial impact of LockBit operations remains staggering. Between August 2021 and August 2022, the group claimed responsibility for 30.25 percent of all known ransomware attacks globally.
Even as law enforcement intensified operations against the group, LockBit maintained its dominance, accounting for approximately 21 percent of ransomware attacks in 2023 alone.
Companies spanning IT, electronics, law firms, and religious institutions have fallen victim to these attacks, with ransom payments and recovery costs reaching billions of dollars worldwide.
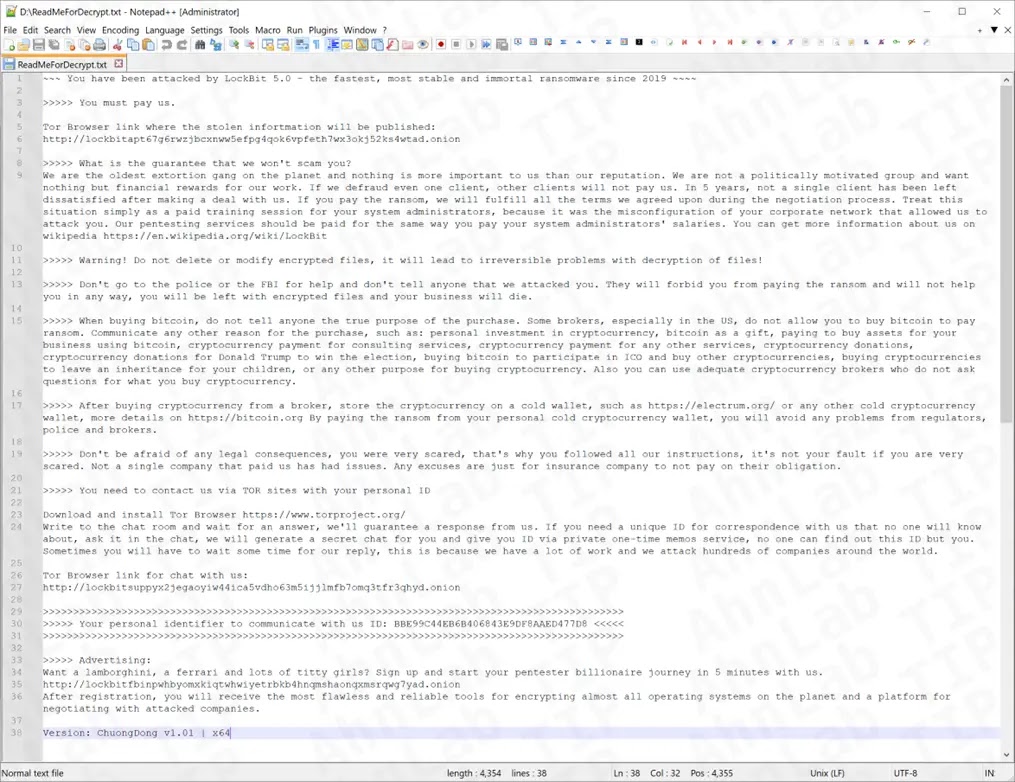
The group’s dark web platform continues to publicly list compromised organizations and their stolen data as a pressure tactic.
