Attackers Hijack Official GitHub Desktop, Dist Hijacking Repository
Cybercriminals are now exploiting fundamental aspects of GitHub’s operations to trick developers into downloading malware. The attack involves creating fake versions of the GitHub Desktop...
Cybercriminals are now exploiting fundamental aspects of GitHub’s operations to trick developers into downloading malware.
The attack involves creating fake versions of the GitHub Desktop installer and making them appear legitimate to unsuspecting users.
Between September and October 2025, this campaign primarily targeted users in Europe and the European Economic Area, though infections spread to Japan and other regions.
The malware, disguised as a standard development tool installer, represents a serious threat to developers who rely on GitHub for their daily work.
The attack chain begins when criminals create throwaway GitHub accounts and fork the official GitHub Desktop repository.
They then modify the download links in the README file to point toward their malicious installer instead of the legitimate one. Using sponsored advertisements targeting searches for “GitHub Desktop,” attackers promote these infected files to developers.
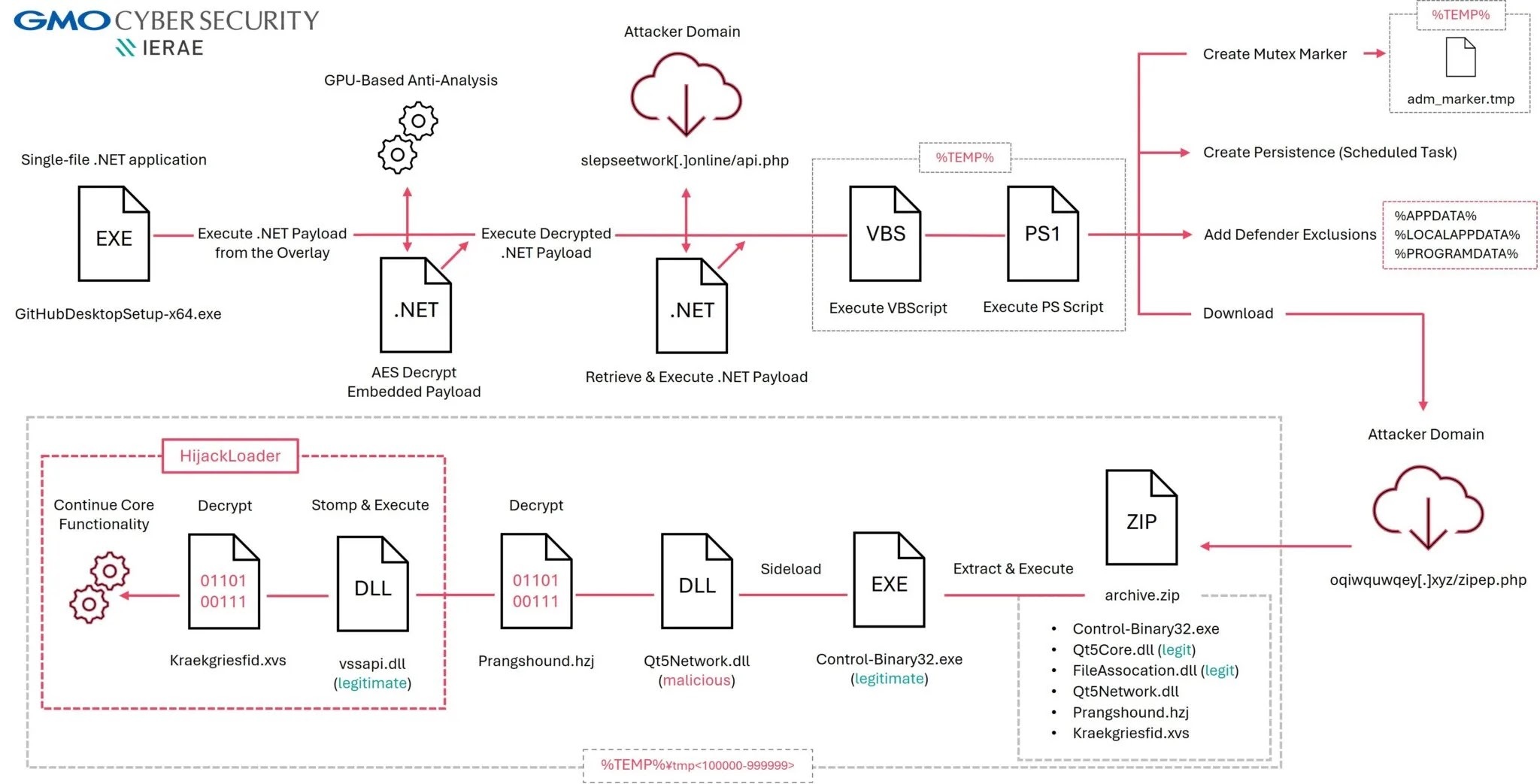
The criminals exploit a feature in GitHub’s design that allows commits from forked repositories to remain visible under the official repository’s namespace, even after the original fork or account is deleted.
