Attackers Use Fake RTO Challan Notifications for Android
A sophisticated Android malware campaign targeting Indian users has emerged, disguising itself as legitimate Regional Transport Office (RTO) challan notifications. The malicious applications are...
A sophisticated Android malware campaign targeting Indian users has emerged, disguising itself as legitimate Regional Transport Office (RTO) challan notifications.
The malicious applications are distributed outside the Google Play Store, primarily through WhatsApp and similar messaging platforms, exploiting user trust in government services.
Threat actors send fake traffic violation alerts to victims, instructing them to install an “E-Challan” or “RTO Challan” mobile application, which contains malware designed to steal financial and personal information.
This campaign represents a dangerous evolution in mobile threats, incorporating a three-stage modular architecture that enhances its ability to evade detection and maintain persistence on infected devices.
Unlike earlier variants that used single-stage APKs with hardcoded logic, this current operation employs dynamic remote configuration and extensive anti-analysis techniques.
The malware creates a custom VPN tunnel to mask its network activity, enabling covert data exfiltration while preventing security tools from detecting command-and-control communication.
Seqrite researchers identified the sophisticated social engineering tactics employed by attackers during their security analysis.
The malicious apps present fraudulent user interfaces mimicking official government portals, complete with RTO branding and logos, to convince users of their legitimacy.
Once installed, the malware prompts users to grant high-risk permissions including SMS access, call logs, notification listeners, and storage access, which enables comprehensive surveillance of the victim’s device.
The malware establishes persistent control by requesting users to disable battery optimization settings, allowing it to run continuously in the background without system restrictions.
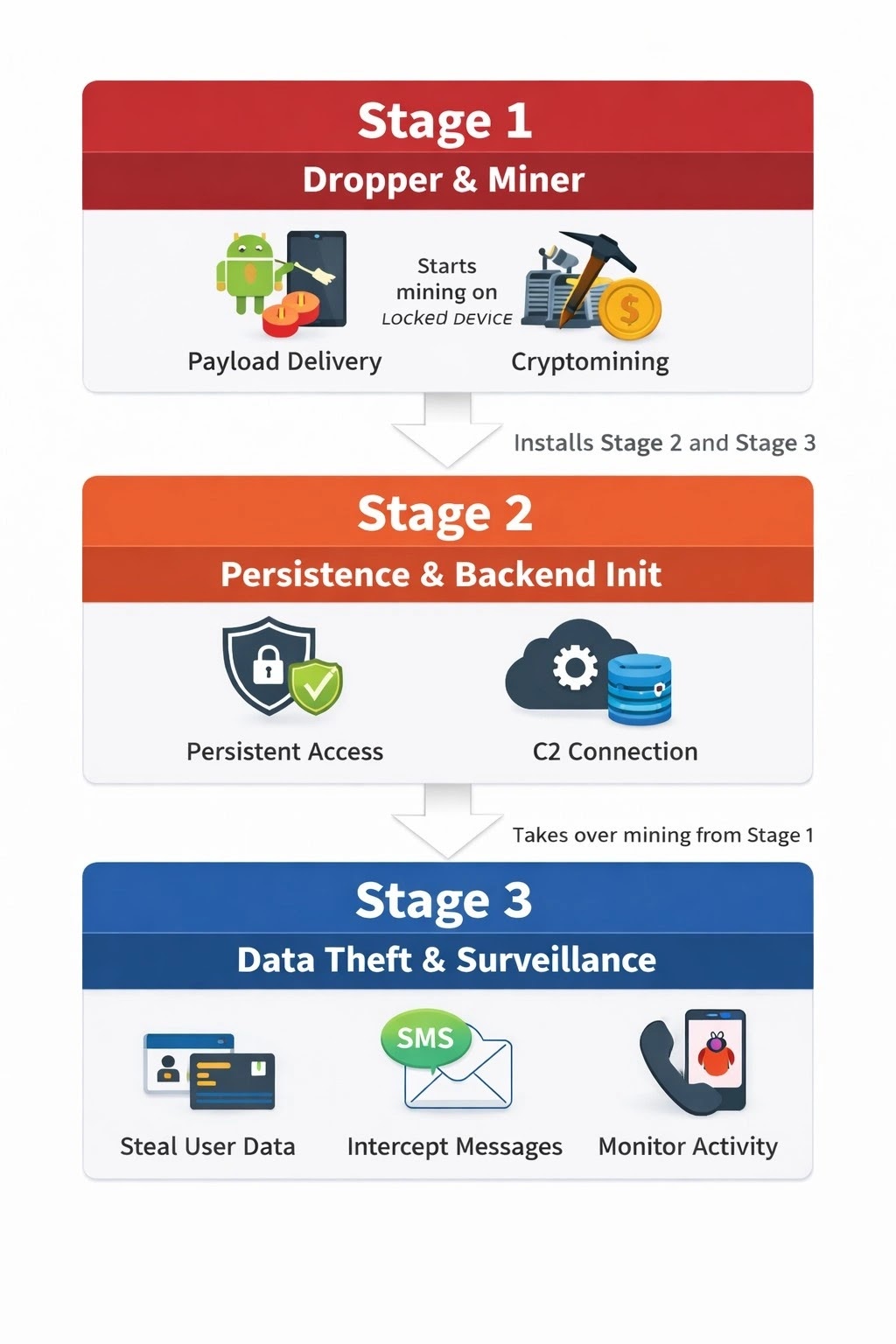
This ensures the malicious application can operate uninterrupted and maintain an active connection to its command-and-control infrastructure.
