Fake Proton VPN & Gaming Mods Spread NWHStealer Sites Windows
NWHStealer, a recently identified information-stealing malware, is actively compromising Windows systems through a sophisticated campaign. This threat propagates by leveraging fake VPN websites,...
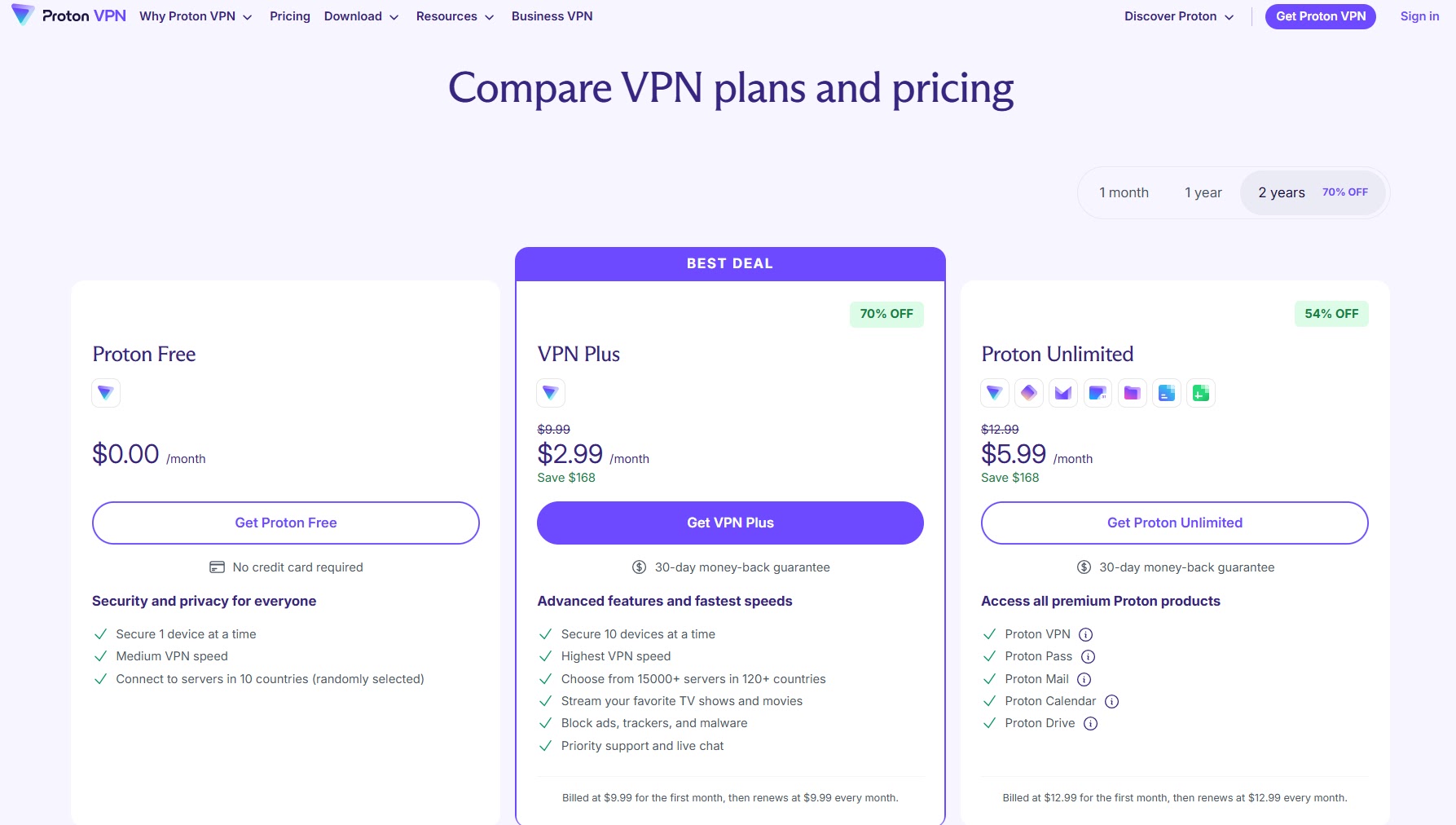
NWHStealer, a recently identified information-stealing malware, is actively compromising Windows systems through a sophisticated campaign. This threat propagates by leveraging fake VPN websites, gaming modifications, and hardware utility tools as lures.