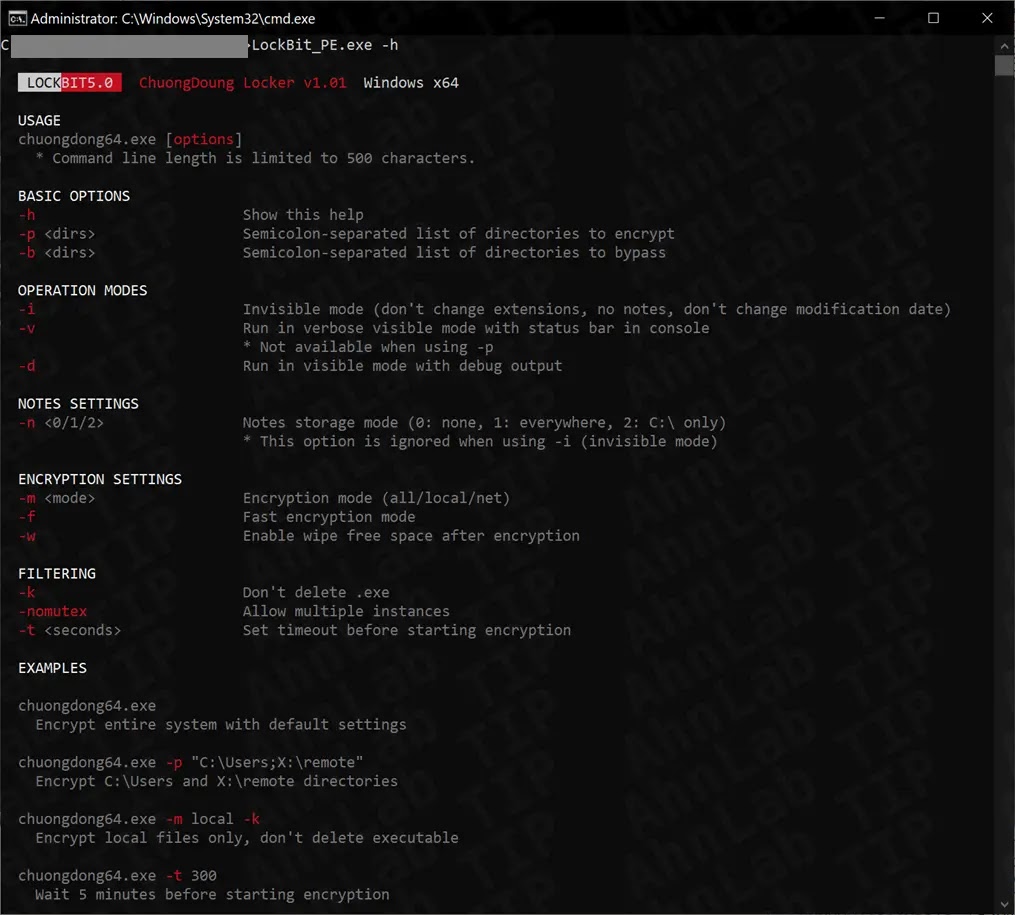
ASEC analysts noted that LockBit 5.0 introduces runtime flexibility, operating normally even when deployed without specific parameters.
The malware terminates Volume Shadow Copy Service-related processes to prevent system recovery attempts while employing advanced packing and obfuscation techniques to complicate static security analysis.
Most critically, the ransomware implements state-of-the-art cryptographic algorithms combining ChaCha20-Poly1305 for file encryption with X25519 and BLAKE2b for secure key exchange, making encrypted files impossible to recover using only local system information.
Advanced Encryption Mechanism
The encryption process represents a masterclass in modern cryptography implementation.
Before initiating file encryption, LockBit 5.0 systematically deletes temporary files from standard Windows paths including AppDataLocalTemp directories, removing unnecessary cache data to accelerate the encryption process.
The malware then disables critical system services using hardcoded hash values, targeting backup and security solutions including Veeam, Backup Exec, and Microsoft Edge Update services to eliminate competing protection mechanisms.
The actual encryption operates through an intricate mathematical process. The malware generates two separate 32-byte random numbers derived from system time and memory information.
Using elliptic curve cryptography, it derives the victim’s private key, generates corresponding public keys, and calculates a shared secret value combining the victim’s private key with the attacker’s public key.
For files under 8 megabytes, the first random number undergoes BLAKE2b hashing to generate a 32-byte encryption key, which then produces a 64-byte ChaCha20 key stream.
This key stream undergoes XOR operations with target data, creating the final encrypted file. When files exceed this threshold, LockBit 5.0 splits data into 8-megabyte chunks, processing each independently with custom hash functions.
After encryption completes, the malware appends critical metadata including file sizes, encrypted random numbers, authentication values, and the victim’s public key, ensuring only attackers possessing their private key can decrypt the data.
This technical sophistication reflects years of ransomware evolution, positioning LockBit 5.0 as one of the most formidable threats in the contemporary threat landscape.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.