The attack results in large-scale financial fraud, identity theft, and complete device compromise as the malware harvests banking notifications, OTP messages, and device metadata.
Infection Mechanism and Permissions Abuse
The infection process begins when victims receive SMS or WhatsApp messages containing shortened URLs that mimic legitimate e-Challan domains.
These messages create urgency by threatening license suspension, court summons, or legal proceedings for unpaid traffic fines.
When users click the link and install the APK file, the malware initiates its multi-stage deployment sequence.
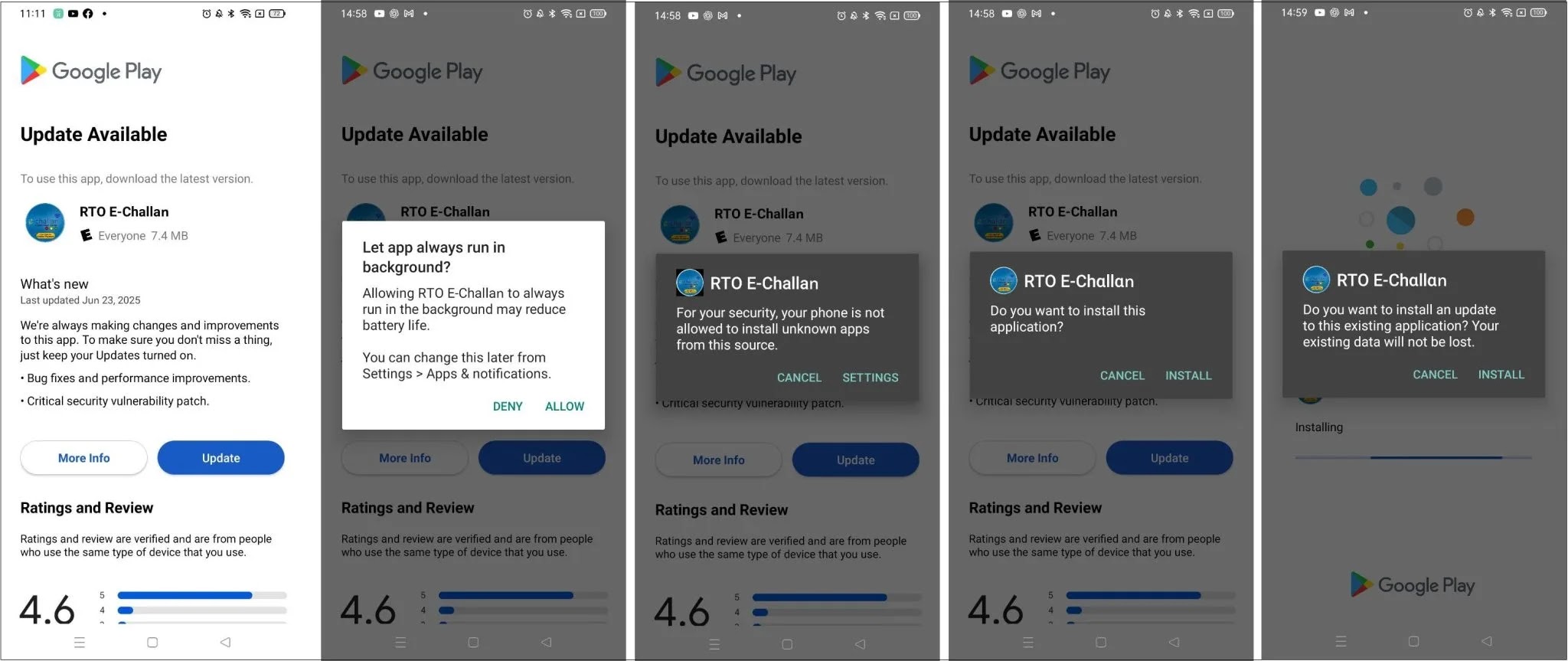
After installation, the third-stage application presents a fake government interface that prompts users to verify their identity or clear a pending challan.
To proceed, users must grant multiple dangerous permissions that grant the malware access to sensitive device functions.
.webp)
Once these permissions are approved, the malware begins harvesting personal identity information, banking notifications, OTP messages, and device metadata.
The malware implements a foreground service deception technique, creating a fake notification that runs continuously while malicious activities occur in the background.
Users should verify traffic fines only through official government websites rather than clicking links in unsolicited messages.
Avoid downloading applications from sources outside the Google Play Store, and never grant unnecessary permissions to applications requesting access to SMS or notifications.
Organizations should implement mobile threat defense solutions and conduct security awareness training to help employees recognize social engineering tactics.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.