ClickFix Attack Leverages Windows/macOS Dialog Terminal
The social engineering technique known as ClickFix has re-emerged, targeting users on both Windows and macOS. It tricks individuals into manually executing malicious commands, which then covertly...
The social engineering technique known as ClickFix has re-emerged, targeting users on both Windows and macOS. It tricks individuals into manually executing malicious commands, which then covertly install malware on their devices.
First documented in late 2023, the method has rapidly grown from a niche tactic into one of the most widely adopted initial access strategies across the cybercriminal ecosystem.
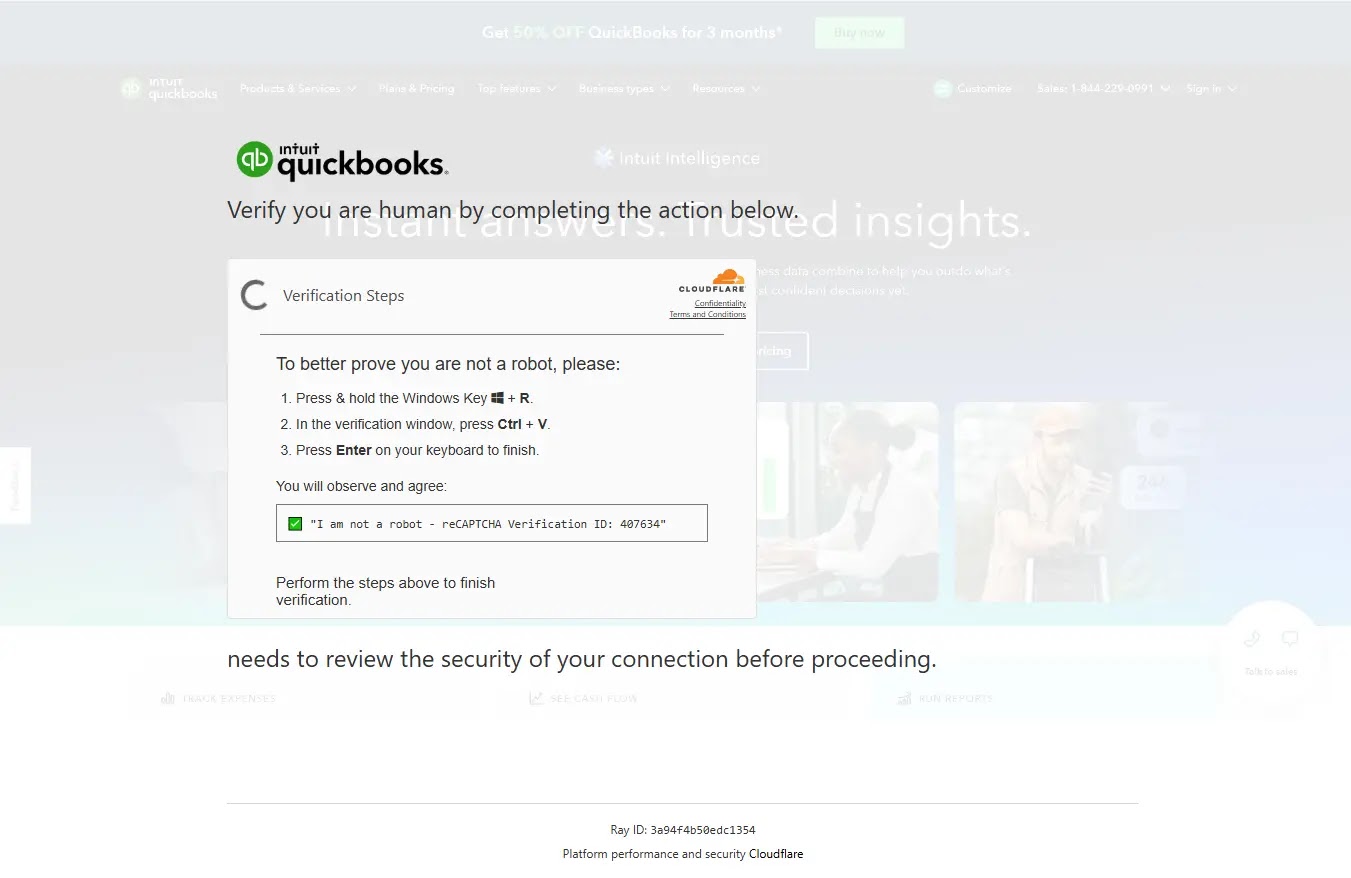
What makes ClickFix particularly dangerous is how routine it appears to unsuspecting users. Rather than exploiting a software flaw directly, it presents victims with a fake verification screen that mimics trusted services like Cloudflare CAPTCHA or Google reCAPTCHA.
