Claude Leak Used to Spread Vidar & GhostSocks Malware
A massive source code leak from Anthropic has put the cybersecurity community on high alert. On March 31, 2026, the company accidentally exposed the complete source code for Claude Code, its flagship...
A massive source code leak from Anthropic has put the cybersecurity community on high alert. On March 31, 2026, the company accidentally exposed the complete source code for Claude Code, its flagship terminal-based coding assistant.
The leak occurred due to a packaging error in a public npm package, which inadvertently included a JavaScript source map file containing over half a million lines of unobfuscated TypeScript. While the exposed data did not include model weights or user data, it did reveal highly sensitive internal mechanisms.
Almost immediately after security researcher Chaofan Shou publicly disclosed the incident on social media, the codebase was mirrored across GitHub and forked tens of thousands of times.
The widespread availability of the proprietary code has created a massive vector for supply chain attacks. Cybercriminals are now actively weaponizing this incident, creating malicious forks designed to compromise developer workstations.
Zscaler ThreatLabz researchers recently discovered a highly deceptive campaign leveraging the leak as a social engineering lure to target developers seeking access to the source code.
Delivering Vidar and GhostSocks Malware
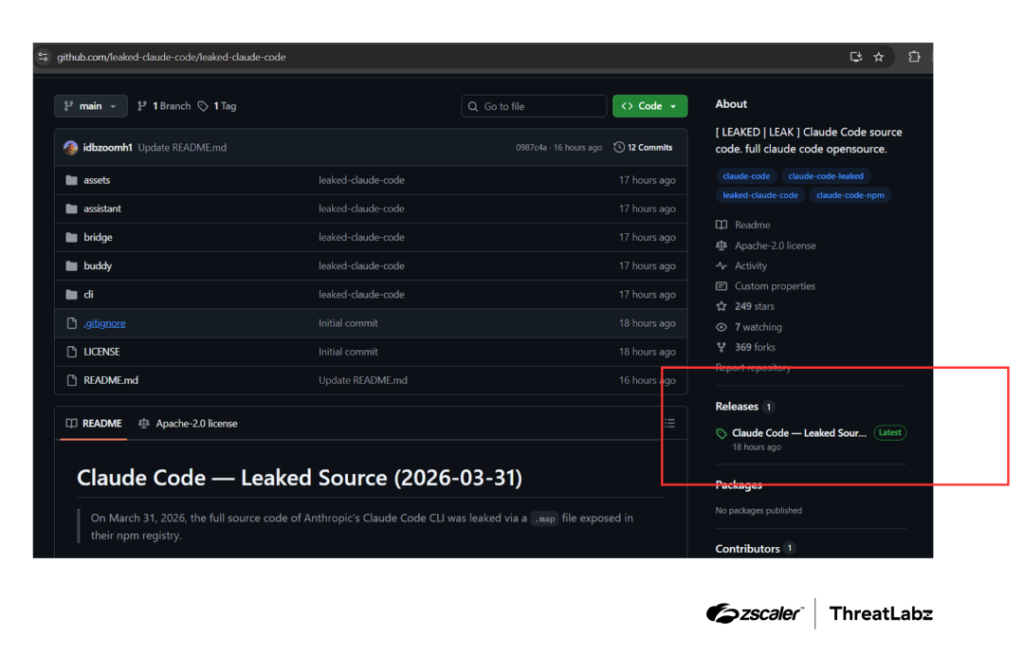
In this newly discovered campaign, attackers have established malicious GitHub repositories that masquerade as the authentic leaked repository.
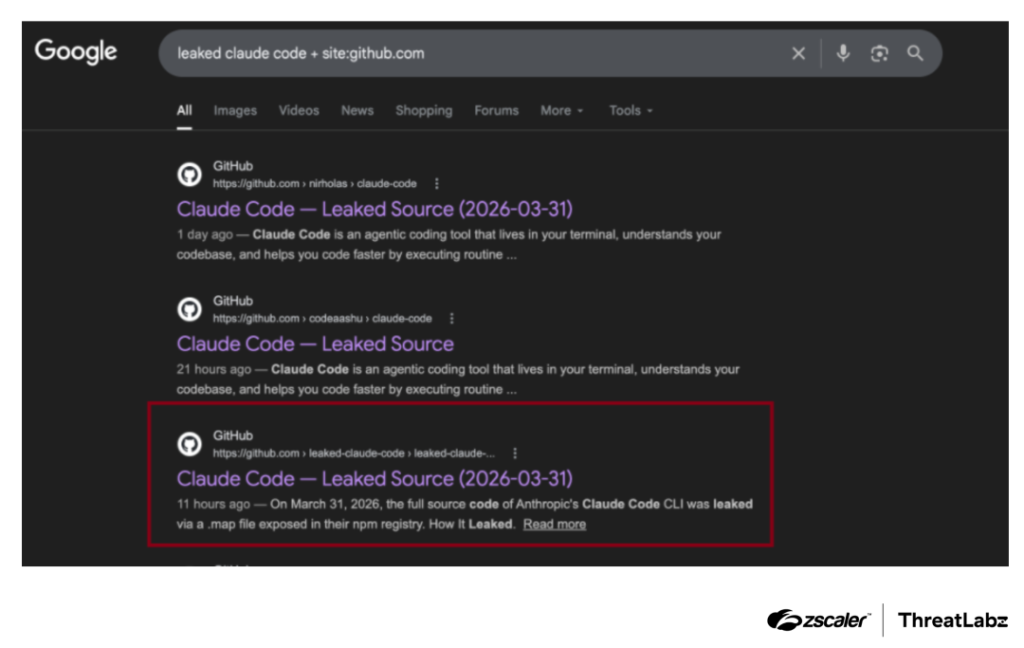
One prominent page, published by a threat actor named idbzoomh, currently ranks near the top of search engine results for users attempting to find the files.
