Fiber Optic Cables: Hidden Microphones Secretly Spy on
Standard fiber-to-the-home (FTTH) telecom cables can be secretly transformed into listening devices, researchers revealed at NDSS 2026. They demonstrated a covert acoustic eavesdropping attack that...
Standard fiber-to-the-home (FTTH) telecom cables can be secretly transformed into listening devices, researchers revealed at NDSS 2026. They demonstrated a covert acoustic eavesdropping attack that repurposes these ordinary fiber optic lines into passive, undetectable microphones. Crucially, these modified cables are invisible to RF scanners and immune to ultrasonic jammers.
Security researchers from The Hong Kong Polytechnic University, The Chinese University of Hong Kong, and the Technological and Higher Education Institute of Hong Kong have disclosed a critical side-channel attack that turns ordinary fiber optic internet cables into hidden microphones capable of capturing private conversations.
The research, titled “Hiding an Ear in Plain Sight: On the Practicality and Implications of Acoustic Eavesdropping with Telecom Fiber Optic Cables,” was presented at the Network and Distributed System Security (NDSS) Symposium 2026 held in San Diego, California.
Fiber Optic Cables Turned Into Microphones
Fiber optic cables have long been considered inherently secure communication channels resistant to RF emissions and electromagnetic interference. But the research shatters that assumption by exploiting a fundamental physical property: optical fibers are sensitive to acoustic vibrations.
When sound waves reach the fiber, they cause microscopic structural deformations in the cable. These deformations produce measurable phase shifts in laser light traveling through the fiber.
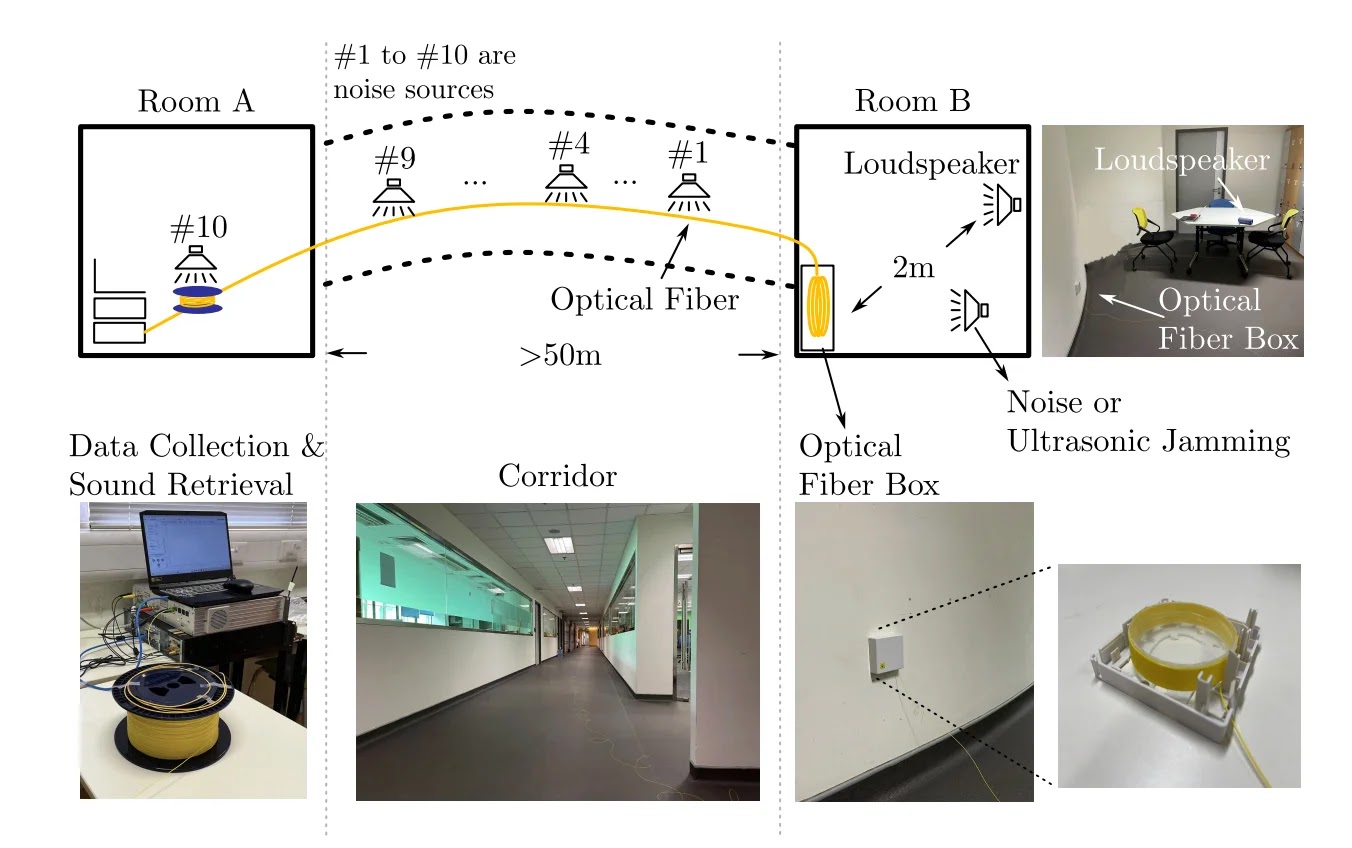
By monitoring these shifts using a commercially available Distributed Acoustic Sensing (DAS) system connected to just one end of the cable, an attacker can reconstruct the original sound wave from the other end, even across distances exceeding 50 meters.
