IPVanish macOS VPN Flaw: Privilege Escalation Vulnerability Attackers
A critical privilege escalation vulnerability affects the IPVanish VPN application for macOS. This flaw enables any unprivileged local user to execute arbitrary code as root, requiring no user...
A critical privilege escalation vulnerability affects the IPVanish VPN application for macOS. This flaw enables any unprivileged local user to execute arbitrary code as root, requiring no user interaction.
The security failure completely bypasses macOS security features, including code signature verification, posing a severe risk to affected systems.
Attack Chain and Execution Flow
The vulnerability discovered by SecureLayer7 stems from the architectural design of the IPVanish VPN macOS application.
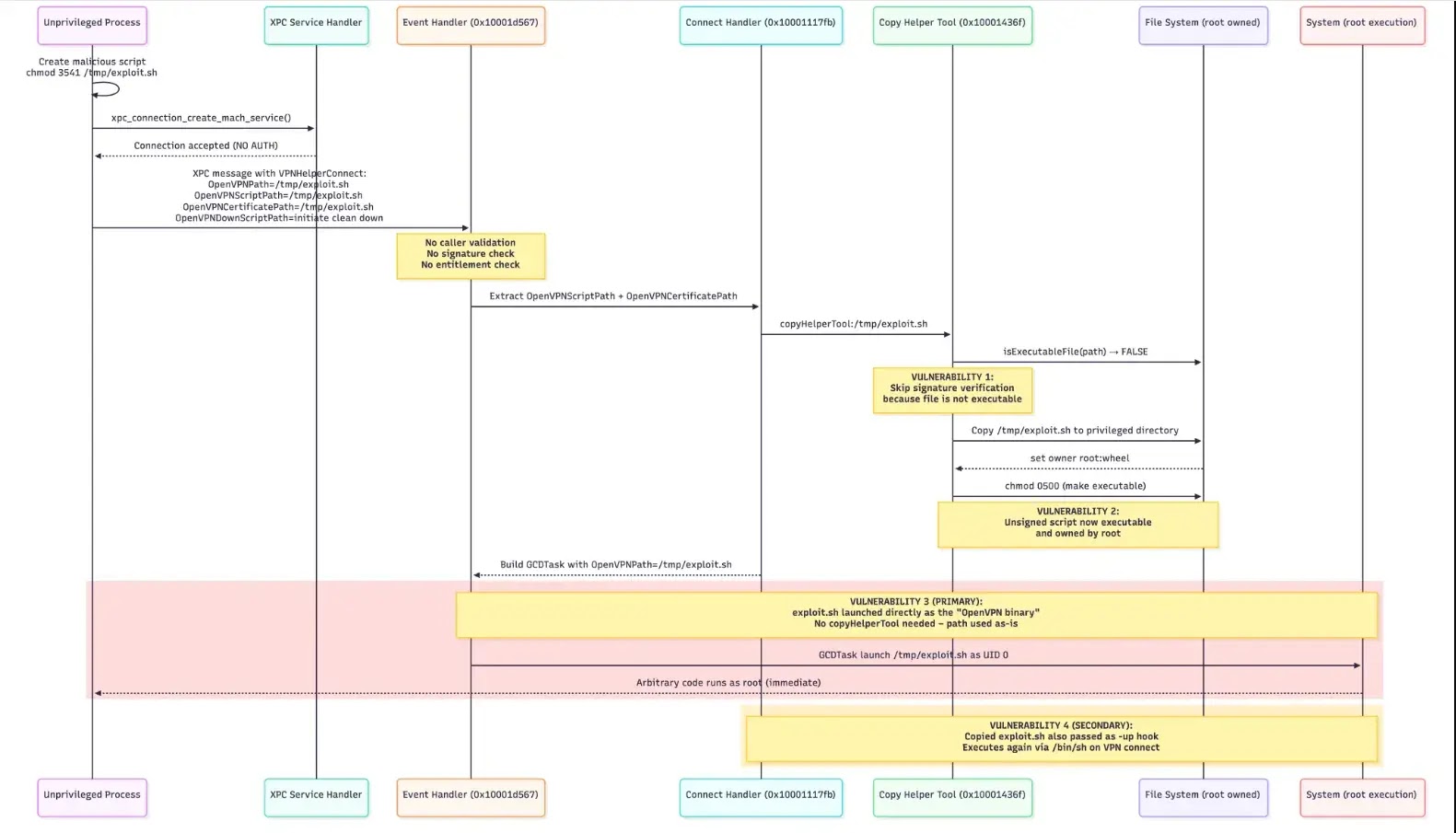
The application splits operations between a user-space bundle and a privileged helper tool (com.ipvanish.osx.vpnhelper) that operates with root privileges.
The core failure occurs when the helper tool creates an XPC listener but fails to authenticate connecting clients.
It never queries the caller’s effective user ID, verifies entitlements, or checks the bundle identifier against an allowlist.
| Category | Details |
|---|---|
| CVE ID | CVE-PENDING |
| CVSS Score | 8.8 (High) |
| CWE | CWE-269: Improper Privilege Management |
| Description | Unauthenticated XPC connections in the com.ipvanish.osx.vpnhelper daemon allow unprivileged processes to execute arbitrary code with root privileges, leading to a potential local privilege escalation. |
| Affected Version | IPVanish VPN for macOS (macOS 10.13+) |
This oversight allows any local process to send crafted XPC messages directly to the privileged helper.
Once connected, an attacker can dispatch a VPNHelperConnect command equipped with malicious parameters. The SecureLayer7 research highlights the exploit leverages two critical flaws.
First, the OpenVPNPath parameter is accepted directly from the unauthenticated message and passed to GCDTask without path or signature validation, enabling immediate arbitrary code execution as root.
Second, a logic error in the copyHelperTool:error: method bypasses code signature verification for non-executable files.
An attacker can supply an unsigned, non-executable script, which the helper copies to a root-owned directory.
| IOC Type | Indicator Details | Context |
|---|---|---|
| File Path | /tmp/ipvanish_exploit.sh |
Initial malicious payload created by the attacker paste.txt. |
| File Path | /Library/Application Support/com.ipvanish.osx.vpnhelper/ |
Destination directory for the copied root executable paste.txt. |
| XPC Service | com.ipvanish.osx.vpnhelper |
Vulnerable privileged helper tool managing the execution paste.txt. |
The helper then modifies the file permissions to make it executable, weaponizing the script as a secondary attack path via OpenVPN’s –up hook mechanism.
Mitigation and Remediation Measures
Securing the IPVanish VPN application requires a comprehensive overhaul of its privilege separation security controls.
SecureLayer7 emphasizes that the most critical immediate action is to implement robust caller authentication within the XPC event handler.
Developers must ensure the helper extracts the audit token from the XPC connection, creates a security task, and validates both the bundle identifier and team identifier to confirm the caller is the legitimate IPVanish application.
| Mitigation Category | Key Action |
|---|---|
| XPC Authentication | Extract audit tokens and verify the caller’s code signature and team ID before connection paste.txt. |
| Signature Verification | Validate code signatures on all files handled by the helper tool, ignoring the execute bit check paste.txt. |
| Path Whitelisting | Canonicalize and restrict file paths to approved application bundle directories paste.txt. |
Furthermore, the code-signature verification logic must be extensively revised. The current system only checks signatures on files that already have the execute bit set, which represents a fatal logical flaw.
According to SecureLayer7, the application must enforce signature verification on all copied files regardless of their permission status.
Finally, strict path allowlisting must be introduced to resolve symlinks and ensure that only files originating from authorized locations, such as the official application bundle resources, are processed by the helper tool.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.