Hackers Abuse OAuth Flow to Steal Microsoft Device Authorization
Attackers are abusing a lesser-known element within Microsoft’s authentication system, allowing them to compromise user account credentials at scale. Device code phishing campaigns now target...
Attackers are abusing a lesser-known element within Microsoft’s authentication system, allowing them to compromise user account credentials at scale.
Device code phishing campaigns now target organizations worldwide by manipulating the OAuth device authorization flow, turning a security feature into a major vulnerability.
This emerging threat has surged dramatically since late 2024, catching security teams unprepared for attacks that operate entirely through legitimate Microsoft infrastructure.
The spike in device code phishing marks a notable evolution in identity takeover techniques.
Previously obscure among cybercriminals, this attack method now appears regularly in campaigns ranging from business email compromise to corporate espionage.
From 2023 to 2024, criminals increasingly abandoned traditional credential harvesting pages in favor of device code techniques.
Analysts from Proofpoint identified the malicious activity in early 2025 and said in a report shared with Cyber Security News (CSN) that hundreds of campaigns targeted organizations across multiple industries.
The research team observed threat actors using device code phishing to gain unauthorized access to Microsoft 365 accounts at an unprecedented scale.
The technique exploits trust in official Microsoft services, making detection exceptionally difficult for traditional security tools.
Hackers Abuse OAuth Device Authorization Flow
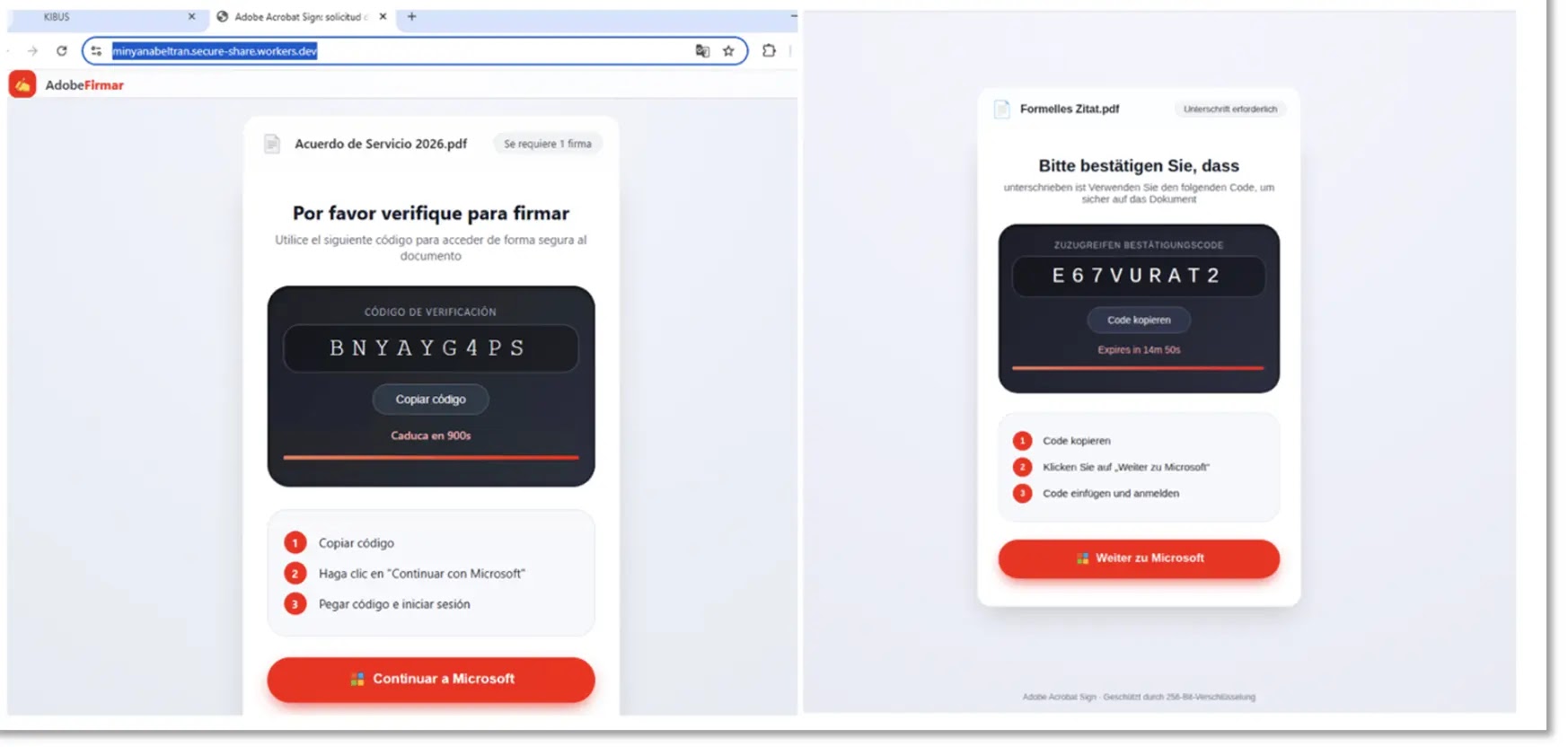
Device code phishing exploits OAuth 2.0 device authorization flow, a feature designed to help users authenticate on devices with limited input capabilities like smart TVs or gaming consoles.
