DesckVB RAT Evades Detection with Ob Uses Obfuscated
A new Remote Access Trojan (RAT), DesckVB, has been observed targeting systems in 2026. This threat leverages obfuscated JavaScript and a fileless .NET loader, enabling it to remain hidden from...
A new Remote Access Trojan (RAT), DesckVB, has been observed targeting systems in 2026. This threat leverages obfuscated JavaScript and a fileless .NET loader, enabling it to remain hidden from traditional security tools.
The malware gives attackers full remote control over a victim’s machine, making it a serious threat for individuals and organizations alike.
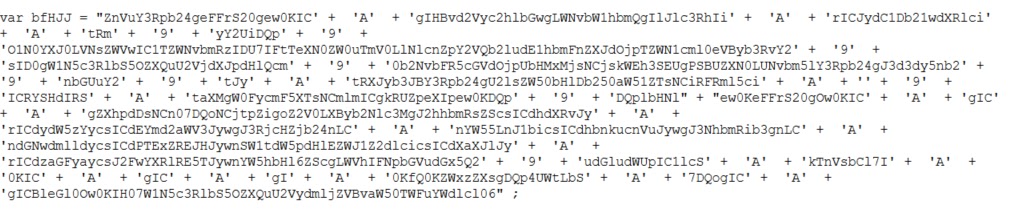
DesckVB RAT starts its infection chain with a heavily obfuscated JavaScript file that, once executed, silently drops a PowerShell script into the C:UsersPublic directory on the target system.
The JavaScript replicates its code into PowerShell and text files, giving the malware multiple ways to run. What makes this threat particularly dangerous is that it avoids writing most of its core components to disk, making it much harder for conventional antivirus tools to catch it.
Point Wild analysts from the LAT61 Threat Intelligence Team identified and examined DesckVB RAT in detail, uncovering how it uses layered obfuscation to hide its true purpose at every stage of execution.
Their research found that the malware combines Base64 encoding with URL string reversal to conceal its command-and-control (C2) server addresses, a tactic designed to trick automated scanning tools.
The overall structure of the malware suggests it was built with a clear understanding of how modern security defenses work.
Once fully deployed, DesckVB RAT loads a .NET assembly directly into memory using .NET reflection techniques, bypassing the need to leave any files on the hard drive.
This in-memory execution method allows the malware to run its harmful routines without triggering many standard file-based detection systems.
At runtime, the malware activates several harmful capabilities, including keylogging, webcam access, antivirus detection evasion, and encrypted communication with its C2 server.
The overall impact of DesckVB RAT is broad and concerning. Attackers who deploy it can steal sensitive information, monitor user activity in real time, and maintain long-term access to a compromised system without raising immediate alarms.
Its use of encrypted HTTPS traffic over port 443 allows it to blend in with normal internet activity, making network-level detection just as difficult.
The Fileless Infection Chain
The most notable aspect of DesckVB RAT is how it moves through its infection stages without relying on traditional file drops. The malware’s flow begins with the JavaScript file, acting as the first entry point.
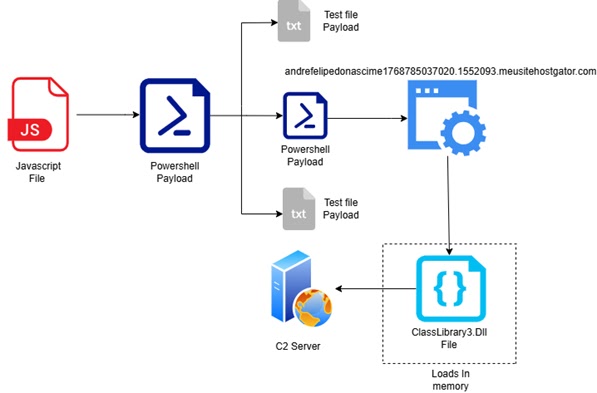
This file is heavily obfuscated and drops a PowerShell file directly into C:UsersPublic, keeping its activities within commonly overlooked system folders.
The PowerShell script first checks for internet connectivity by pinging Google, then attempts to connect to a malicious external domain. The C2 domain is hidden using Base64 encoding combined with string reversal.
The malware uses the legitimate Windows tool InstallUtil.exe to execute its payload — a known technique for bypassing application control policies.
From there, the script loads ClassLibrary3.dll directly into memory and invokes the obfuscated method prFVI, which then loads ClassLibrary1.dll.
The Execute method within this loader uses CreateProcessA to spawn a new process in a suspended state before injecting the malicious payload.
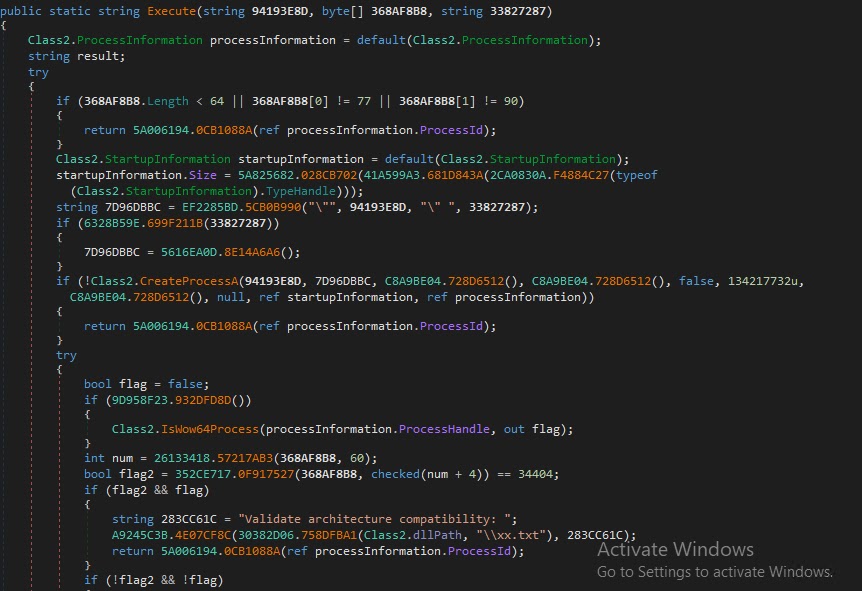
This process injection approach allows the malware to hide inside trusted processes and avoid drawing attention.
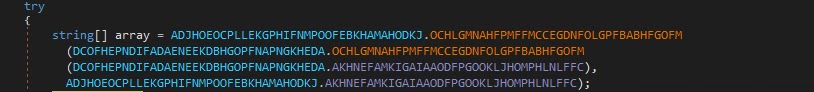
The final payload, Microsoft.exe, carries encoded string arrays that hold a hidden runtime configuration. Once active, it drops Keylogger.dll directly into memory and begins C2 communication over manikandan83.mysynology.net on port 7535, resolving to IP 45.156.87.226.
Network captures confirm the malware transmits its module names and internal activity to its remote server.
Security teams should watch for unusual PowerShell execution, unexpected use of InstallUtil.exe, and outbound connections to unknown domains or IPs.
Blocking script execution from C:UsersPublic and enabling detailed PowerShell script logging are practical first steps to catching this threat early.
Keeping endpoint protection software current also remains a critical defense, as detection tools have already shown the ability to flag key components of this malware.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.