Game-Theoretic AI Guides Cyber Attack & Defense Strategies
Researchers from Alias Robotics and Johannes Kepler University Linz have unveiled an innovative approach to automated penetration testing. This new method integrates artificial intelligence with game...
Researchers from Alias Robotics and Johannes Kepler University Linz have unveiled an innovative approach to automated penetration testing. This new method integrates artificial intelligence with game theory.
Led by Víctor Mayoral-Vilches, Mara Sanz-Gómez, Francesco Balassone, Stefan Rass, and their collaborators, the team introduced Generative Cut-the-Rope (G-CTR), a system designed to guide both attackers and defenders in modern cybersecurity operations.
The emergence of AI-driven penetration testing tools has revolutionized security assessment by executing thousands of actions per hour, far surpassing human capabilities.
However, these tools often produce overwhelming amounts of unstructured data that security teams struggle to interpret strategically.
The G-CTR framework addresses this critical gap by automatically transforming AI security logs into structured attack graphs and computing optimal strategies through game theory.
Víctor Mayoral-Vilches, Mara Sanz-Gómez, Francesco Balassone, Stefan Rass, and their collaborators noted that this closed-loop architecture fundamentally changes how security operations function.
The system operates in three coordinated phases: game-theoretic analysis that extracts attack graphs from AI logs and calculates Nash equilibria to identify optimal strategies, strategic interpretation that transforms equilibrium data into actionable guidance, and agent execution where AI systems perform security testing with continuous refinement.
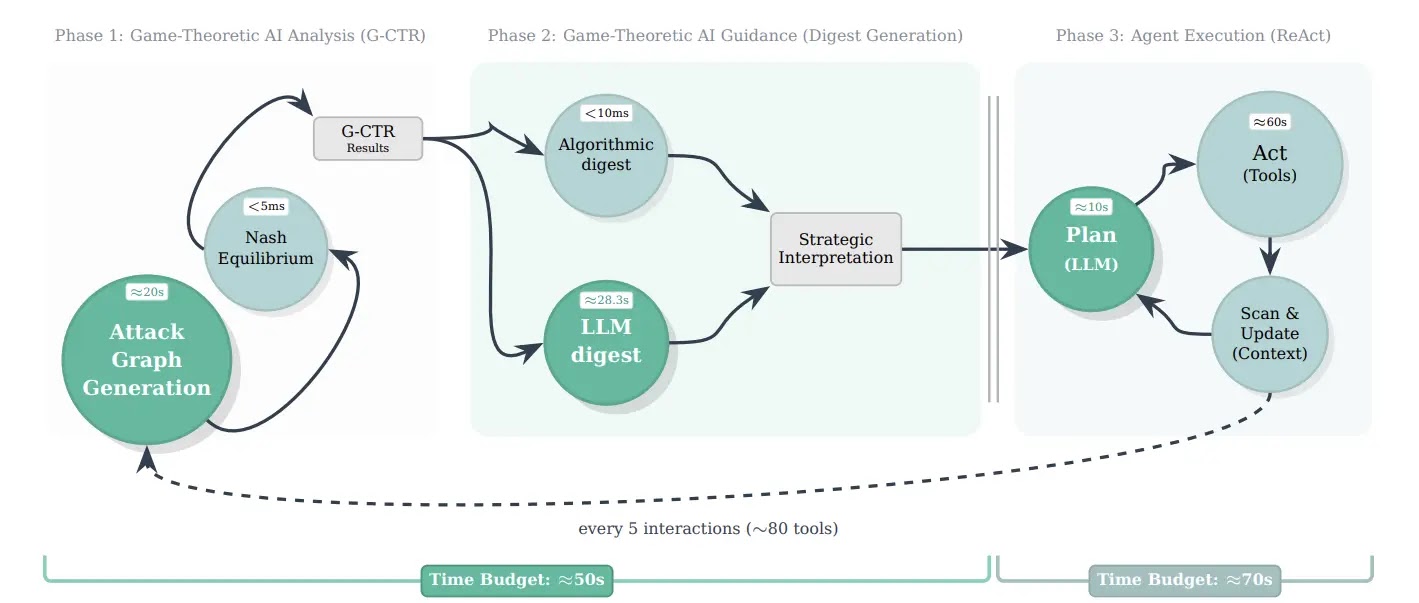
Unlike traditional approaches that require manual human analysis of security logs over hours or days, G-CTR completes the same task in seconds.
The technical foundation rests on effort-aware scoring that combines message distance, token complexity, and computational cost metrics.
This approach replaces classical probabilistic models with empirically grounded computational complexity measures suited for automatically generated graphs.
When security teams run the system on real exercises, results improve dramatically.
In a 44-run cyber-range benchmark targeting the Shellshock vulnerability, the framework doubled success probability from 20.0 percent to 42.9 percent while reducing cost-per-success by 2.7 times and decreasing behavioral variance by 5.2 times.
