Check Point Harmony SASE Windows Flaw Allows Client Vulnerability
A critical privilege-escalation vulnerability has been identified in Check Point’s Harmony SASE (Secure Access Service Edge) Windows client software, impacting versions prior to 12.2. Tracked...
A critical privilege-escalation vulnerability has been identified in Check Point’s Harmony SASE (Secure Access Service Edge) Windows client software, impacting versions prior to 12.2.
Tracked as CVE-2025-9142, the flaw allows local attackers to write or delete files outside the intended certificate working directory, potentially leading to system-level compromise.
The vulnerability exists within the Service component of Perimeter81 software (Perimeter81.Service.exe), which operates with SYSTEM privileges.
The flaw stems from insufficient validation of JWT (JSON Web Token) values during authentication.
| CVE ID | Product | Affected Versions | Severity |
|---|---|---|---|
| CVE-2025-9142 | Harmony SASE Windows Client | Below 12.2 | Medium |
When users initiate the Perimeter81 login flow through a URI handler, the JWT token is passed to the service via an IPC call, but is processed without proper signature verification.
A malicious actor can craft a specially designed perimeter81:// URL with a tampered JWT containing directory traversal sequences (../../../) in the tenant ID field.
This bypasses authentication controls and reaches the local service component, which fails to validate the token before processing it.
Technical Attack Chain
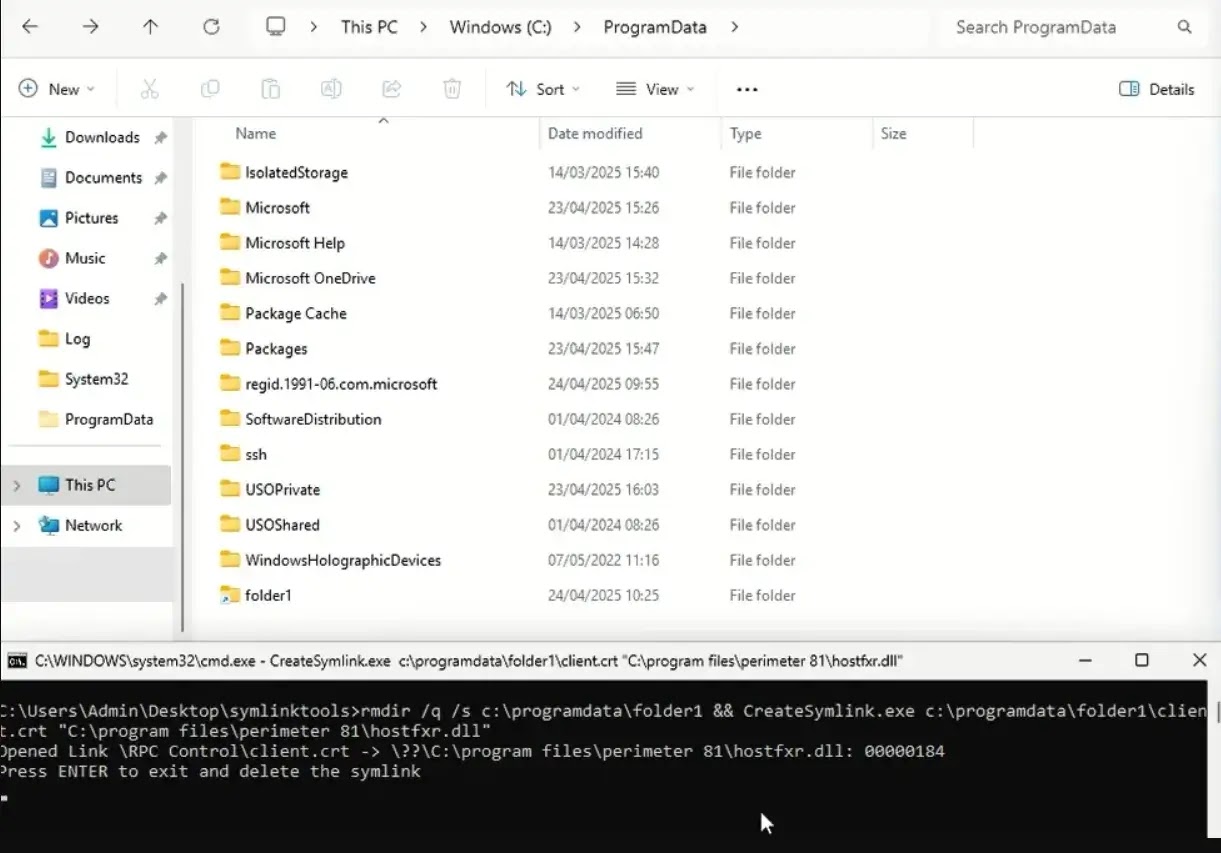
The exploitation chain unfolds in two distinct phases. First, the attacker registers a rogue authentication domain; notably, p81-falcon.com was available for registration at the time of discovery.
This domain passes the client’s whitelist validation. The JWT manipulation enables directory traversal, allowing the adversary to force the Perimeter81 service to create folder structures outside the intended location.
The second phase leverages symbolic link injection. When the GenerateAndLoadCertificates() function executes, it writes client certificates to the attacker-controlled working directory with SYSTEM privileges.
By exploiting Windows Object Manager and RPC Control directory symlinks, an attacker can redirect certificate writes to arbitrary system locations such as C:WindowsSystem32.
Exploitation Impact
This primitive enables attackers to overwrite critical system files or inject malicious DLLs. Process monitoring revealed the service attempting to load missing DLLs from its working directory.
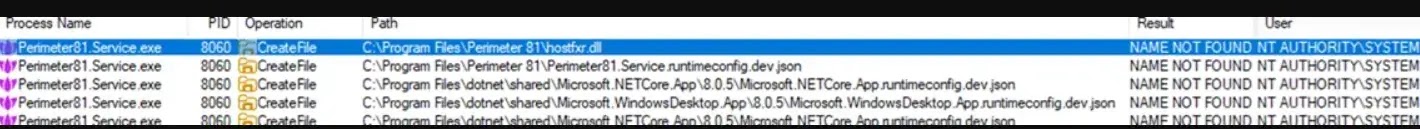
By placing a malicious DLL at these expected locations, attackers can execute code when the Perimeter81 service restarts, thereby escalating to SYSTEM-level access.
The vulnerability is further amplified by the fact that the service’s file-handling logic fails to enforce strict trust boundaries between user input and privileged operations.
Check Point was notified of the vulnerability on March 16, 2025, and released a fix in version 12.2 on November 18, 2025. The CVE was publicly disclosed on January 14, 2026.
Organizations using Harmony SASE must immediately upgrade to version 12.2 or later to mitigate the risk of local privilege escalation attacks.
Organizations should immediately deploy Harmony SASE agent version 12.2 or later, according to Amberwolf advisory.
Additionally, restrict local administrative access and implement application whitelisting to prevent unauthorized DLL injection attacks.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.