Cybercriminals Use IRS, Tax Lures to Push Malware Abuse Filing
Each tax season predictably triggers a surge of phishing attacks; however, 2026 has already demonstrated a significantly larger and more coordinated campaign than in prior years. Cybercriminals are...
Each tax season predictably triggers a surge of phishing attacks; however, 2026 has already demonstrated a significantly larger and more coordinated campaign than in prior years.
Cybercriminals are actively impersonating the Internal Revenue Service (IRS), national tax authorities, and company HR departments to trick people into installing malware or handing over login credentials.
Over a hundred campaigns using tax-related lures have been recorded so far this year, delivering everything from malware to remote access tools and credential-stealing pages.
The range of tactics in these campaigns is wider than before. Attackers are spoofing emails about expired tax documents, IRS filing notices, W-2 form requests from fake HR teams, and even W-8BEN filings for non-U.S. taxpayers.
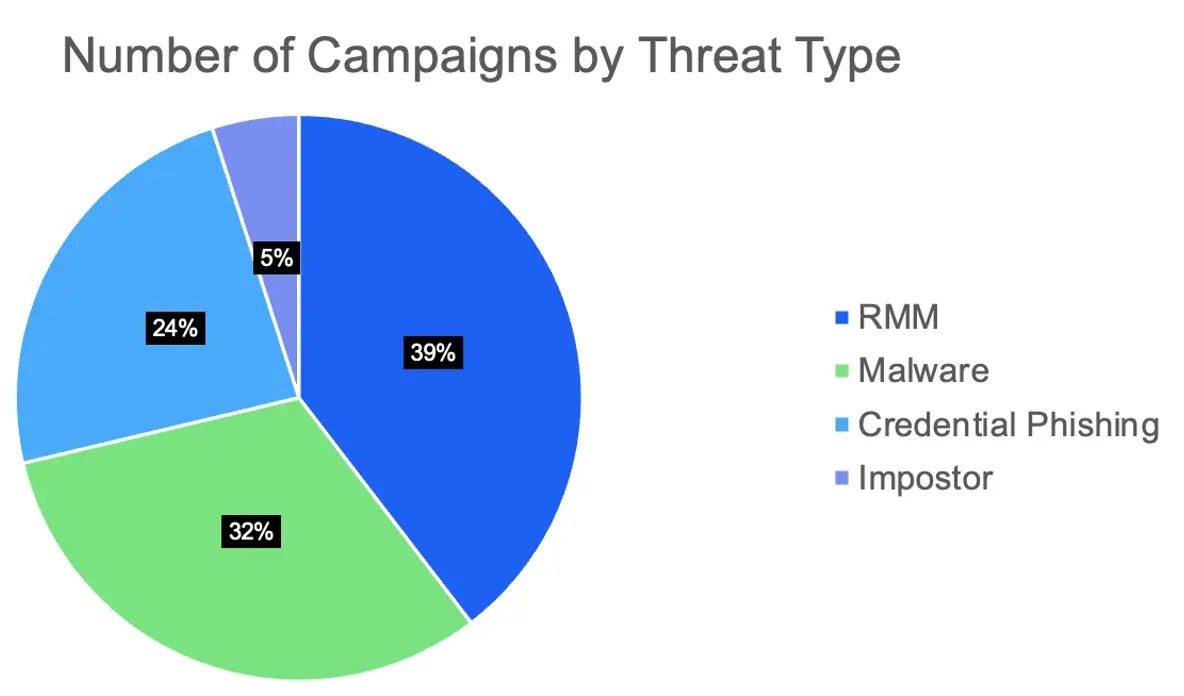
Malware and remote monitoring and management (RMM) payloads account for the bulk of threats delivered through tax-themed emails this year.
Campaigns have targeted users mainly in the United States, but also in Canada, Australia, Switzerland, and Japan, with email volumes ranging from a few targeted messages to tens of thousands.
Proofpoint researchers identified over a dozen IRS-impersonation RMM campaigns since January 2026 and flagged two specific threat actor groups — TA4922 and TA2730 — each running organized operations with clear financial objectives.
Researchers noted that 2026 shows more RMM payloads than past tax seasons, with activity from newly identified actors and a broader variety of social engineering lures than previously observed.
