Chinese APT Exploits Microsoft Exchange to Breach Energy Networks
Chinese state-linked hacking group FamousSparrow has successfully breached an Azerbaijani oil and gas company, according to a detailed security report. The group exploited an unpatched Microsoft...
Chinese state-linked hacking group FamousSparrow has successfully breached an Azerbaijani oil and gas company, according to a detailed security report. The group exploited an unpatched Microsoft Exchange server, deploying multiple backdoors deep within the network. This incident highlights ongoing threats to critical energy infrastructure, as outlined in the full analysis.
The attack ran from late December 2025 through late February 2026 and stands as one of the most detailed Chinese APT intrusions targeting energy infrastructure in the South Caucasus ever documented.
The threat group did not stop at one attempt. Attackers returned to the same compromised Exchange server three separate times, swapping malware families between visits and adjusting their tactics each time defenders tried to remove them.
That persistence signals a deliberate, sustained espionage campaign rather than an opportunistic breach.
Researchers at Bitdefender, who tracked the operation across all three activity waves, attributed the intrusion to FamousSparrow with moderate-to-high confidence, noting significant overlap with the Earth Estries threat cluster.
The timing is no coincidence. Azerbaijan has grown into a critical gas supplier for Europe after Russia’s Ukraine transit deal expired in 2024 and Strait of Hormuz disruptions in early 2026 reduced alternative energy sources.
Chinese APT Hackers Exploit Microsoft Exchange
The operation deployed two distinct backdoor families, Deed RAT and Terndoor, across different stages. Attackers also introduced an evolved DLL sideloading technique engineered to defeat automated security analysis, a level of sophistication rarely seen in prior campaigns tied to these malware families.
What followed was a layered operation that expanded analyst understanding of this group’s reach into energy targets.
The earliest signs of the intrusion date to December 25, 2025, when the Microsoft Exchange IIS worker process attempted to write a web shell into a publicly accessible directory on the server.
This action leveraged the ProxyNotShell exploit chain, two vulnerabilities tracked as CVE-2022-41040 and CVE-2022-41082 that allow unauthenticated remote code execution on unpatched Exchange servers.
In the days that followed, attackers dropped additional web shells with filenames such as key.aspx, log.aspx, errorFE_.aspx, and signout_.aspx. These provided a reliable foothold for issuing commands and staging further payloads.
A three-component malware chain was then deployed using files disguised as the legitimate LogMeIn Hamachi VPN application to reduce suspicion.
The loader file, LMIGuardianDll.dll, was placed alongside a genuine LogMeIn binary and sideloaded during normal startup. The Deed RAT payload was stored in an encrypted file named .hamachi.lng, decrypted in memory using AES-128 and RC4.
A Windows service mimicking LogMeIn Hamachi was also created to auto-launch the malware on every restart, locking in persistent access.
