Fake Dropbox Phishing Attack Steals User Login Credentials
A dangerous phishing campaign is actively underway, designed by cybercriminals to steal user login credentials. This sophisticated campaign leverages convincing impersonations of Dropbox to trick...
A dangerous phishing campaign is actively underway, designed by cybercriminals to steal user login credentials. This sophisticated campaign leverages convincing impersonations of Dropbox to trick victims.
This attack uses a multi-stage approach to bypass email security checks and content scanners.
The threat actors exploit trusted cloud platforms and harmless-looking PDF files to create a deception chain that leads victims to a fake login page designed to steal their credentials.
The attack starts with a legitimate-looking business email that appears related to procurement processes.
These emails contain a PDF attachment and ask recipients to review request orders by signing in with their credentials.
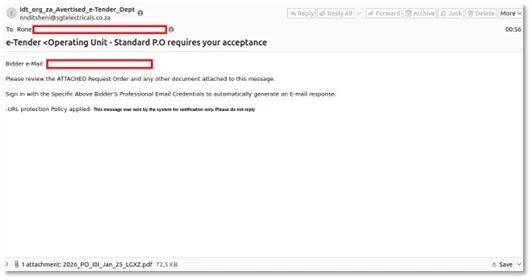
What makes this campaign effective is that the email body contains no malicious links, allowing it to pass authentication checks like SPF, DKIM, and DMARC without raising red flags.
Once the victim opens the PDF attachment, they encounter an embedded link that directs them to another PDF hosted on Vercel Blob storage, a legitimate cloud infrastructure service.

This staging layer exploits the trust users place in well-known platforms. Forcepoint analysts identified that the PDF uses specialized techniques like FlateDecode compression and AcroForm objects to hide clickable elements while appearing harmless to scanning tools.
The cloud-hosted document then redirects victims to a fraudulent website that impersonates Dropbox with a familiar login interface.
The fake page mimics the authentic Dropbox design to convince users that they need to enter credentials to access important documents.
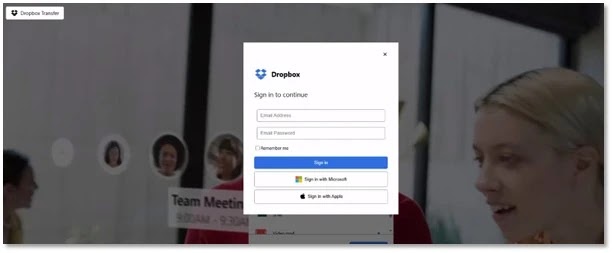
When victims input their email and password, the information gets captured immediately and transmitted to attackers through Telegram infrastructure.
How the Credential Theft Mechanism Works
The fake Dropbox page contains hidden JavaScript code that performs several malicious functions.
When a victim enters their credentials, the script validates the email format and collects the password without any minimum length requirement.
It then gathers additional information by fetching the victim’s IP address and geo-location details including city, region, country, and internet service provider through external APIs.
All this collected data gets packaged into a message and sent to a Telegram bot using a hardcoded bot token and chat ID.
The script simulates a login process with a five-second delay before displaying an error message, making victims believe they simply mistyped their credentials while attackers already have the stolen information.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.