Copyright-Themed Lures Deliver Multi-Stage PureLog Stealer in New
A new malware campaign is deploying PureLog Stealer, a potent information-stealing malware, against organizations in the healthcare, government, education, and hospitality sectors. Attackers are...
A new malware campaign is deploying PureLog Stealer, a potent information-stealing malware, against organizations in the healthcare, government, education, and hospitality sectors. Attackers are using cleverly disguised
PureLog Stealer is an infostealer known for harvesting browser credentials, cryptocurrency wallet data, browser extension data, and general system information.
It is classified as a low-cost, easy-to-use tool, which means even less-skilled threat actors can deploy it.
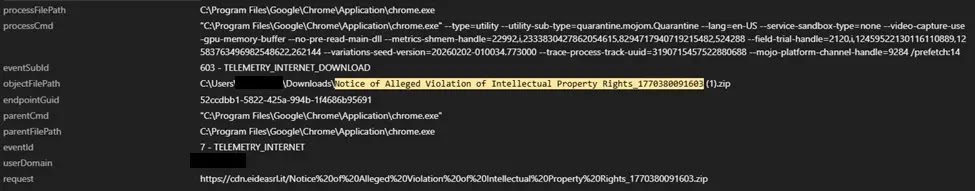
The campaign uses phishing emails with malicious download links — rather than direct attachments — to deliver language-specific lures, with German-language variants targeting Germany and English-language versions targeting Canada and other regions.
Trend Micro researchers identified that the campaign does not rely on software vulnerabilities or exploits. Instead, it depends entirely on social engineering, convincing users to manually run a file disguised as a copyright complaint.
The malicious executable carries names like “Documentation on Intellectual Property Rights Violations.exe,” making it appear genuine to an unsuspecting recipient.
This approach makes the campaign particularly dangerous because standard patch management alone cannot stop it.
The campaign has been most active against organizations in Germany and Canada, with additional victims observed in the United States and Australia.
Industries targeted include healthcare, government, hospitality, and education — sectors that often deal with legal notices and compliance documents, making the copyright lure format highly believable.
The selective targeting and localized delivery suggest a structured operation rather than a random mass spam campaign.
What makes this threat stand out is the level of technical sophistication woven throughout its delivery chain.
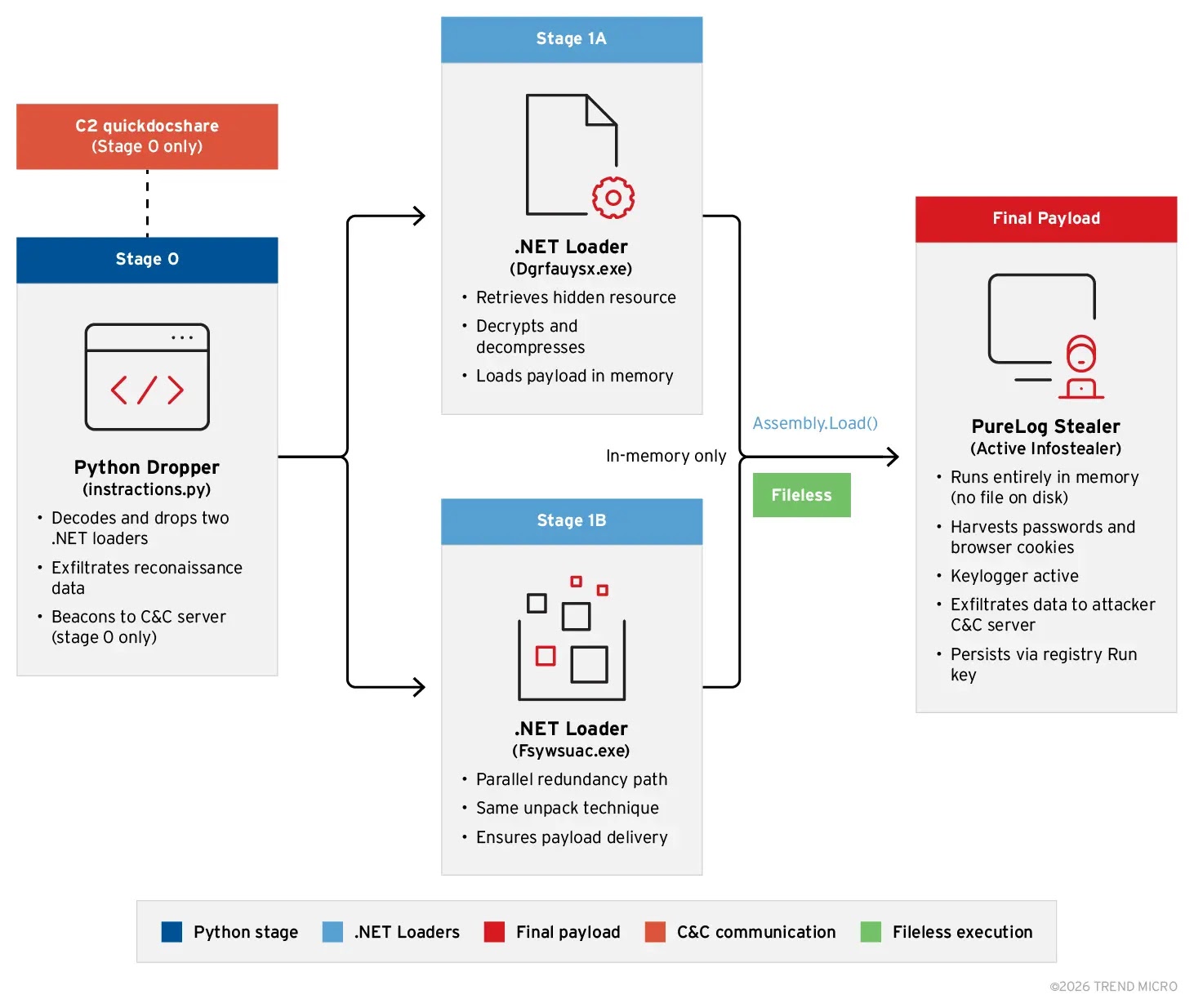
The malware uses encrypted payloads, remote decryption key retrieval, and fully in-memory execution — leaving very little forensic trace on compromised machines.