When users visit a legitimate Microsoft page and enter a code provided by attackers, the system assumes they are completing normal authentication.
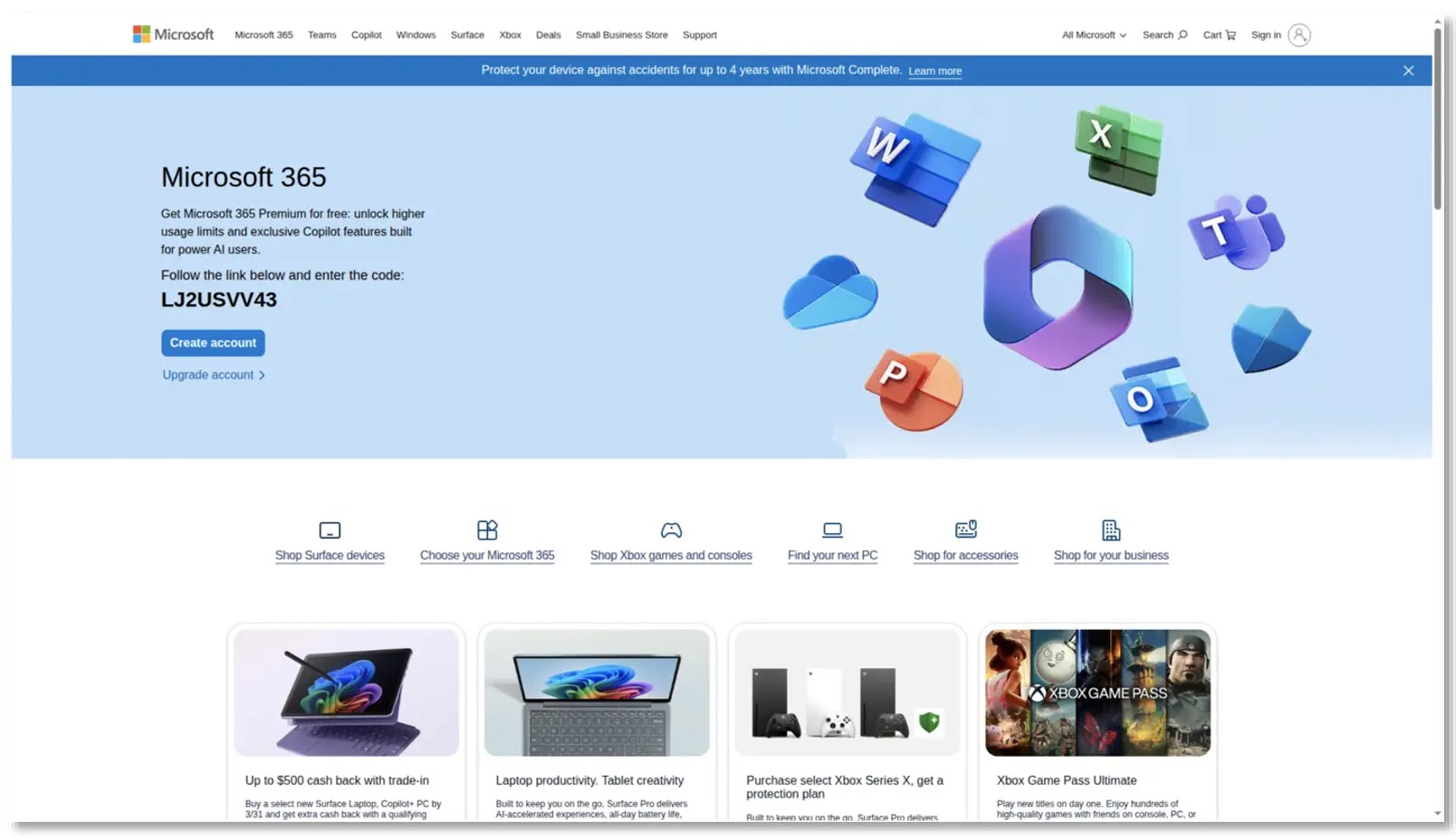
The victim unknowingly grants full access to their Microsoft 365 account without ever seeing a suspicious login prompt.
