Hackers Plant Stealthy BPFdoor Backdoors in Telecom Networks
A months-long investigation by Rapid7 Labs has exposed a sophisticated, state-sponsored espionage campaign perpetrated by the China-nexus threat actor Red Menshen. This group embedded some of the...
A months-long investigation by Rapid7 Labs has exposed a sophisticated, state-sponsored espionage campaign perpetrated by the China-nexus threat actor Red Menshen. This group embedded some of the most covert digital sleeper cells ever documented inside global telecommunications infrastructure.
Released on March 26, 2026, the findings reveal a deliberate shift from opportunistic hacking to long-term pre-positioning within the very backbone networks that underpin national and international communications.
Telecommunications networks carry government communications, authenticate subscriber identities, coordinate critical industries, and process signaling flows across national borders.
At their core, these environments rely on specialized protocols such as SS7, Diameter, and SCTP to manage subscriber identity, mobility, and global connectivity, making them uniquely valuable for intelligence collection far beyond what a conventional data breach enables.
Persistent access within a telecom core can expose subscriber identifiers, mobility events, authentication exchanges, and communication metadata, enabling large-scale tracking of high-value geopolitical targets.
Red Menshen has specifically targeted telecom providers across South Korea, Hong Kong, Myanmar, Malaysia, Egypt, and the Middle East, with collateral risk extending to government networks that depend on those carriers.
BPFdoor: A Kernel-Level Trapdoor
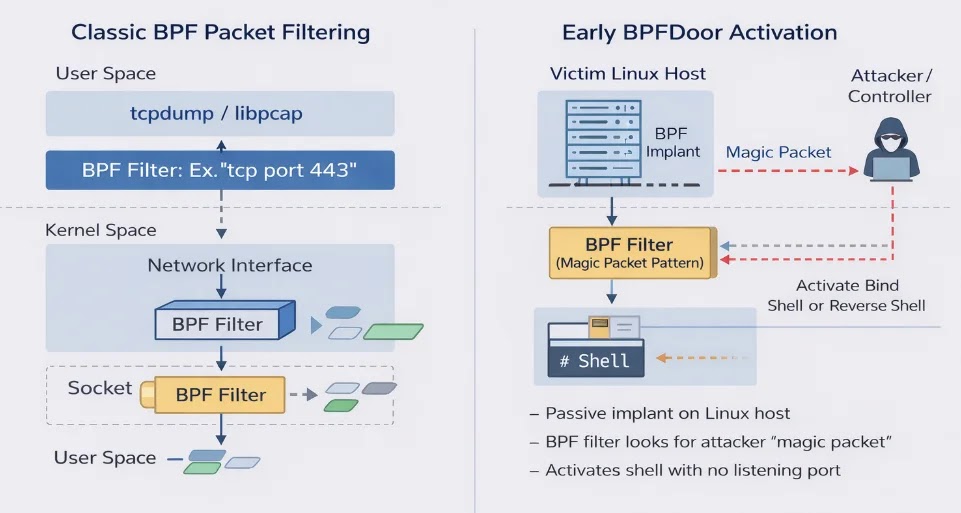
At the center of this campaign is BPFdoor, a stealth Linux backdoor engineered to operate within the operating system kernel by abusing Berkeley Packet Filter (BPF) functionality.
Unlike conventional malware, BPFdoor does not open listening ports or generate visible command-and-control beaconing. Instead, it installs a custom BPF filter inside the kernel that silently inspects incoming traffic, activating only when it receives a specially crafted “magic packet” containing a predefined byte sequence. Tools such as netstat, ss, or nmap show nothing unusual; the system appears entirely clean.
Rapid7 Labs identified a previously undocumented BPFdoor variant that significantly advances its stealth capabilities. Rather than relying on a detectable magic packet, the updated variant now conceals command triggers within legitimate HTTPS traffic, exploiting SSL termination points like load balancers and reverse proxies to deliver activation commands after decryption in the internal network zone.
A sophisticated “magic ruler” padding mechanism ensures a marker string (“9999”) always lands at a fixed 26-byte or 40-byte offset within inspected request data, allowing the implant to survive proxy header rewriting, effectively creating dynamic Layer-7 camouflage.
The variant also employs an ICMP-based control channel, where compromised servers relay commands to each other using crafted ICMP packets embedded with the value 0xFFFFFFFF as a “do not forward” terminal signal, enabling lateral propagation without standard C2 traffic.
Infrastructure-Level Masquerading
Some BPFdoor samples mimic legitimate processes on HPE ProLiant bare-metal servers, specifically impersonating hpasmlited, a daemon belonging to HPE’s Agentless Management Service, to blend into telecom hardware environments running 4G/5G core workloads.
Other samples spoof Docker and containerd components, targeting Kubernetes-hosted 5G core functions such as AMF, SMF, and UDM.
Initial access consistently targets edge infrastructure: Ivanti Connect Secure VPNs, Cisco and Juniper network devices, Fortinet firewalls, and VMware ESXi hosts. Post-exploitation tooling includes CrossC2, TinyShell, SSH brute-forcers, and custom ELF keyloggers with telecom-aware credential lists referencing terms like “imsi.”
Rapid7 has coordinated with national CERTs and government partners to notify affected organizations. The firm released a free, open-source scanning script capable of detecting both legacy and new BPFdoor variants to assist organizations in rapid exposure validation.
Defenders are strongly advised to expand visibility into kernel-level operations, raw BPF filter activity, and anomalous high-port behavior on Linux systems — areas where most organizations currently lack adequate monitoring depth.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.