Endpoint detection tools that rely on file creation monitoring would find almost nothing to flag.
Inside the Multi-Stage Infection Chain
Once the victim executes the malicious lure, a command interpreter launches silently in the background.
To keep the user occupied, a harmless-looking decoy PDF immediately opens on screen.
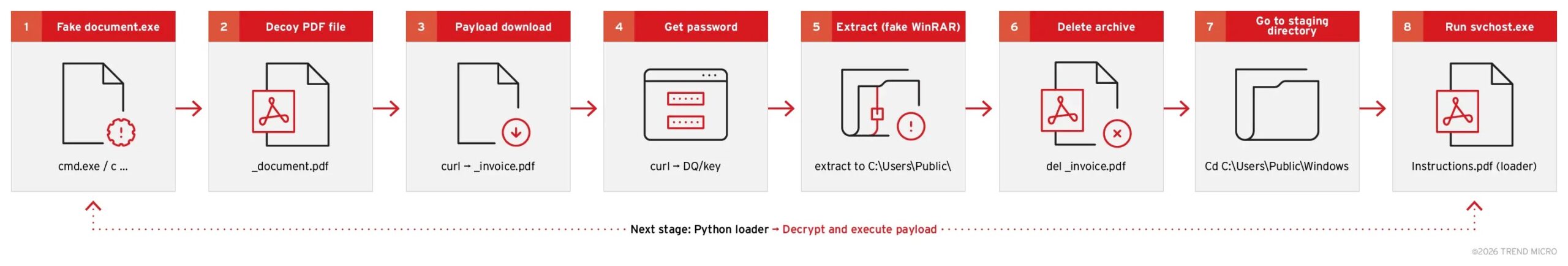
Meanwhile, the malware contacts attacker-controlled infrastructure to download an encrypted archive disguised as a PDF file named invoice.pdf.
Rather than embedding the decryption password inside the malware itself, the attackers retrieve it remotely from a separate server endpoint at runtime. This design makes offline analysis nearly impossible and allows the attacker to control or cancel each infection remotely.
A renamed WinRAR executable — disguised as a PNG image file — then uses that retrieved password to extract the real payload.
The extracted content includes a renamed Python interpreter called svchost.exe and a heavily obfuscated Python script named instructions.pdf.
The script first bypasses Windows Defender’s Antimalware Scan Interface by patching memory directly, preventing the system from scanning what follows.
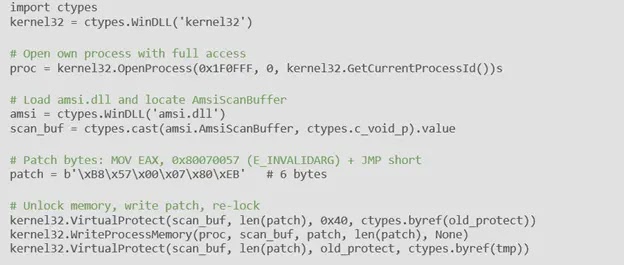
It then establishes registry persistence under HKCURunSystemSettings, ensuring the malware restarts automatically on every user login.
The script also takes a full-screen screenshot, collects the machine hostname, username, and installed antivirus product names, then sends all of it to the command-and-control server via an HTTPS POST request.
Finally, two identical .NET loader files decrypt and load PureLog Stealer directly into memory, leaving no files on disk for antivirus tools to find.
Organizations should train employees to treat unexpected emails about copyright violations with caution, especially those containing download links.
Security teams should monitor registry Run keys for unusual entries, watch for Python or WinRAR processes executing from non-standard directory paths, and block outbound connections to known malicious domains.
Behavioral detection tools and network telemetry are essential, as traditional signature-based antivirus may miss this campaign entirely due to its fileless execution design.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.