The attackers are not relying on spam emails or obvious phishing tricks. Instead, they are placing malware inside files that people actively search for and download on their own, making detection far harder than in most campaigns.
The campaign covers a wide range of distribution methods. NWHStealer spreads through fake websites that impersonate trusted services, code-hosting platforms like GitHub and GitLab, file-sharing sites such as MediaFire and SourceForge, and even gaming and security-related YouTube videos carrying malicious links.
The malware disguises itself as software people genuinely need, including VPN installers, hardware diagnostic tools like OhmGraphite, Pachtop, and Sidebar Diagnostics, as well as popular gaming cheats and mods such as Xeno.
This broad reach across trusted platforms is what makes this campaign particularly dangerous.
Malwarebytes analysts identified and tracked multiple active campaigns distributing NWHStealer, noting that the stealer can be loaded through self-injection or injected into legitimate Windows processes like RegAsm, which is Microsoft’s Assembly Registration Tool.
Researchers at Malwarebytes observed that additional wrappers including MSI packages and Node.js are often used as the initial loader before the actual payload is delivered.
According to the report authored by Malware Research Engineer Gabriele Orini, once the malware successfully lands on a victim’s system, it can collect browser data, saved passwords, and cryptocurrency wallet information that attackers may use to take over accounts, drain funds, or carry out further attacks.
The immediate consequences for victims are serious. NWHStealer enumerates more than 25 folders and registry keys tied to cryptocurrency wallets and targets browsers including Edge, Chrome, Opera, Brave, Chromium, and Firefox to pull saved credentials and session data.
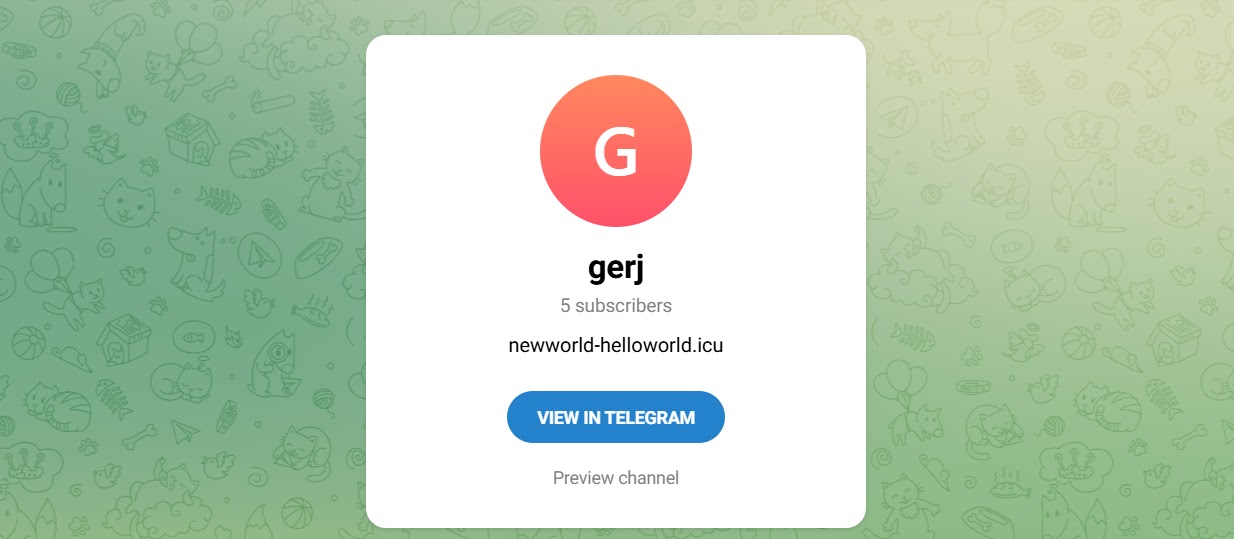
Stolen information is encrypted using AES-CBC before being sent to the attacker’s command-and-control server. If the primary server goes offline, the malware retrieves a fresh C2 domain through a Telegram-based dead drop, ensuring the operation stays connected even if infrastructure changes.
