Lapsus$ Hunters Launch ShinySp1d3r Scattered Resurface
After a period of silence, the notorious Scattered Lapsus$ Hunters threat group has resumed active operations following their high-profile supply chain attack targeting Salesforce third-party...
After a period of silence, the notorious Scattered Lapsus$ Hunters threat group has resumed active operations following their high-profile supply chain attack targeting Salesforce third-party integrations, including Gainsight and Salesloft.
Recent activity observed across underground Telegram channels and credential-trading forums shows the collective has rebuilt its operational structure and launched an aggressive recruitment campaign targeting insiders and initial access brokers.
The group is now promoting a new Ransomware-as-a-Service platform called ShinySp1d3r, described as a joint effort involving operators linked to ShinyHunters, Scattered Spider, and Lapsus$.
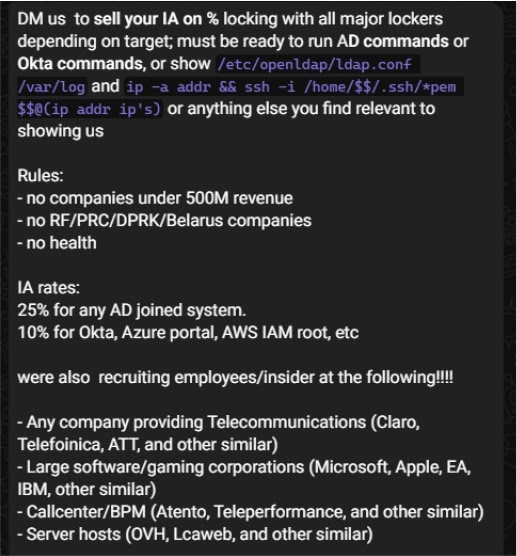
The resurgence marks a significant shift in the group’s operational strategy. Unlike previous campaigns that relied primarily on social engineering tactics, the collective is now pursuing a more structured approach focused on acquiring privileged access through insider collaboration and commission-based deals.
Their recruitment advertisements specify clear targeting criteria: organizations with annual revenues exceeding 500 million dollars, excluding entities in Russia, China, North Korea, Belarus, and the healthcare sector.
The group has established tiered commission structures, offering 25 percent for Active Directory-joined systems and 10 percent for cloud identity platforms such as Okta, Azure Portal, and AWS IAM root access.
CYFIRMA analysts identified the resurgence through monitoring of closed Telegram clusters and access-broker ecosystems where the group has been actively posting recruitment messages and negotiating initial access purchases.
The collective is specifically seeking insiders who can provide VPN, VDI, Citrix, or AnyDesk access from telecommunications providers, software and gaming corporations, and call-center environments.
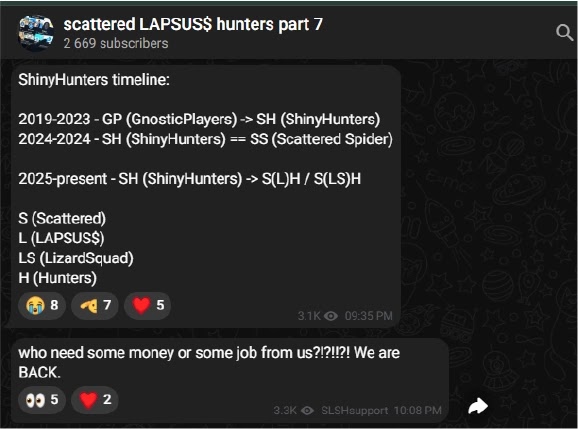
Chatroom discussions frequently reference the LizardSquad name, though these mentions appear to be part of a reputation-building strategy rather than evidence of a verified partnership.
The group has demonstrated its credibility by sharing leaked screenshots of a CrowdStrike internal dashboard and an Okta single sign-on page allegedly provided by an insider source.
Insider Recruitment and Operational Security Messaging
The threat actors have adopted a sophisticated approach to addressing potential insider concerns about detection.
Following the recent CrowdStrike insider incident, the group publicly reassured potential collaborators by claiming that informants within their operation would remain undetected.
They framed the CrowdStrike case as a self-inflicted disclosure resulting from a failed insider attempt, using this narrative to build confidence among prospective recruits.
This messaging strategy suggests the group understands the psychological barriers that prevent insiders from engaging in malicious activity and is actively working to overcome these concerns.
The development of ShinySp1d3r further indicates the collective is positioning itself for sustained operations throughout 2026, with public threats to compromise and leak additional customer data from targeted organizations.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.