TeamPCP Hackers Steal Cloud & Developer Credentials via
The TeamPCP hacking group has been observed actively abusing trusted development tools, specifically CI/CD pipelines, to facilitate the large-scale theft of developer and cloud credentials By...
The TeamPCP hacking group has been observed actively abusing trusted development tools, specifically CI/CD pipelines, to facilitate the large-scale theft of developer and cloud credentials
By slipping malicious code into popular CI/CD components, the group has shown how easily attacker controlled logic can blend into normal build and release activity.
The result is a campaign that focuses less on breaking into laptops and more on draining the secrets that power modern cloud and software pipelines.
Trend Micro said in a report shared with Cyber Security News (CSN) that this activity has already unfolded in at least seven distinct waves across March and April 2024.
In two of the most recent cases, TeamPCP compromised Checkmarx KICS and the popular Python package elementary data as part of a broader supply chain campaign.
In both incidents, the attackers poisoned official Docker images, code extensions, and GitHub Actions workflows so that the victim pipelines would pull and run their stealer payloads as if they were routine components.
Researchers from Trend Micro identified how these operations reached the same outcome stealing developer and cloud credentials at scale even though the technical paths were different.
The core idea is stark: every trusted build step and release job becomes a potential exfiltration stage once a single control point is compromised.
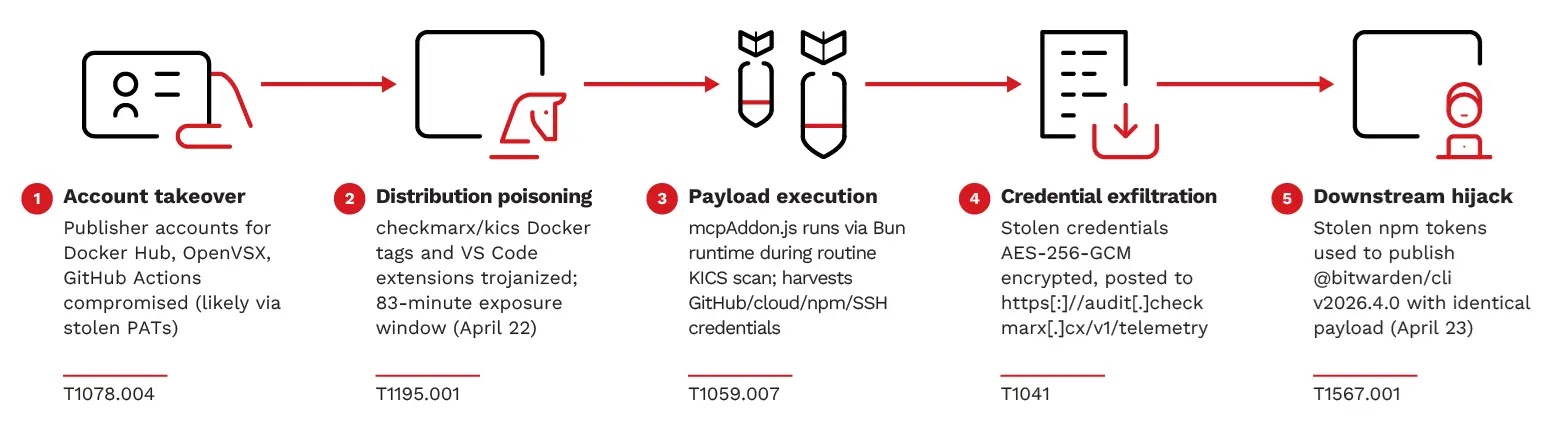
In the KICS incident, this meant multichannel poisoning across Docker Hub, VS Code extensions, OpenVSX, and GitHub Actions, followed by a downstream hijack of the Bitwarden CLI using stolen tokens.
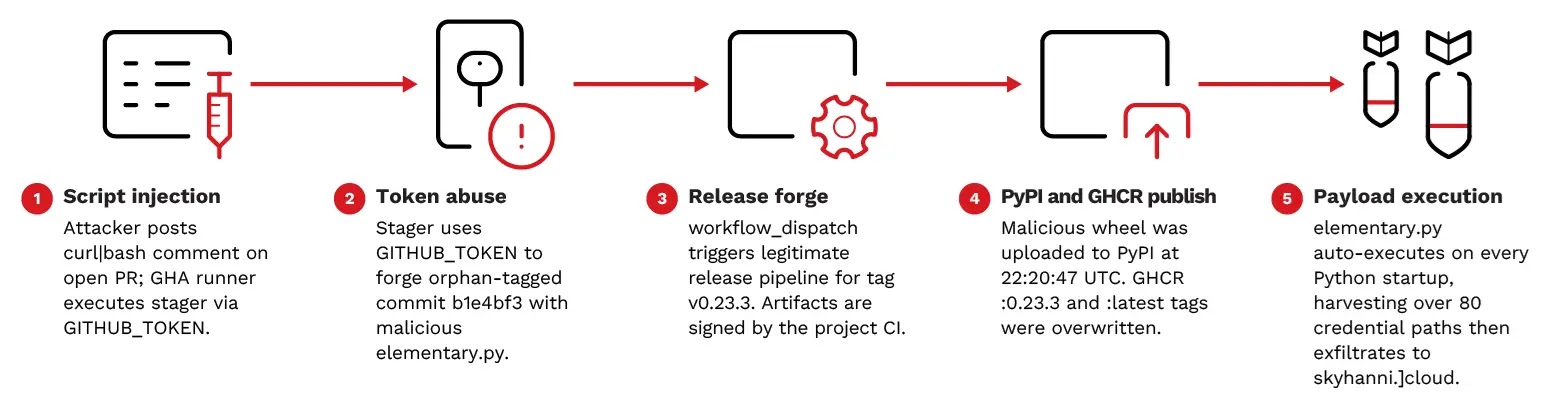
In the elementary data case, a single unsanitized pull request comment was enough to turn the project’s own release pipeline into an attacker operated signing and distribution channel.