This technique, called repo squatting, makes it extremely difficult for GitHub to track and remove malicious content.
GMO Cybersecurity analysts identified that this campaign represents an adaptive, ongoing threat that continues evolving.
The malicious Windows installer detected by the researchers, named GitHubDesktopSetup-x64.exe with a file size of 127.68 megabytes, serves as a multi-stage loader.
Similar malicious samples have been discovered disguised under other application names including Chrome, Notion, 1Password, and Bitwarden installers dating back to May 2025.
Analyzing the Infection Mechanism and Advanced Evasion Tactics
The infection mechanism reveals sophisticated technical deception.
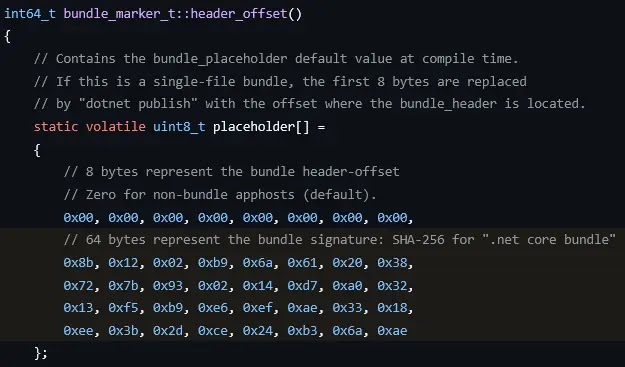
The malicious installer appears as a standard C++ application on the surface, but analysis of its debug information reveals it is actually a single-file .NET application bundled into a single executable called an AppHost.
The actual malicious .NET payload hides within the file’s overlay section, making it invisible to simple scanning tools.
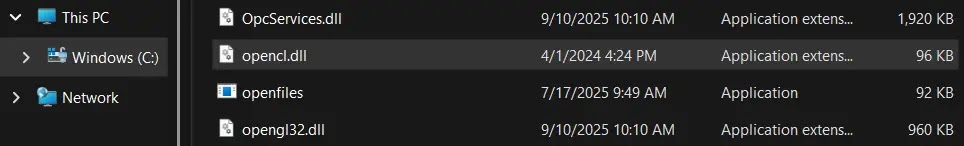
What makes this particularly concerning is that the malware incorporates a GPU-based API called OpenCL to deliberately prevent analysis in standard sandbox environments.
Most security testing sandboxes and virtual machines lack GPU drivers or OpenCL support, forcing security researchers to conduct analysis on actual physical machines with real graphics hardware before understanding the malware’s true behavior.
This technique, dubbed GPUGate, represents deliberate anti-analysis protection designed to slow down security researchers.
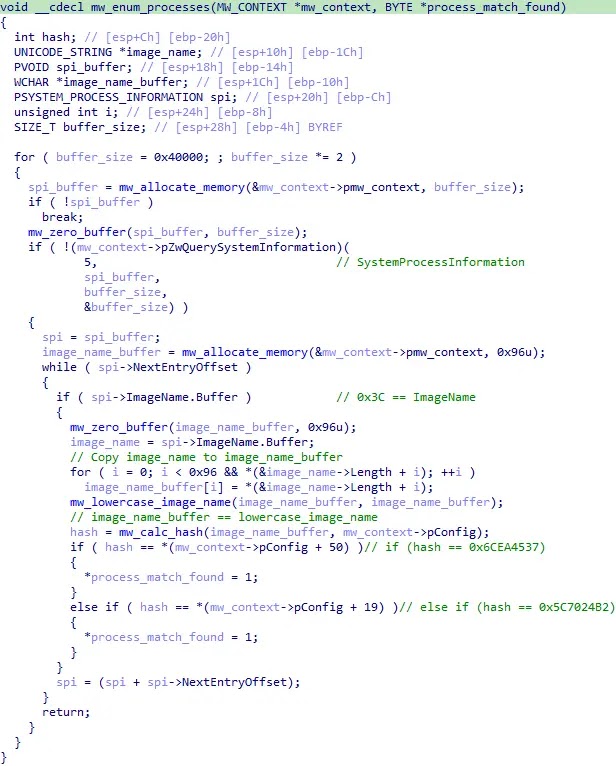
Additionally, the malware intentionally uses code misdirection tactics to confuse analysts attempting to recover the decryption keys statically.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.