Abusing legitimate RMM software has become a go-to move for these actors. Tools like N-able, Datto, RemotePC, Zoho Assist, and ScreenConnect are trusted by enterprise security systems because they are legitimate, digitally signed applications — making them hard to detect as threats.
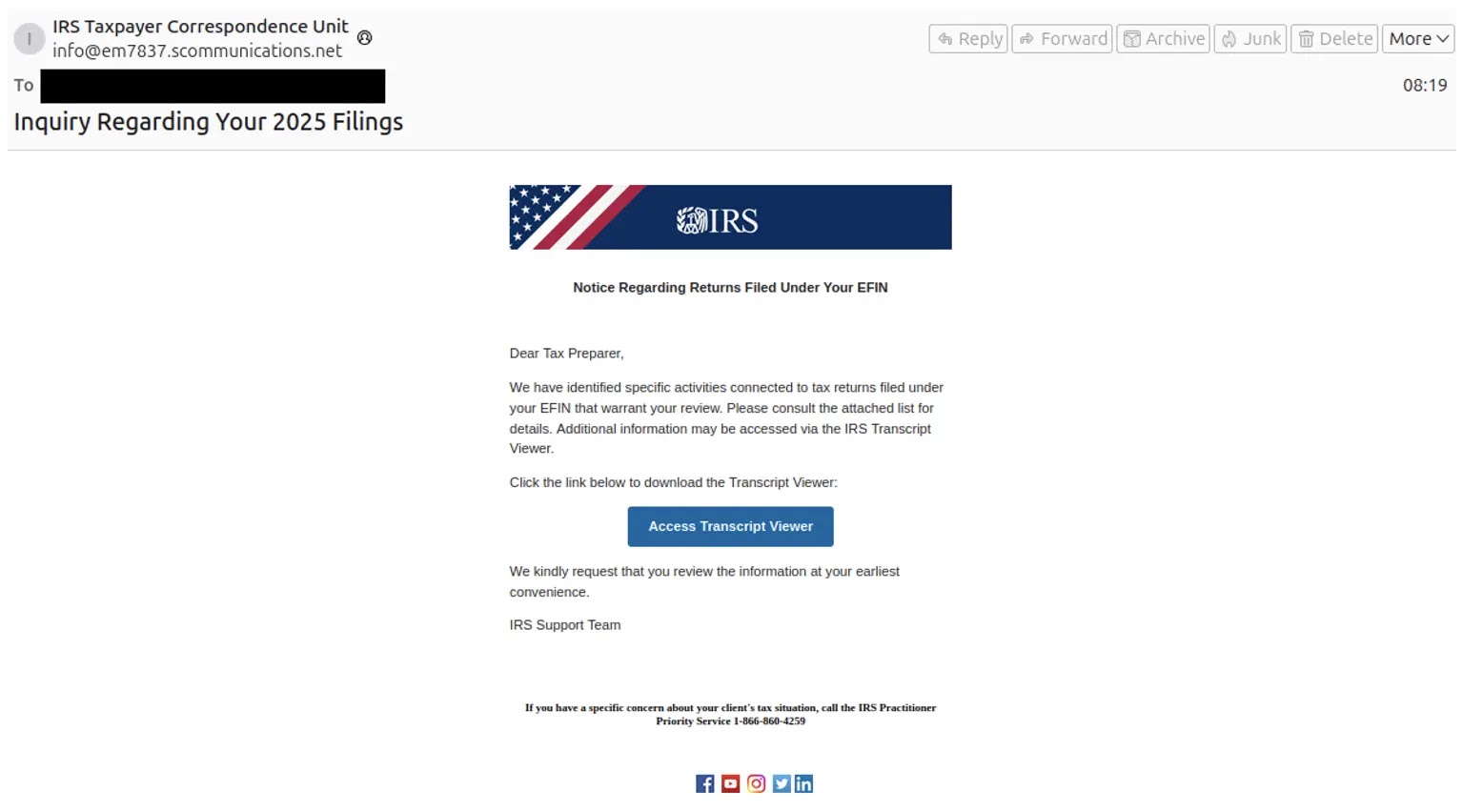
On February 5, a campaign impersonating the IRS sent emails with a fake “Transcript Viewer” button, which linked to a Bitbucket-hosted executable that silently installed N-able RMM on the victim’s machine.