Attackers typically deliver device codes through email campaigns containing PDF attachments, URLs, or QR codes that redirect victims to the official Microsoft device login page.
Once the target enters the code within the 15-minute expiration window, threat actors immediately gain access to authentication tokens. These tokens allow persistent account access even if the victim later changes their password.
The technique requires minimal technical skill compared to traditional credential phishing. Threat actors simply generate device codes using legitimate Microsoft APIs and distribute them through social engineering.
The seamless integration with Microsoft’s authentication systems means no red flags appear during the process. Email messages often impersonate common business services, urging recipients to take immediate action by entering the provided code.
Rising Threat Actor Adoption
Multiple threat groups now leverage device code phishing across different attack scenarios. Proofpoint researchers documented campaigns from threat actor TA4903, who distributed device code phishing lures alongside PDF attachments containing CAPTCHA-themed social engineering.
The group targeted small businesses and government entities, impersonating services like Microsoft, DocuSign, and Norton.
Other threat actors including EvilProxy operators, Storm-365, and groups using the Kali 365 toolkit have integrated device code phishing into their standard operations.
The Tycoon 2FA phishing kit added device code capabilities, while researchers observed the technique in campaigns linked to Russian cybercriminal infrastructure.
Even security-aware users struggle to identify the attack since the entire process occurs on genuine Microsoft domains without any suspicious indicators.
The proliferation accelerated after proof-of-concept tools like ClickFix emerged, lowering barriers to entry for less sophisticated criminals.
What began as a technique used by advanced persistent threat groups quickly spread across the threat landscape. Device code phishing now appears in campaigns targeting everyone from individual users to Fortune 500 enterprises.
Organizations should implement several defensive measures to counter this threat, Proofpoint said in a report shared with Cyber Security News (CSN). Blocking device code flow where possible through conditional access policies provides the strongest protection.
Requiring compliant or managed devices prevents unauthorized authentication attempts from uncontrolled endpoints. Enhanced user awareness training specifically addressing device code phishing attacks is critical, as traditional phishing education does not cover this threat vector.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| Domain | onedrive-9tudh[.]thebootieselmny-thi-om-s-oundh[.]workers[.]dev | EvilTokens Device Code Phishing Landing |
| Domain | voicemail-8c[.]min-treyriess-aly-om-s-oundh[.]workers[.]dev | EvilTokens Device Code Phishing Landing |
| Domain | wex-9[.]mark-squiress-axerservernes-om-s-oundh[.]workers[.]dev | EvilTokens Device Code Phishing Landing |
| Domain | lyr[.]nuskly-msk-om-s-oundh[.]workers[.]dev | EvilTokens Device Code Phishing Domain |
| Domain | 0uh4-wem-j7u18h[.]vesquezz-serintoncs-rtneres-om-s-oundh[.]workers[.]dev | EvilTokens Device Code Phishing Landing |
| Domain | ytgw4-c9n60-xelw[.]vesquezz-serintoncs-rtneres-om-s-oundh[.]workers[.]dev | EvilTokens Device Code Phishing Landing |
| Domain | z9746881-9[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | 014772-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | jo2c7259t-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | 9803t97c4t9t-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | 10399t0b4c-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | yg4c05t9t501010-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | c649c5c710416-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | 757c46-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | 187906187-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | t918c7186a7-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | 1010c5c4t918-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | 014772-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | 014t90t901-[.]nspoint[.]com | Device Code Phishing Domain |
| Domain | stelwsystems[.]com | B-OX Device Code Phishing Domain |
| Domain | marketkarr-lengnefl[.]com | B-OX Device Code Phishing Domain |
| Domain | realizeextension[.]com | B-OX Device Code Phishing Domain |
| Domain | servicewithoutinterruption[.]com | B-OX Device Code Phishing Domain |
| Domain | marketreliabilityservices[.]com | B-OX Device Code Phishing Domain |
| Domain | kohl-hoff-lasthealthverreitung[.]com | B-OX Device Code Phishing Domain |
| Domain | reliefsupport[.]com | B-OX Device Code Phishing Domain |
| Domain | eurostrustwav[.]com | B-OX Device Code Phishing Domain |
| Domain | trustengagement[.]com | B-OX Device Code Phishing Domain |
| Domain | methoilness[.]com | B-OX Device Code Phishing Domain |
| Domain | extendyourreliability[.]com | B-OX Device Code Phishing Domain |
| Domain | eurosignaltrust[.]com | B-OX Device Code Phishing Domain |
| Domain | consistentdigital[.]com | B-OX Device Code Phishing Domain |
| Domain | uninterruptedperformen[.]com | B-OX Device Code Phishing Domain |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.