Advanced Evasion and Multi-Wave Persistence
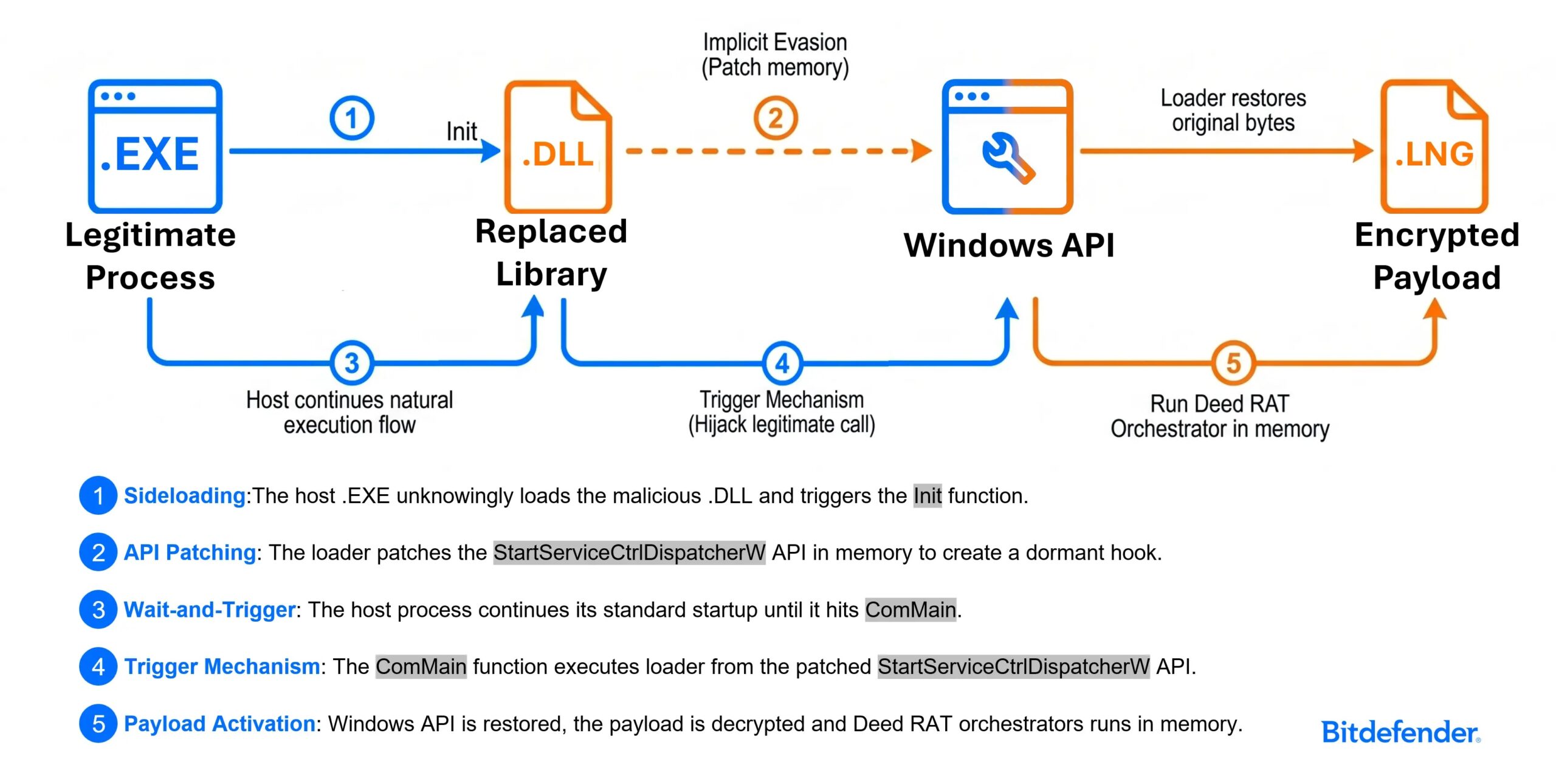
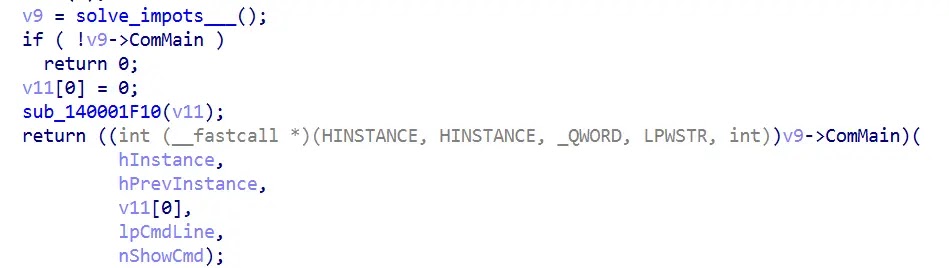
What sets this campaign apart is the evolved DLL sideloading technique used to hide the Deed RAT loader. Unlike typical sideloading that triggers malicious code the moment a DLL is loaded, this version split its logic across two export functions named Init and ComMain.
