Adobe Breach Leaks 13 Million Support Tickets Threat Actor
Threat actor “Mr. Raccoon” has allegedly breached Adobe, claiming to have exfiltrated a massive trove of sensitive data. This cache reportedly comprises 13 million support tickets, all containing...
Threat actor “Mr. Raccoon” has allegedly breached Adobe, claiming to have exfiltrated a massive trove of sensitive data. This cache reportedly comprises 13 million support tickets, all containing personal information, 15,000 employee records, every HackerOne bug bounty submission, and a range of internal documents. International Cyber Digest published details of these claims on April 3, 2026.
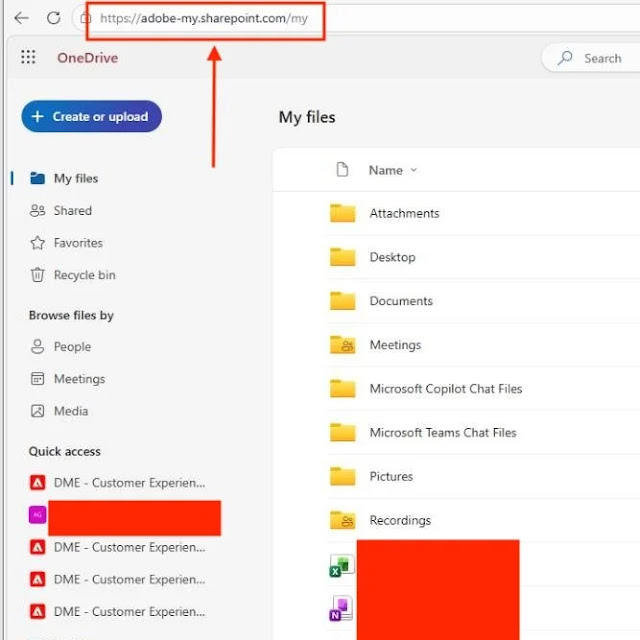
According to details shared by the threat actor, the intrusion did not begin directly within Adobe’s infrastructure. Instead, Mr. Raccoon allegedly gained initial access through an Indian Business Process Outsourcing (BPO) firm contracted by Adobe, a classic supply chain pivot that highlights growing risks in third-party vendor relationships.
Attack Chain Via BPO
The attacker reportedly deployed a Remote Access Tool (RAT) on a BPO employee’s machine via a malicious email. Once that foothold was established, Mr. Raccoon escalated access by phishing the compromised employee’s manager, broadening control within the network.
The RAT deployment reportedly also gave the attacker webcam access on the targeted employee, along with the ability to intercept private communications through WhatsApp.
Perhaps the most alarming disclosure came directly from Mr. Raccoon, who told International Cyber Digest: “They allowed you to export all tickets in one request from an agent.” This suggests a significant access control misconfiguration within Adobe’s support ticketing platform — one that allowed bulk data extraction without triggering adequate security controls or rate-limiting mechanisms.
International Cyber Digest stated that its team reviewed multiple files confirming the breach’s scope. The alleged stolen dataset is particularly sensitive for several reasons.
Support tickets typically contain customer names, email addresses, account details, and descriptions of technical issues, a goldmine for phishing campaigns and identity theft.
The inclusion of HackerOne submissions is especially concerning, as these contain unpublished vulnerability reports that could be weaponized by other threat actors before patches are deployed.
Adobe has yet to issue an official statement confirming or denying the breach. If verified, this incident would represent one of the more significant data exposures of 2026, raising urgent questions around third-party vendor security vetting, privileged access management in support environments, and the risks of overly permissive data export capabilities in enterprise ticketing systems.
Security teams across industries are advised to monitor their own BPO and contractor access pathways, audit bulk data export permissions, and watch for any credential or vulnerability data from this alleged breach appearing on dark web forums.
Note: This article is based on unverified claims reported by International Cyber Digest. Adobe has not officially confirmed the breach at the time of publication.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.