One unusual distribution method stands out in this campaign. A free web hosting provider at onworks[.]net, ranked within the top 100,000 websites globally, was found hosting malicious ZIP archives in its download section.
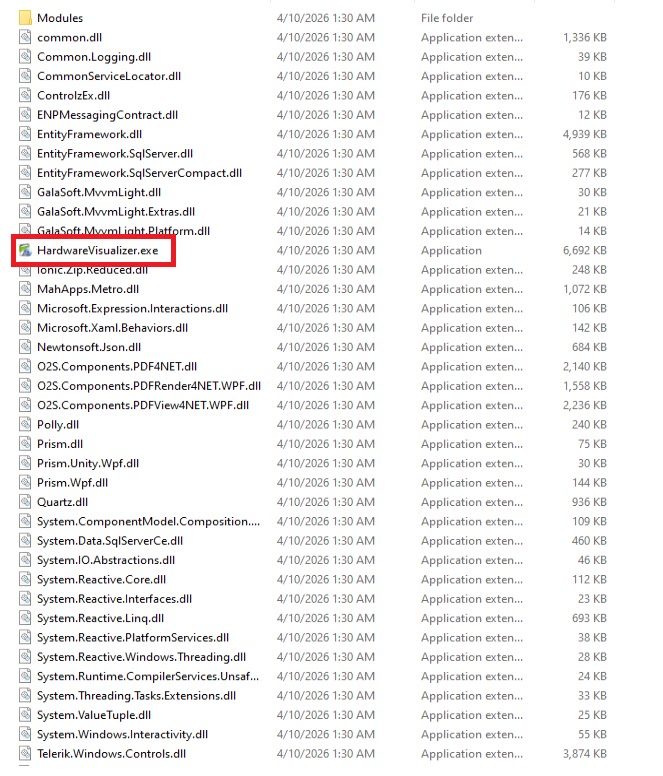
Files bearing names like HardwareVisualizer_1.3.1.zip and Sidebar Diagnostics-3.6.5.zip appear completely legitimate but carry embedded malicious code that starts the infection chain the moment the user runs the executable inside.
Inside the Infection Mechanism
The way NWHStealer reaches its final stage is technically layered and built to avoid detection at every step. In the first observed case, the malicious code is embedded directly inside a legitimate-looking executable such as HardwareVisualizer.exe.
When launched, this loader performs several operations in sequence: it checks for analysis tools and shuts down if any are found, uses a custom decryption function to process strings, resolves Windows API functions through LoadLibraryA and GetProcAddress, and finally decrypts and loads the next stage payload using AES-CBC via BCrypt APIs.
Junk code is deliberately packed into the loader to slow down analysis and confuse automated tools.
In the second observed case, fake Proton VPN websites deliver a malicious ZIP that uses DLL hijacking to execute the stealer. Here, a file appearing to be a WinRAR executable carries a malicious library named WindowsCodecs.dll, which decrypts two embedded resources.
One of those resources is a second-stage DLL called runpeNew.dll, which performs process hollowing by injecting the final payload into a running Windows process like RegAsm.exe using low-level APIs including NtProtectVirtualMemory and NtAllocateVirtualMemory.
Once inside the system, the injected DLL uses PowerShell to create hidden directories in LOCALAPPDATA, adds those directories to Windows Defender exclusions, and forces a Group Policy update to lock in its changes.
Scheduled tasks are also created to run the payload at user logon with elevated privileges, giving the malware a durable foothold.
To bypass User Account Control, the stealer uses a known CMSTP UAC bypass technique, generating a random .inf file in the temp folder and using cmstp.exe to elevate privileges without triggering a visible prompt.
Malwarebytes researchers advise users to apply the following precautions to reduce exposure to this campaign:
- Download software only from official, verified websites and avoid third-party download mirrors.
- Exercise caution with any files sourced from GitHub, SourceForge, or file-sharing platforms unless the publisher is fully trusted and verified.
- Always check file signatures and publisher details before running any downloaded executable.
- Do not download tools or software through links posted in YouTube video descriptions or comments.
- Verify the integrity of compressed archives by checking the signature and version information of any software they contain before extraction.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.