Striking breakthrough
The framework’s most striking breakthrough emerges in Attack and Defense exercises where red and blue teams operate simultaneously.
When both teams share a single G-CTR graph and context, creating what researchers call the Purple configuration, the system defeats independent dual guidance by 3.71 times.
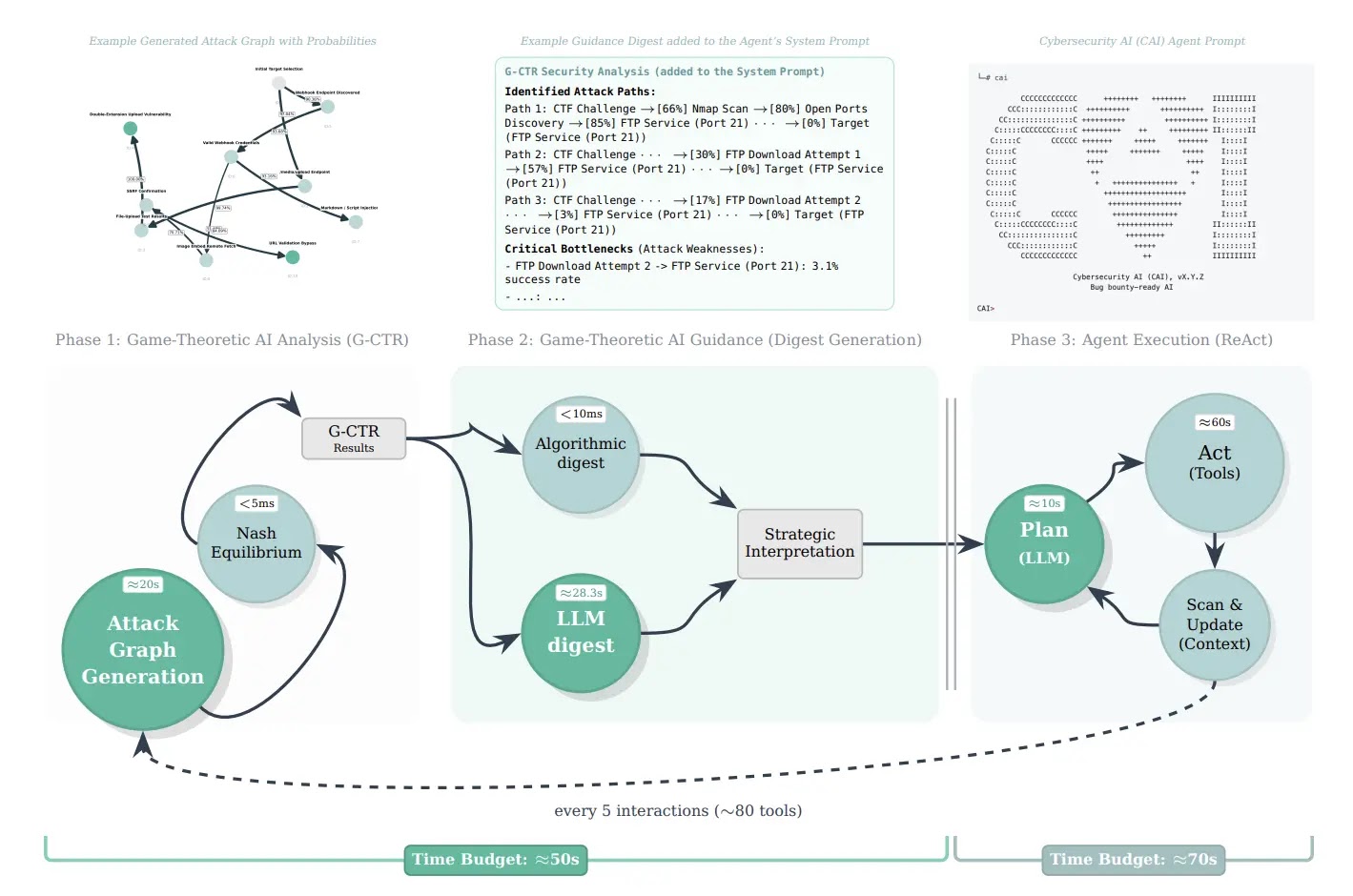
Across five real-world exercises, G-CTR generated attack graphs with 70-90 node correspondence to expert annotations while running 60-245 times faster than manual analysis and costing 140 times less to produce.
The innovation demonstrates that LLMs can automatically extract structured attack graphs from unstructured security logs, achieving substantial temporal and economic advantages.
This automation eliminates the primary bottleneck in applying game-theoretic analysis to actual security data.
By anchoring AI reasoning to external game-theoretic control signals derived from attack graphs and Nash equilibria, the system reduces hallucinations and maintains focus on statistically advantageous exploitation paths.
The research represents a concrete step toward cybersecurity superintelligence that not only discovers vulnerabilities but also reasons strategically about optimal exploitation sequences and critical defensive positions.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.