A malicious command is silently placed on the clipboard through background JavaScript, and the victim is then instructed to paste it into the Windows Run dialog box or macOS Terminal — unknowingly giving the attacker direct access to their system.
Recorded Future’s Insikt Group researchers identified five distinct ClickFix clusters, each sharing the same core deception technique while differing in themes, infrastructure, and target sectors.
Impersonated services included Intuit QuickBooks, Booking.com, and the AI marketing platform Birdeye, with targets spanning accounting, travel, real estate, and legal services.
Published on March 25, 2026, the findings confirm that both cybercriminal groups and potentially state-sponsored actors such as APT28 and North Korea’s PurpleBravo are actively leveraging the method.
All five clusters rely on a living-off-the-land (LotL) approach, using trusted system tools already present on the operating system to carry out the attack.
By routing execution through native utilities like PowerShell or the macOS Terminal, attackers effectively operate outside the reach of most standard browser-based security defenses.
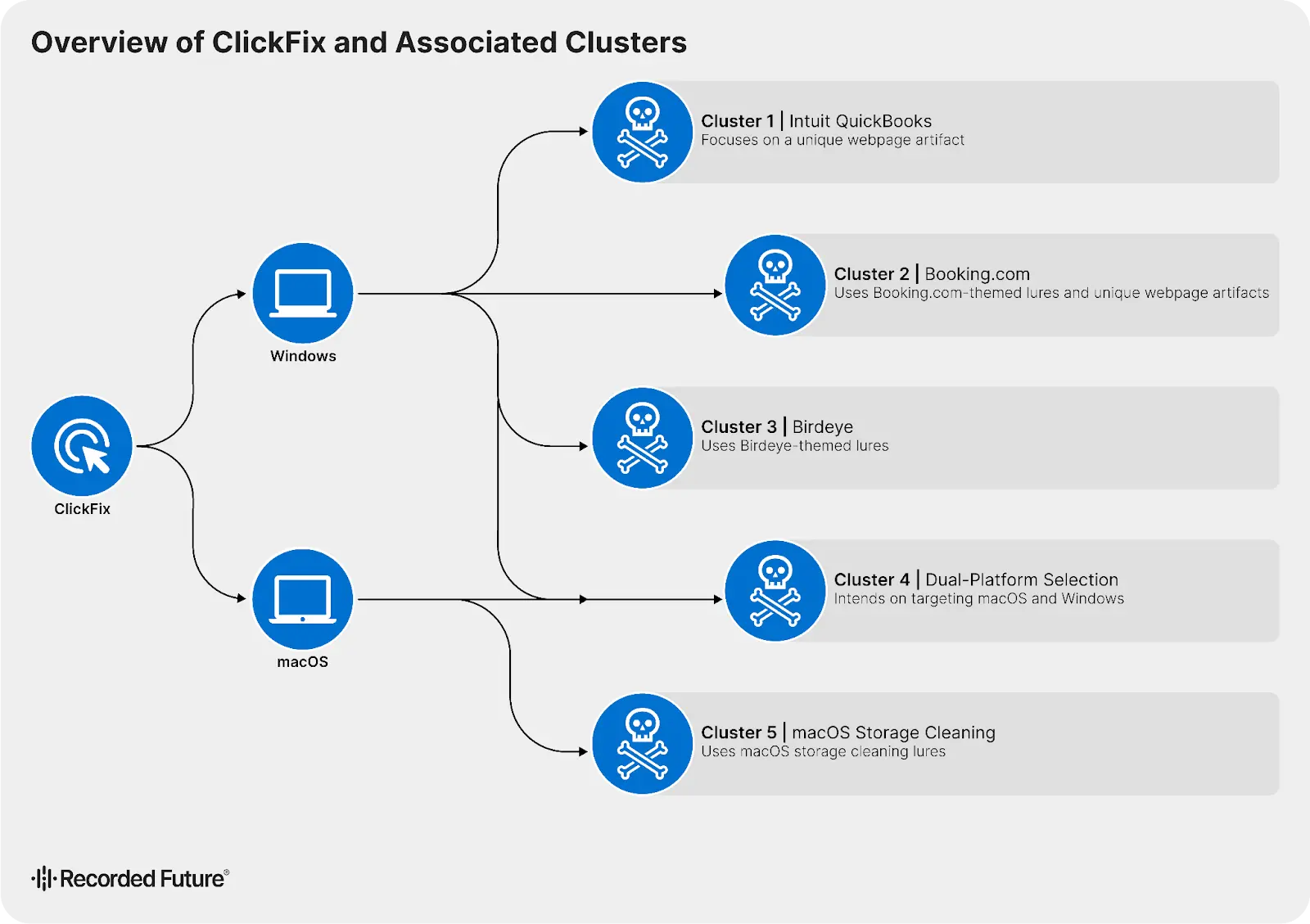
The malware families deployed across these campaigns include NetSupport RAT, Odyssey Stealer, Lumma Stealer, and MacSync — tools capable of remote system control, credential theft, and harvesting cryptocurrency wallet data from infected devices.
The Four-Stage Infection Chain
The ClickFix execution chain follows a consistent four-stage pattern across both Windows and macOS — beginning with an obfuscated input, moving through native system shell execution, pulling payloads from remote infrastructure, and finishing with in-memory execution that leaves almost no trace on disk.
On Windows, victims are guided to open the Run dialog box and paste what looks like a verification command.
In the QuickBooks cluster, the pasted command launches a hidden PowerShell process using mixed-case obfuscation and shortened parameter aliases to slip past signature-based detection.
