Discord Abuse: Clipboard Hijacker Steals Crypto Wallet
A new clipboard hijacker is quietly draining cryptocurrency from gamers and streamers by abusing trust inside Discord communities. The campaign centers on a malicious Windows program shared as a...
A new clipboard hijacker is quietly draining cryptocurrency from gamers and streamers by abusing trust inside Discord communities.
The campaign centers on a malicious Windows program shared as a supposed streaming or security tool. Once installed, it silently watches the user’s clipboard, waiting for the moment they copy a crypto wallet address.
When the victim pastes it into an exchange, wallet, or payment field, the malware swaps it with an attacker-controlled address, redirecting the funds without leaving obvious traces.
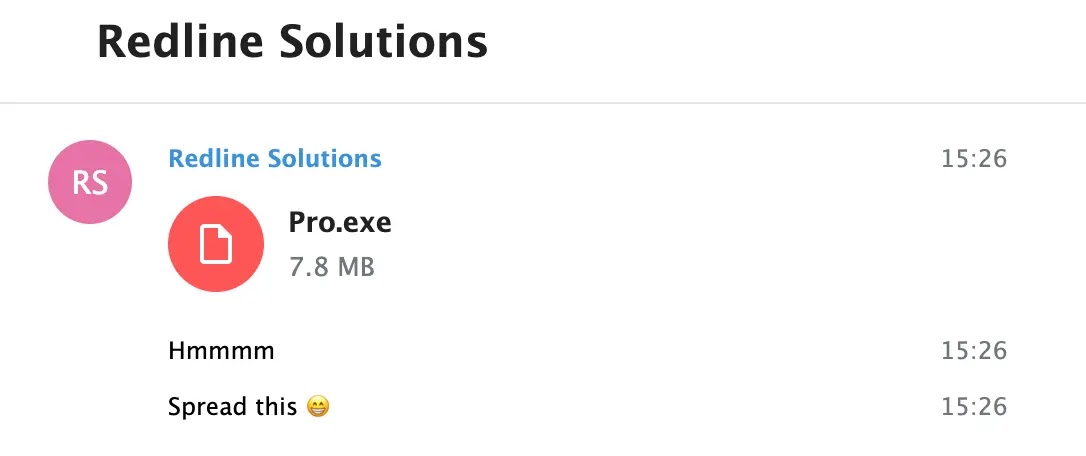
The threat actor, tracked as “RedLineCyber,” focuses on Discord servers linked to gaming, gambling, and cryptocurrency streaming.
They build rapport with server members, present themselves as tool developers, and privately share a file named Pro.exe or peeek.exe.
Victims are told the tool will help them manage or protect their wallet addresses during live sessions, making it appear useful rather than suspicious.
Behind this friendly pitch is a focused theft operation that can quietly empty transactions in a single mistyped paste.
CloudSEK analysts uncovered this operation while monitoring underground communities and Discord channels used by cybercriminals.
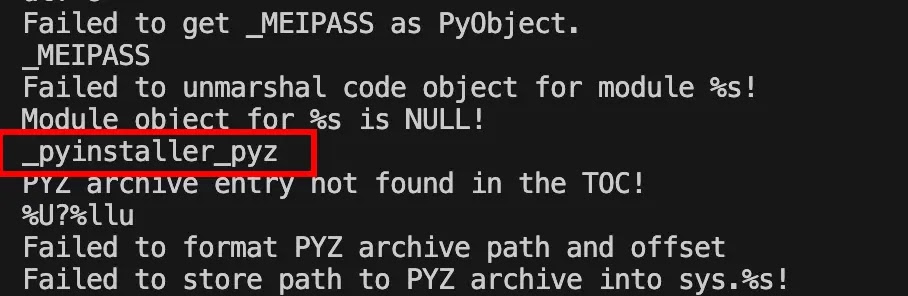
During these human intelligence operations, researchers identified the fake “RedLine Solutions” persona and traced the malware back to a Python-based executable packed with PyInstaller.
