Gootloader Evades Most Security Tools with Low Detection Rate
After a period of dormancy, Gootloader has reemerged as a serious threat, returning in November 2025 with renewed capabilities specifically engineered to bypass modern security systems. This malware...
After a period of dormancy, Gootloader has reemerged as a serious threat, returning in November 2025 with renewed capabilities specifically engineered to bypass modern security systems.
This malware serves as an initial access broker, meaning its developers create the entry point for ransomware attacks and then hand over control to other threat actors who deploy the actual encryption tools.
The malware’s effectiveness lies in its ability to evade detection while maintaining functionality on compromised systems.
Organizations worldwide are racing to defend against this growing menace as the threat actor group known as Vanilla Tempest continues leveraging it in conjunction with Rhysida ransomware campaigns.
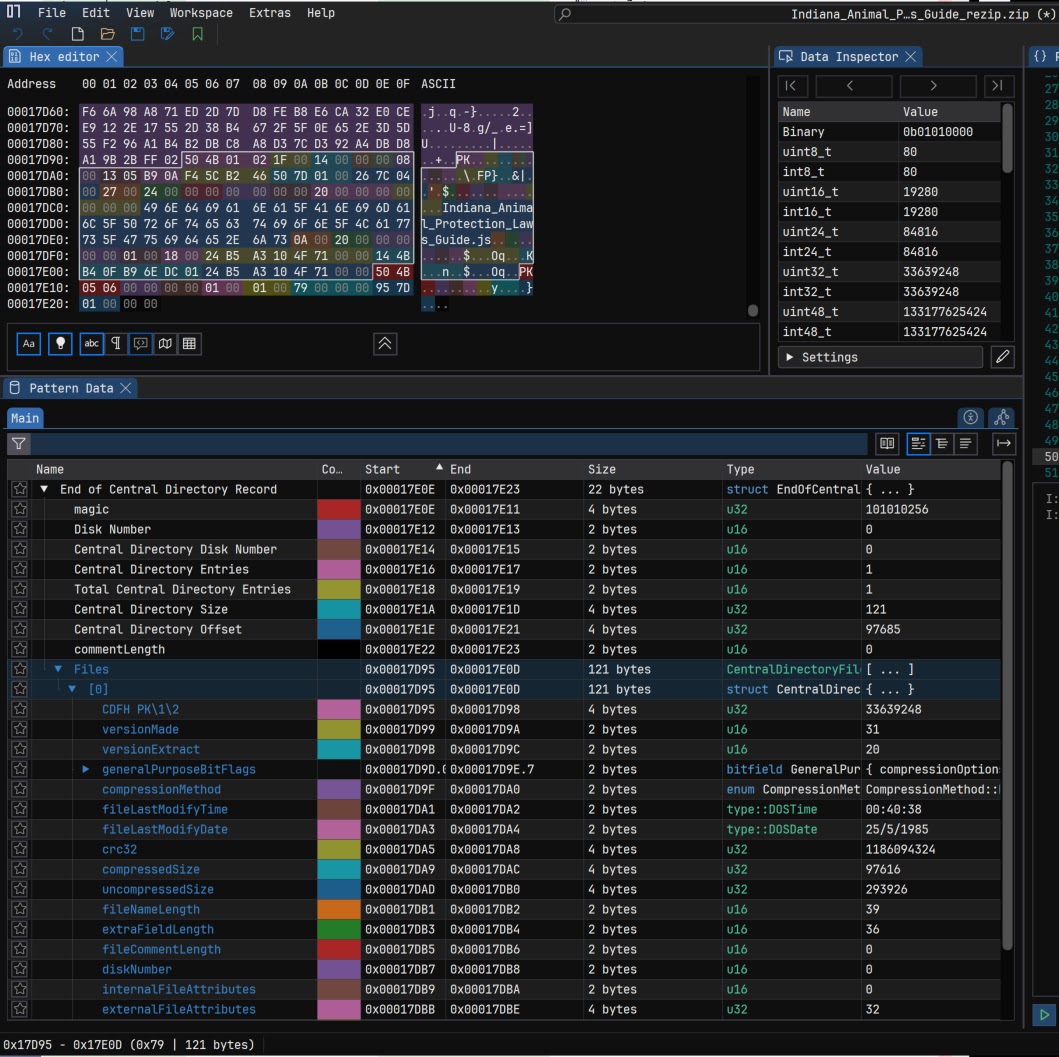
The malware travels through compromised websites embedded within deceptive ZIP archives that are deliberately malformed to confuse security tools.
When users download what appears to be a legitimate document, they receive a file packed with hundreds of concatenated ZIP archives designed to bypass both automated analysis and specialized extraction software.