The attacker also included a real IRS phone number in the email to make the message look official.
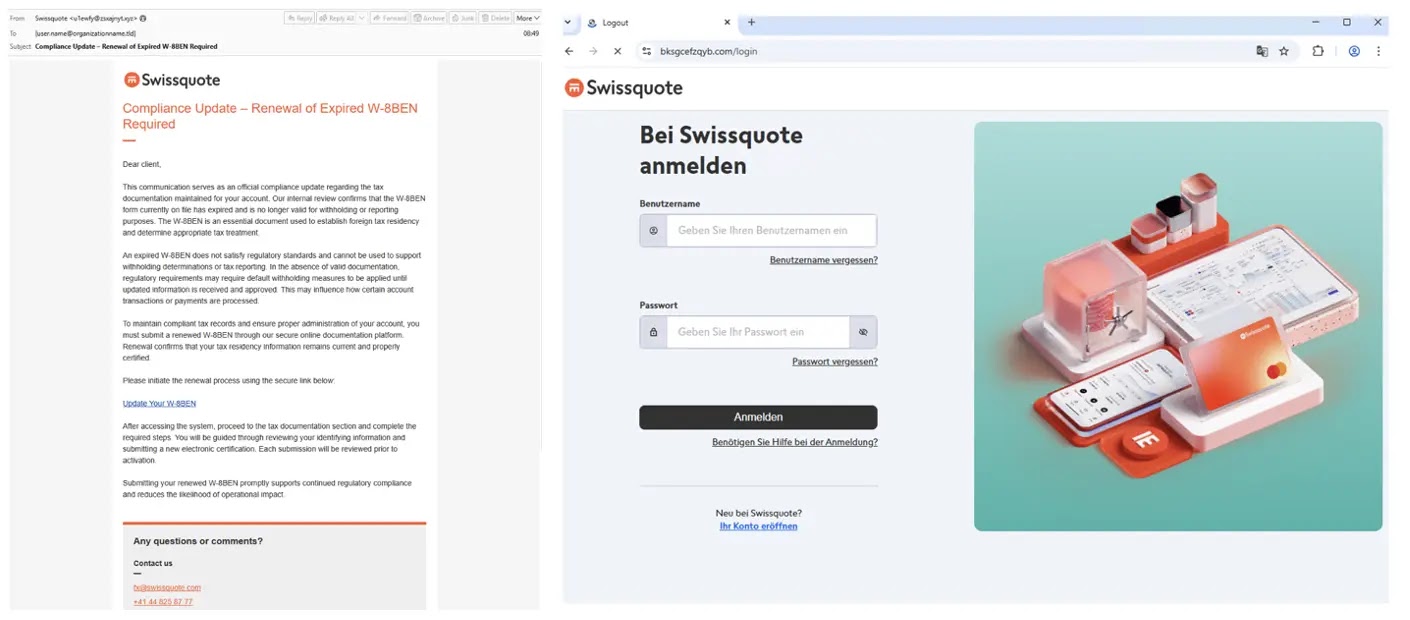
Separately, TA2730 — a credential phishing group tracked by Proofpoint since June 2025 — ran campaigns impersonating investment firms and asking targets to update W-8BEN tax forms.