The payload only runs after the host application follows a specific internal sequence of calls, meaning a sandbox examining the file in isolation sees no malicious behavior at all.
This design gates the infection behind a legitimate execution path. Security tools that inspect only portions of code find nothing to flag, and the full attack behavior is only visible when the application runs exactly as expected. That makes this sample significantly harder to detect during automated triage.
In the second wave, the group deployed a backdoor called Terndoor by hijacking the legitimate deskband_injector64.exe binary. The attempt was blocked, but forensic artifacts confirmed the malware had tried to install a kernel driver.
The third wave brought back a modified Deed RAT using sentinelonepro[.]com as its command-and-control address, impersonating a well-known security vendor to avoid detection in network logs.
Security teams should apply all available Exchange patches and rotate any exposed credentials without delay.
Monitoring should cover web shell writes through the IIS worker process, unsigned binaries patching Windows API functions in memory, and outbound HTTPS traffic to domains impersonating security vendors.
Unexpected RDP sessions using domain administrator accounts, followed quickly by PowerShell activity and new file downloads, should be treated as high-priority alerts.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| MD5 Hash | 0554f3b69d39d175dd110d765c11347a | LMIGuardianSvc.exe — legitimate LogMeIn Hamachi binary used in Wave 1 sideloading chain |
| MD5 Hash | 762f787534a891eca8aa9b41330b4108 | USOShared.exe — renamed copy of deskband_injector64.exe used in Wave 2 |
| File Name | LMIGuardianDll.dll | Malicious DLL loader sideloaded by LMIGuardianSvc.exe; deploys Deed RAT |
| File Name | .hamachi.lng | Encrypted Deed RAT payload, AES-128 + RC4 decrypted in memory |
| File Name | lmiguardiandll.dll | Alternate-casing malicious loader variant observed in initial Exchange exploitation stage |
| File Name | key.aspx | Web shell dropped via ProxyNotShell exploit on Exchange server |
| File Name | log.aspx | Web shell dropped via ProxyNotShell exploit on Exchange server |
| File Name | errorFE_.aspx | Web shell dropped via ProxyNotShell exploit on Exchange server |
| File Name | signout_.aspx | Web shell dropped via ProxyNotShell exploit on Exchange server |
| File Name | winmm.dll | Malicious loader DLL used in Wave 2 Terndoor sideloading chain |
| File Name | vmflt.sys | Driver that Terndoor malware attempted to install for kernel-level persistence |
| File Name | cache.dat | Assessed payload container associated with Terndoor deployment |
| Registry Key | HKLMSYSTEMControlSet001Servicesvmflt | Registry entries created by Terndoor to register kernel driver service |
| Domain (C2) | virusblocker[.]it[.]com:443 | Command-and-control address used by Wave 1 Deed RAT variant |
| Domain (C2) | sentinelonepro[.]com:443 | Command-and-control address used by Wave 3 modified Deed RAT variant |
| Domain | ipinfo[.]io | Legitimate service contacted by Wave 2 malware for network reconnaissance |
| CVE | CVE-2022-41040 | ProxyNotShell Exchange vulnerability exploited for initial access |
| CVE | CVE-2022-41082 | ProxyNotShell Exchange vulnerability exploited for initial access |
| Magic Value | 0xFF66ABCD | Updated Deed RAT module magic value (replaces 0xDEED4554 in older variants) |
| File Path | C:Recovery | File storage path used by Wave 3 Deed RAT components |
| File Path | C:ProgramDataUSOShared | File storage path used by Wave 2 Terndoor components |
| File Path | C:TEMPLMIGuardianSvc.exe | Initial staging path for Wave 1 Deed RAT loader |
| File Path | C:Program Files (x86)LogMeIn Hamachi | Final installation path mimicking legitimate LogMeIn Hamachi software |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.