Hackers Abuse VS Code to Execute Malicious Payloads
North Korean threat actors are weaponizing Microsoft Visual Studio Code, one of the world’s most popular code editors. This tactic marks a significant expansion of their attack capabilities....
North Korean threat actors are weaponizing Microsoft Visual Studio Code, one of the world’s most popular code editors. This tactic marks a significant expansion of their attack capabilities.
The Contagious Interview campaign has evolved significantly, shifting from traditional social engineering tactics to targeting developers through trusted development environments.
This new approach marks a concerning escalation in how adversaries exploit legitimate software tools to deliver sophisticated malware directly onto victim systems.
The attack chain begins when developers unknowingly clone malicious repositories, often disguised as recruitment assignments or technical job interviews.
The attack represents a shift in tactics beyond previously documented ClickFix-based delivery methods. Rather than relying on suspicious email links, attackers now embed malicious commands within Visual Studio Code configuration files.
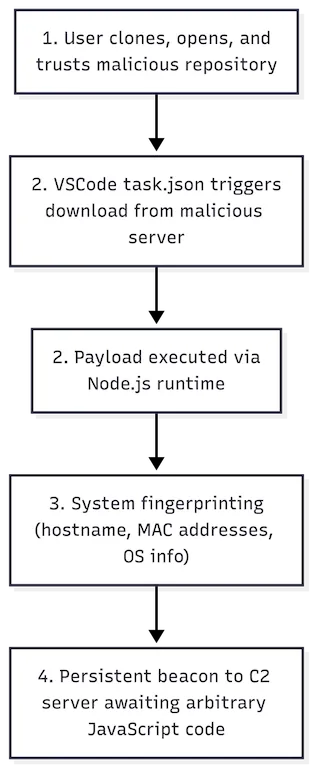
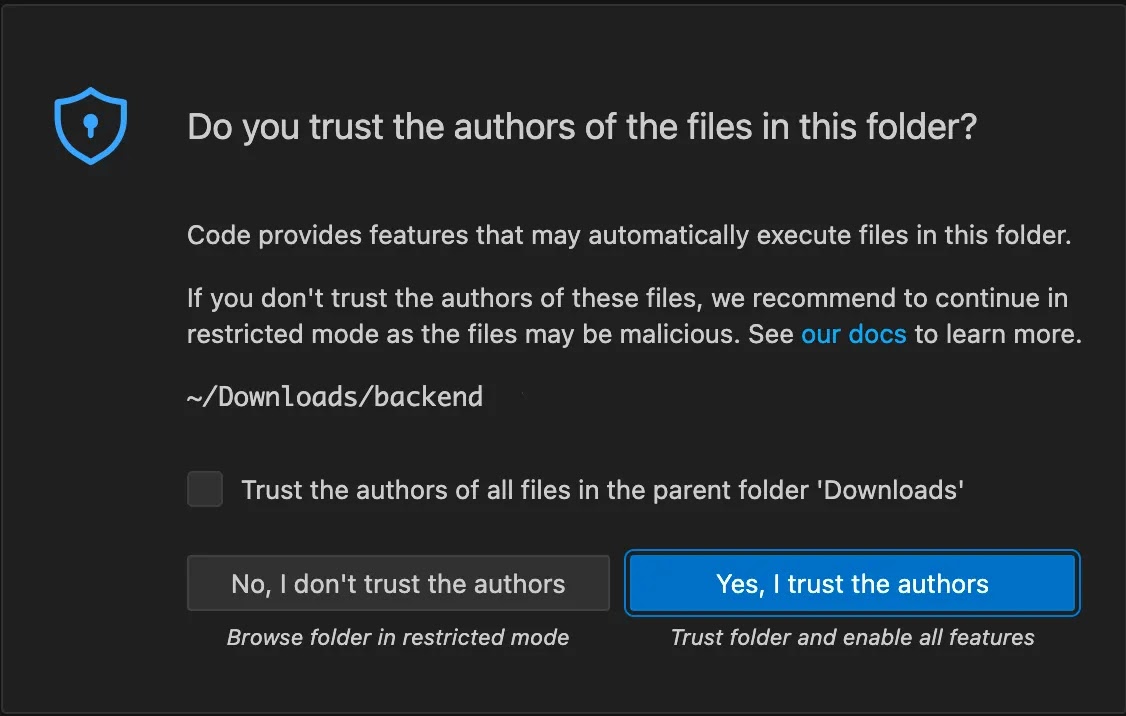
When a victim opens a compromised repository in Visual Studio Code and grants repository trust—a standard workflow action—the application automatically processes the repository’s tasks.json configuration file.
This file can contain embedded commands that execute arbitrary code on the system, effectively bypassing user awareness.
Jamf analysts and researchers identified additional abuse of Visual Studio Code’s task configuration files in December, discovering dictionary files containing heavily obfuscated JavaScript code.
This JavaScript executes silently when a victim opens a malicious repository. The security researchers also documented how attackers introduced increasingly sophisticated obfuscation techniques to evade detection and analysis.
The Infection Mechanism and Execution Flow
The infection begins when a developer clones and opens a malicious Git repository hosted on GitHub or GitLab.
On macOS systems, the malware uses a background shell command combining nohup bash with curl to retrieve a JavaScript payload remotely from Vercel-hosted infrastructure.
The payload executes directly in the Node.js runtime, allowing the attack to continue even if Visual Studio Code closes.
This persistence mechanism is particularly effective because it operates independently from the editor’s process.
Once executed, the JavaScript payload establishes a persistent connection to a command-and-control server located at 87.236.177.93, beaconing every five seconds.

The malware collects system information including hostname, MAC addresses, and operating system details, then sends this data to attackers for further tasking.
The payload maintains a persistent execution loop capable of accepting additional JavaScript instructions from the C2 server, enabling attackers to execute arbitrary commands and maintain long-term access.
Developers should carefully review repository contents before marking them as trusted and scrutinize tasks.json files for suspicious configurations that could indicate malicious intent.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.