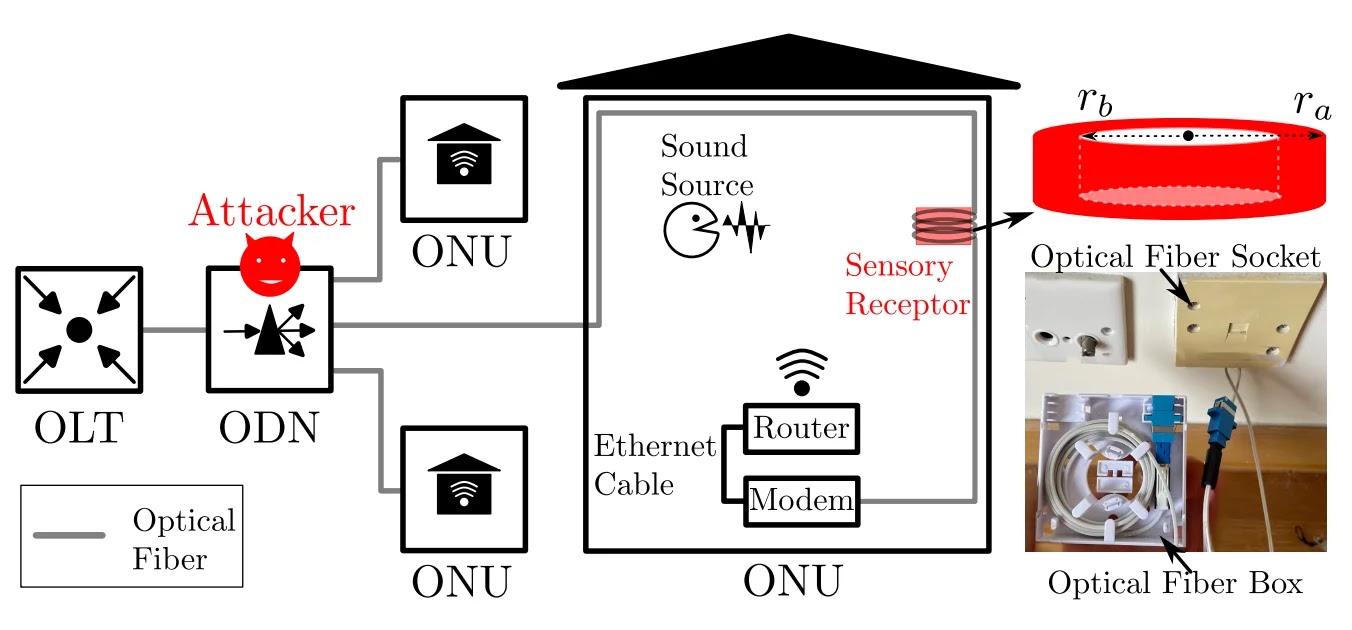
Because standard fiber alone is not sensitive enough to capture airborne speech, the researchers engineered a custom “Sensory Receptor” — a hollow PET (polyethylene terephthalate) cylinder, 65mm in diameter, with 15 meters of optical fiber tightly wound around it.
The cylinder amplifies acoustic pressure fluctuations and converts them into longitudinal strain along the fiber, dramatically boosting sound capture performance.
Critically, this device can be disguised as an ordinary optical fiber box, the same type of enclosure routinely installed in homes and offices during FTTH deployments — making it virtually indistinguishable from legitimate networking equipment.
The attack requires physical access to both the victim’s premises (ONU) and the Optical Distribution Network (ODN). This is a realistic threat vector.
FTTH deployments regularly involve ISP technicians, subcontractors, or third-party service providers physically accessing fiber endpoints during installation, upgrades, or troubleshooting — all scenarios where a rogue insider or an attacker impersonating one could plant the sensory receptor undetected.
The research team’s lab and real-world office experiments produced striking results:
- Speech recovery at 2 meters achieved a Word Error Rate (WER) below 20%, meaning over 80% of spoken content was successfully transcribed using AI speech recognition models including OpenAI Whisper and NVIDIA Parakeet.
- Indoor localization of a speaker’s position was accurate to an average of 77 centimeters within a room.
- Sound event detection (identifying activities like typing, coughing, or alarms) reached 83% accuracy after fine-tuning deep learning models on recovered audio.
- In a real office scenario spanning two rooms separated by 50+ meters of fiber cable, the best placement (fiber box under a desk) yielded a mean WER of just 9% — a near-perfect transcript.
Unlike hidden microphones, fiber optic sensors operate without electricity and emit no RF signatures, making them completely invisible to standard Technical Surveillance Countermeasures (TSCM) sweeps or RF bug detectors.
More alarmingly, when researchers tested commercial ultrasonic jammers, a common defense against covert microphones, the optical-fiber-based system showed no significant degradation in speech recognition performance, even with the jammer placed as close as 10 centimeters away. Conventional microphones were fully disrupted.
Mitigations
The researchers recommend several countermeasures to reduce exposure:
- Install polished fiber connectors to introduce Fresnel reflections that create dead zones in DAS detection.
- Deploy optical isolators on transmission channels to prevent Rayleigh backscatter from returning to potential attackers.
- Minimize excess fiber slack inside rooms and prevent cables from looping around or contacting resonant surfaces like desks or walls.
- Add sound-proofing materials to walls and ceilings where fiber cables run.
The findings carry especially serious implications for corporate boardrooms, government facilities, and diplomatic environments, where the attack’s passive, RF-silent, and jammer-resistant nature makes it a strategically potent tool for adversaries seeking sensitive intelligence without triggering conventional detection systems.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.