This stager contacts attacker-controlled domains such as nobovcs[.]com and retrieves a secondary script, bibi.php, which installs NetSupport RAT.
The script also generates a randomly named folder under the user’s local app data directory using romantic-themed words — a deliberate move to blend in and avoid raising suspicion.
On macOS, the attack travels a similar path through the Terminal. In Cluster 5, a page impersonating Apple’s support site instructed users to run a command to free up storage space.
That command used stacked encoding layers — first decoding hex to Base64, then piping the result through the zsh shell — to silently fetch and run MacSync, an information stealer.
Cluster 4 extended this further by detecting the victim’s operating system and serving a tailored command for each platform, showing how carefully threat actors are refining these attacks.
![Landing Page for mac-os-helper[.]com (Source - RecordedFuture)](https://hackersradar.com/wp-content/uploads/2026/03/content_1774555257_2777.jpg)
Once execution completes, the final payload runs entirely in memory, leaving almost no forensic evidence on the device. On Windows, persistence is established by placing a shortcut in the Startup folder, ensuring the malware automatically reactivates on every reboot.
Security teams should disable the Windows Run dialog box through Group Policy Objects to remove a primary delivery path.
Implementing PowerShell Constrained Language Mode alongside AppLocker or Windows Defender Application Control policies will help block unauthorized script execution.
On macOS, terminal access should be restricted through mobile device management, with System Integrity Protection kept enabled at all times.
Across both platforms, conducting targeted user awareness training that specifically addresses manual verification prompt scams remains one of the most effective ways to stop a ClickFix attack before any malicious command ever runs.
Continuously updating SIEM and EDR platforms with current threat intelligence to block newly identified staging and command-and-control domains adds another critical layer of defense.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.