Beware: Fake WinRAR Website Delivers Malware Installer
A newly identified malware campaign is leveraging fraudulent WinRAR download sites to Delivers Malware Installer presents a significant threat to anyone seeking quick software solutions without...
A newly identified malware campaign is leveraging fraudulent WinRAR download sites to Delivers Malware Installer presents a significant threat to anyone seeking quick software solutions without verifying legitimate download sources.
The attackers exploit the widespread practice of downloading WinRAR from third-party websites by packaging harmful code alongside the real installer.
Once executed, the malware begins profiling the target system by accessing Windows profile information, allowing it to select and deploy the most effective payload for each victim.
This adaptive approach ensures maximum success rates across different computer configurations, making the threat particularly dangerous for both personal and business environments.
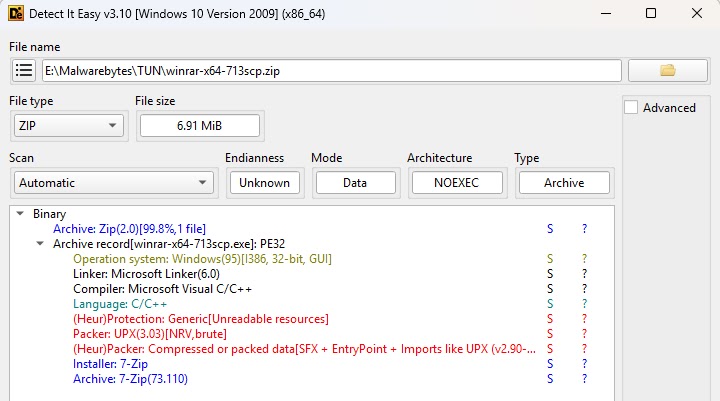
Malwarebytes analysts identified this sophisticated attack after discovering the initial suspicious file hidden within multiple protective layers of code obfuscation and compression.
Infection mechanism
The infection mechanism reveals a complex multi-stage delivery system designed specifically to evade detection.
The original file, named winrar-x64-713scp.zip, contains a UPX-packed executable that uses deliberate anomalies in its structure to complicate analysis.
When unpacked with specialized tools, the file exposes two embedded programs: the legitimate WinRAR installer and a password-protected archive named setup.hta.
The setup.hta archive represents the actual malicious component, which remains obfuscated until runtime when it gets unpacked directly into system memory.
This memory-resident technique prevents simple file-based detection methods from identifying the threat. During dynamic analysis on isolated systems, researchers discovered the file spawns nimasila360.exe, a component associated with the Winzipper malware family.
Once installed, Winzipper operates as a backdoor trojan, providing attackers with remote access to compromised machines.
The malware enables data theft, unauthorized system control, and installation of secondary malware payloads, all while appearing as a legitimate file archive utility. Users typically remain unaware of the infection until significant damage occurs.
The compromised domains include winrar-tw.com, winrar-x64.com, and winrar-zip.com, all currently blocked by Malwarebytes protection systems.
Users should download WinRAR exclusively from official sources and maintain current anti-malware protection to prevent infection from these fake installer campaigns.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.