Across both waves, the payloads went after a wide range of secrets: GitHub PATs, cloud keys, SSH material, Kubernetes secrets, database passwords, developer tooling tokens, and even cryptocurrency wallets.
In AWS environments, the stealer did not stop at files on disk, but also made live API calls to Secrets Manager and SSM Parameter Store, which let it dump managed secrets that never existed locally.
This combination of deep credential coverage and supply chain reach makes the campaign especially dangerous for organizations that rely heavily on cloud native CI/CD runners.

Here’s the TeamPCP campaign timeline, from the first GitHub Actions compromises in March through the later elementary data script injection in mid April.
This walk through the multi channel KICS infection chain and the elementary data compromise path, illustrating how trusted infrastructure did most of the work once the attackers had a foothold.
TeamPCP Hackers Abuse CI/CD Pipelines
Trend Micro tracks TeamPCP as a financially motivated cluster it also refers to internally as SHADOW WATER, linking multiple supply chain incidents through shared infrastructure, tooling, and operator markers.
In public telemetry, the group has even posted under a TeamPCP themed persona tying earlier compromises together with the same branding seen inside payload headers and archive names.
Stolen credentials have since surfaced in extortion activity, with a ransomware group publishing victims and data attributed to TeamPCP within weeks of collection.
In the KICS campaign, the attackers pushed malicious images to the official Checkmarx KICS Docker Hub repository while also poisoning related VS Code and OpenVSX extensions and modifying the project’s GitHub Actions workflow.
The poisoned artifacts downloaded a JavaScript stealer module that ran on top of the Bun runtime during what looked like a normal KICS scan.
That payload harvested GitHub tokens, cloud credentials, SSH keys, configuration files, and shell history, then exfiltrated them over HTTPS to attacker controlled command and control infrastructure.
Within roughly 48 hours of the initial KICS exposure window, the same stolen tokens allowed TeamPCP to publish a malicious Bitwarden CLI release that extended their reach to any developer or CI environment that installed it.
The Bitwarden variant reused the same command and control domain, encryption approach, and even fallback recovery behavior through GitHub commit search.
Trend Micro associates these overlaps with a single campaign, reinforced by Dune themed staging repositories and the recurring “Long Live The Resistance Against Machines” commit message marker across waves.
The elementary data incident followed a simpler but in some ways more worrying pattern. An attacker controlled account posted a crafted comment to a public pull request in the GitHub repository, which flowed straight into a GitHub Actions workflow step that interpolated event data into a shell command without sanitization.
That comment injected a script which abused the runner’s GitHub token to forge a tagged release commit and trigger the project’s own signing pipeline, producing a malicious wheel that the maintainers’ CI signed and uploaded to PyPI and GitHub Container Registry as if it were legitimate.
Once installed, the elementary data package relied on a Python pth based loader that executes whenever the interpreter starts, even in processes that never import the package.
The inner stealer was written in pure Python, avoiding obvious malware patterns and leaving few artifacts on disk, and it focused heavily on cloud and Kubernetes secrets in addition to local keys and tokens.
Exfiltration again used HTTPS with attacker branded headers and a Cloudflare fronted endpoint, followed by rapid rotation of the infrastructure once the operation concluded.
Protecting pipelines from trusted abuse
Trend Micro’s analysis stresses that every entry point in the TeamPCP campaign exploited implicit trust in CI/CD: trusted Docker tags, known publishers in extension marketplaces, and project owned signing pipelines.
The researchers recommend enforcing the principle of least privilege so that a single compromised workflow or artifact cannot access more secrets than its role truly requires. They also highlight the value of network egress controls around CI runners, which would have blocked exfiltration even if poisoning succeeded.
For organizations that pulled affected Checkmarx KICS Docker tags or installed the specific VS Code extensions and Bitwarden CLI versions, Trend Micro advises treating those environments as fully compromised.
Teams should rotate GitHub PATs, cloud IAM keys, Azure and GCP credentials, Kubernetes service account tokens, SSH keys, and any secrets stored in environment variables or standard credential files like aws credentials and git credential stores.
Upgrading to safe versions of KICS images and extensions, verifying image digests, and auditing GitHub Actions logs for suspicious format check jobs are also key steps.
The same response model applies to hosts and runners that installed elementary data during its malicious window.
Any host that pulled the tainted PyPI or container image should be assumed compromised, with priority rotation focused on cloud access keys, service account keys, Azure credentials, Kubernetes tokens, GitHub tokens, Vault tokens, npm and PyPI credentials, and any cryptocurrency wallets present on disk.
Incident responders should also search for the persistence marker file under the system temp directory, oversized elementary data pth files in Python site packages, and outbound connections to documented command and control and staging domains.
Longer term, the report urges development and security teams to audit GitHub Actions workflows for user controlled expressions interpolated straight into shell commands, and to pin all Docker image pulls to verified digests instead of mutable tags.
Trend Micro notes that neither payload would have succeeded in exfiltrating data from a CI runner with outbound HTTPS restricted to an allowlist of known endpoints and cloud services.
In other words, hardening the structure of pipelines and their network paths may matter more than chasing the next variant of the stealer itself.
Indicators of Compromise:-
| Type | Indicator | Description |
|---|---|---|
| URL | https://www.trendmicro.com/en_us/research/26/e/analyzing-teampcp-supply-chain-attacks.html | Trend Micro public report containing full IoC set referenced in this article |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.