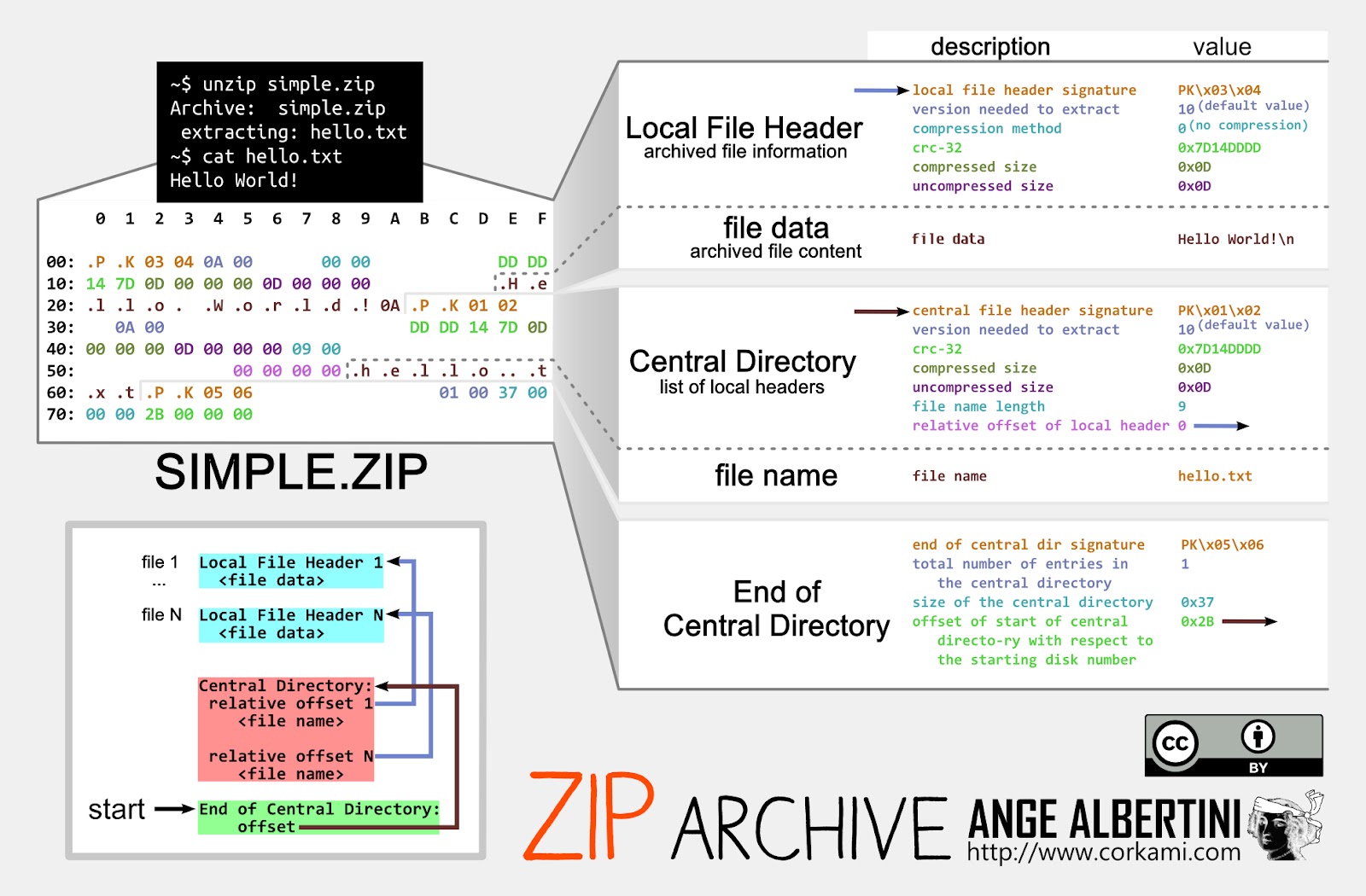
The outer packaging is crafted so that most unarchiving tools like 7zip and WinRAR cannot extract the contents, yet the default Windows unarchiver opens it reliably, ensuring victims can execute the payload while defenders struggle to analyze it.
Expel analysts noted that Gootloader’s ZIP archives contain multiple sophisticated evasion features working in concert.
The structure includes hundreds of copies concatenated together, randomly generated values in critical fields, and deliberately truncated sections that cause parsing errors in traditional security scanners.
In previous years, this malware represented eleven percent of all malware detected bypassing security solutions, demonstrating its proven track record.
The Infection Mechanism and Persistence Strategy
Once the malicious ZIP file is opened, a JScript file embedded within executes automatically when double-clicked.
The script runs through Windows Script Host and immediately establishes persistence by creating link files in the user’s Startup folder. These links point to a second JScript file stored in a random directory, ensuring the malware reactivates with every system restart.
The JScript then spawns PowerShell with heavily obfuscated commands that communicate with attacker infrastructure to download secondary payloads.
The evasion strategy extends further through a technique called hashbusting, where every downloaded file contains unique characteristics.
Each victim receives a completely different archive structure with randomized field values, making signature-based detection virtually impossible. Organizations cannot rely on file hashes or static patterns to identify these samples across their networks.
Security teams should prioritize preventing JScript execution through Group Policy Objects by reassociating .js files to Notepad instead of Windows Script Host.
Additional protections include monitoring for suspicious PowerShell process chains, detecting NTFS shortname usage during script execution, and scanning for malformed ZIP structures using specialized YARA rules.
Early detection at the ZIP delivery stage offers the best opportunity to prevent ransomware deployment before attackers gain deeper system access.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.