Google Exposes ShinyHunters’ Expanded Threat Activity & New
The ShinyHunters threat group has expanded its extortion operations, now deploying sophisticated attack methods that target cloud-based systems across multiple organizations. These cybercriminals use...
The ShinyHunters threat group has expanded its extortion operations, now deploying sophisticated attack methods that target cloud-based systems across multiple organizations.
These cybercriminals use voice phishing and fake credential harvesting websites to steal login information from employees.
Once they gain access, they extract sensitive data from cloud software applications and use this information to demand ransom payments from victim companies.
The threat group creates realistic-looking phishing websites that mimic company login pages to capture single sign-on credentials and multi-factor authentication codes from unsuspecting employees.
The attackers typically call employees while pretending to be IT staff members and claim the company is updating security settings. They then direct workers to fraudulent websites designed to steal their login credentials.
This approach has proven effective because it combines human manipulation with technical deception.
Google Cloud analysts identified that the threat activity is being tracked under three separate threat clusters named UNC6661, UNC6671, and UNC6240.
The researchers discovered that these groups have expanded the number and types of cloud platforms they target, seeking more valuable data for their extortion schemes.
Recent incidents show the attackers are using aggressive tactics including harassment of victim employees and launching denial-of-service attacks against company websites.

The attacks do not exploit security vulnerabilities in software products or infrastructure. Instead, they succeed through social engineering techniques that trick people into providing their credentials voluntarily.
Security experts emphasize that organizations should adopt phishing-resistant authentication methods such as FIDO2 security keys or passkeys, which cannot be bypassed through social engineering tactics like traditional SMS or push-based authentication systems.
Attack Mechanism and Data Theft Operations
The threat actors register fake domains that impersonate legitimate corporate portals using patterns like companynamesso.com or companynameinternal.com to make their phishing sites appear authentic.
After obtaining employee credentials, the attackers register their own authentication devices to maintain persistent access to victim accounts.
They then systematically move through corporate cloud environments to steal data from platforms including SharePoint, Salesforce, DocuSign, and Slack.
The cybercriminals search specifically for documents containing terms like “confidential,” “internal,” “proposal,” and “vpn” within cloud applications.
In some cases, they enabled special tools like ToogleBox Recall within Google Workspace accounts to permanently delete security notification emails, preventing employees from discovering that unauthorized devices were accessing their accounts.
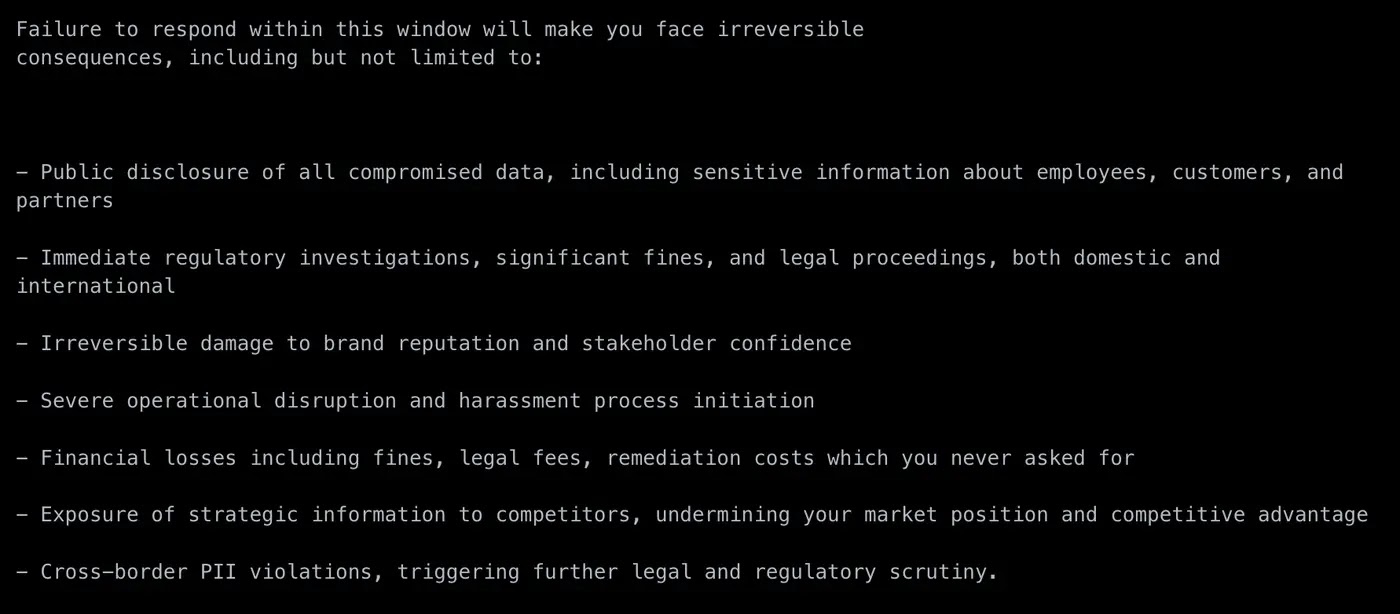
After stealing data, the attackers send extortion emails demanding Bitcoin payments within 72 hours and provide samples of stolen information hosted on file-sharing platforms to prove their claims.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.