Their analysis confirmed that the program does not behave like classic information-stealing malware, but instead narrows its activity to one task: manipulating clipboard data linked to popular cryptocurrencies.
The impact of this campaign is significant because it targets users at the exact point where human attention is weakest. Many streamers and frequent traders copy and paste long wallet strings without double-checking every character.
By operating without command-and-control traffic and using minimal system resources, the malware can remain active for long periods, waiting for high-value transfers.
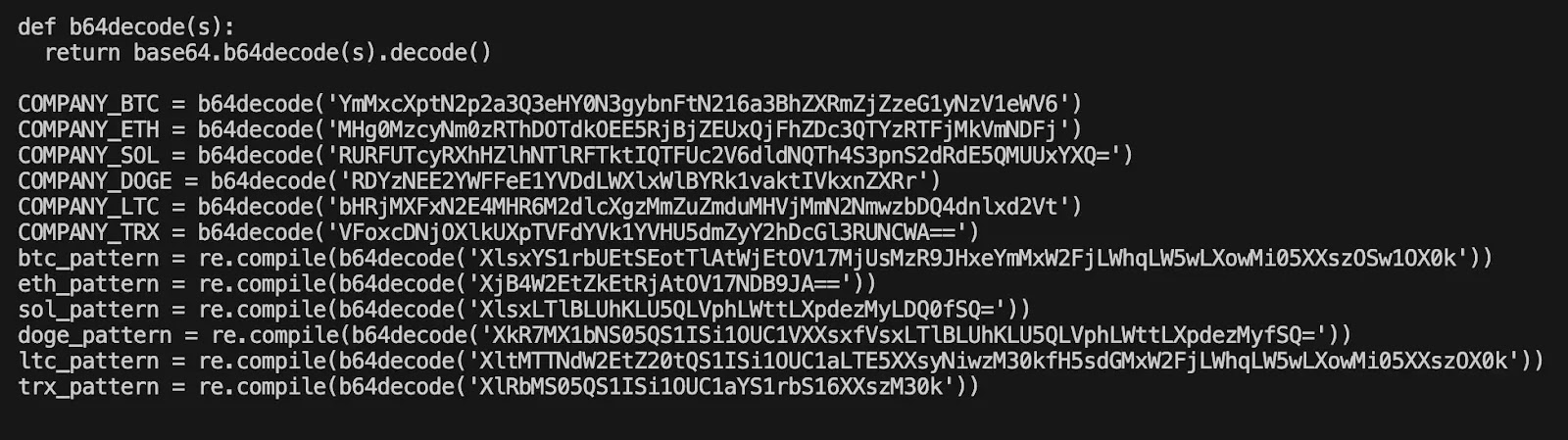
Blockchain traces linked to the attacker’s embedded wallet addresses already show stolen funds across Bitcoin, Ethereum, Solana, Dogecoin, Litecoin, and Tron.
Infection Mechanism and Clipboard Hijacking Logic
Once a victim launches Pro.exe, the malware creates a folder named CryptoClipboardGuard inside the Windows %APPDATA% directory and registers itself in the Run key of the current user’s registry.
This ensures it starts automatically whenever the system boots, persisting in the background without any visible window.
The executable bundles its own Python runtime and obfuscated bytecode, enabling it to run even on systems without Python installed.
It then enters a tight loop, checking the clipboard roughly three times per second.
Every time the clipboard content changes, the malware scans it against base64-encoded regular expressions that match wallet formats for major cryptocurrencies.
If it detects a valid address, it immediately overwrites the clipboard with a preset attacker wallet for that coin and records the swap in an activity.log file within %APPDATA%CryptoClipboardGuard.
Because the address change happens between copy and paste, most victims never notice the replacement until their funds arrive in the wrong wallet — and by then, the transfer is irreversible.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.