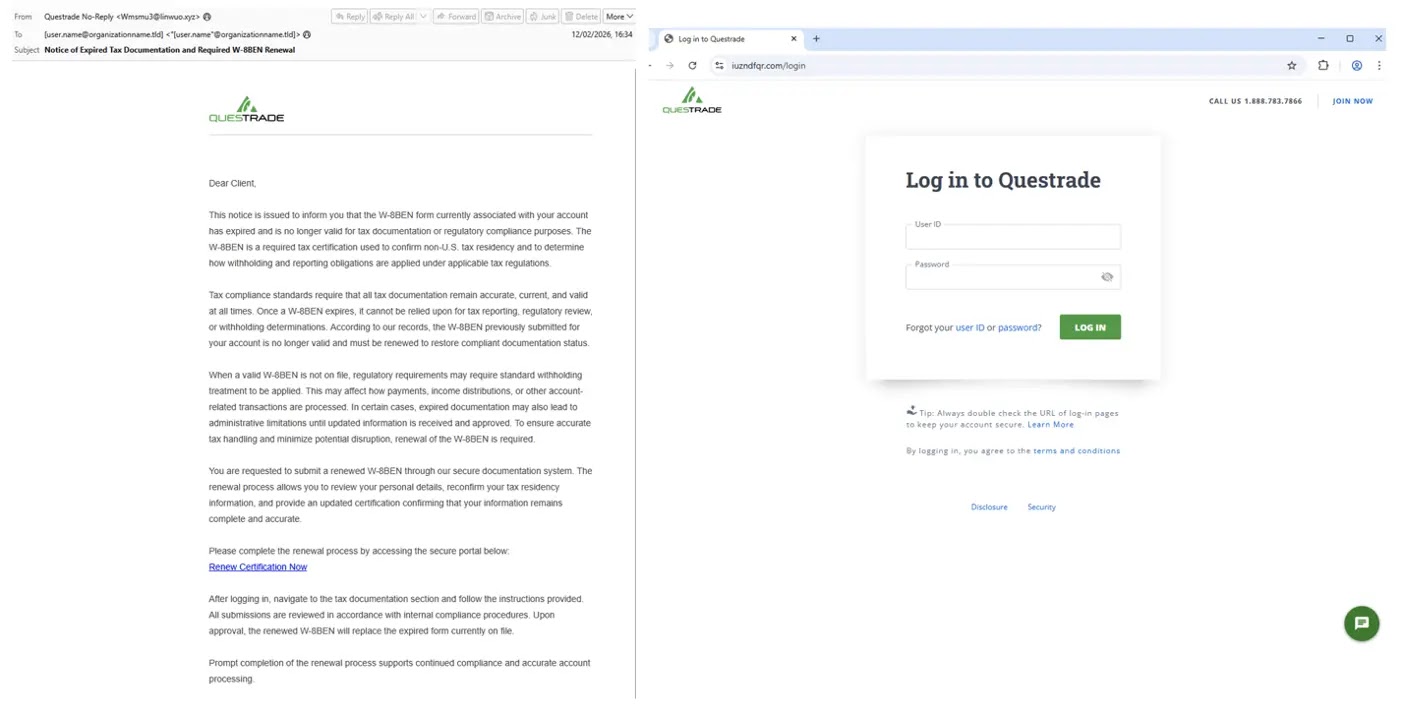
In February 2026, the actor impersonated Swissquote in Switzerland and Questrade in Canada, directing victims to fake login pages built to steal account credentials for financial gain.
TA4922’s Multi-Step Social Engineering Approach
Among the threat actors identified this year, TA4922 stands out for its deliberate, multi-stage attack chain. Tracked by Proofpoint since spring 2025, this financially motivated group is believed to be based in East Asia and is likely Chinese-speaking.
Its primary goal is gaining remote access to victim systems for fraud, data theft, or selling that access to other criminals.
TA4922 primarily delivers malware from the Winos4.0 ecosystem — also known as ValleyRAT — using a combination of loaders and information stealers.
What makes this actor particularly dangerous is its two-phase approach. The group begins by sending an impersonation email posing as a tax authority claiming the recipient has unresolved tax obligations and requesting a mobile phone number to continue discussions.
Once that private channel is established, the actor escalates by pretending to be company finance leadership before delivering malicious files or links outside of email.

In early March 2026, a related campaign spoofed the Inland Revenue Department, leading victims to download an information stealer that remains under active investigation by Proofpoint researchers.
Organizations and employees can take clear steps to protect themselves. Security teams should enforce allow-listing policies to ensure that only approved RMM tools can run on corporate networks, reducing the risk of unauthorized remote access software going undetected.
Employees need regular training that covers tax-season phishing techniques and teaches them to question emails requesting personal contact details or prompting action on tax filings through external links.
Any unsolicited message from a supposed tax authority or HR contact should always be verified through official channels before any action is taken.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.