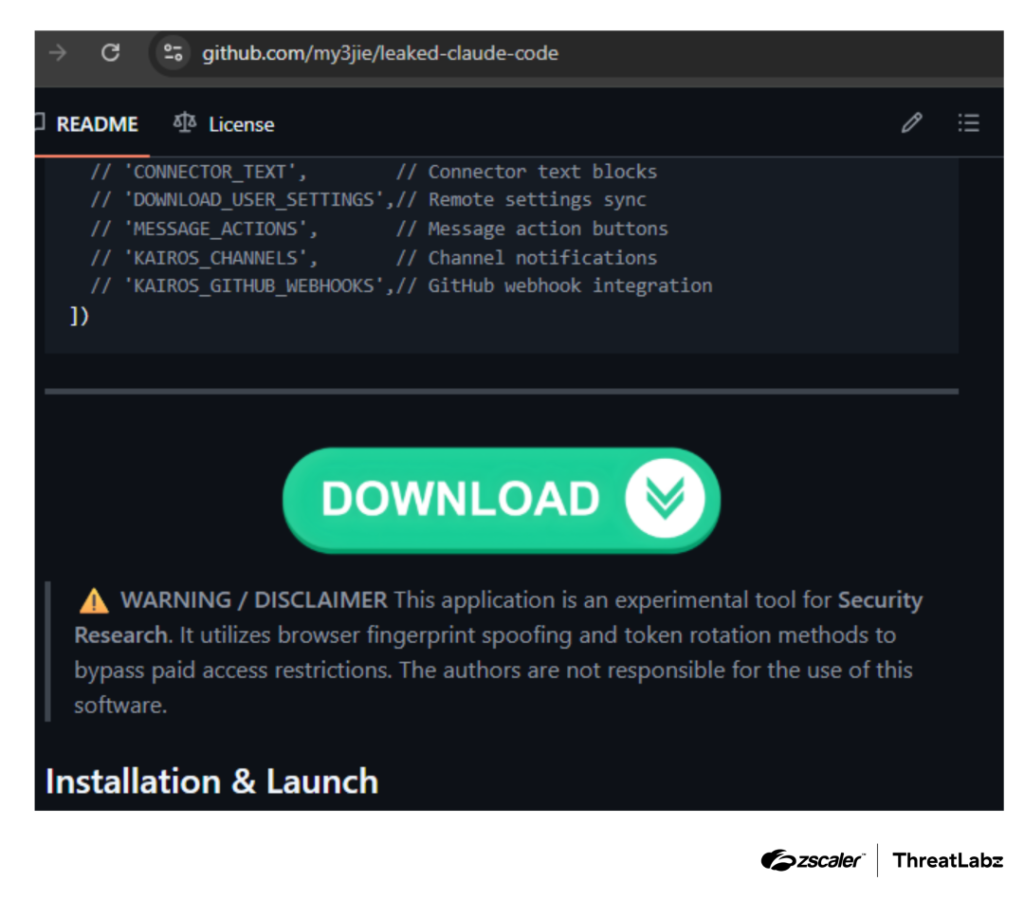
The repository promises an unlocked version of the enterprise software featuring no usage limits. Instead of legitimate code, the provided zip archive contains a Rust-based dropper executable.
Upon execution, this dropper deploys the Vidar information stealer to siphon sensitive credentials and GhostSocks to proxy network traffic.
This deployment of GhostSocks closely mirrors previously observed campaigns where threat actors utilized fake software installers to distribute network proxies alongside data-stealing malware.
The exposure of these internal components presents severe risks that extend far beyond simple social engineering lures. The leaked files reveal complex orchestration details, permission execution layers, persistent memory systems, and dozens of hidden internal feature flags.
Because the original codebase includes advanced capabilities for local shell execution and auto-executing scripts, threat actors possessing the full source can easily craft precise exploits.
Attackers can potentially trigger silent device takeovers or credential theft simply by tricking a developer into cloning an untrusted repository or opening a specially crafted project file.
Mitigation and Defense Strategies
Organizations must implement immediate defensive measures to protect their development environments from these opportunistic attacks.
Security teams should strongly advise all developers against downloading, building, or running any code claiming to be the leaked Anthropic software. Relying strictly on official channels and signed binaries is essential for maintaining integrity.
Furthermore, implementing a Zero Trust architecture and segmenting access to critical applications will help limit the potential blast radius if a developer workstation becomes compromised.
Monitoring for anomalous outbound network connections and scanning local environments for unexpected npm packages are critical steps for identifying early signs of infection.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.