Amazon Bug Exposed AI Chat Agents Via Custom Permissions
A critical security flaw recently uncovered effectively left sensitive organizational data exposed, much like a vault door standing robustly in place but lacking its essential locking mechanism....
A critical security flaw recently uncovered effectively left sensitive organizational data exposed, much like a vault door standing robustly in place but lacking its essential locking mechanism.
Security researchers at Fog Security recently uncovered a severe authorization bypass in Amazon Quick’s AI Chat Agents.
This vulnerability allowed blocked users to interact freely with enterprise AI tools, despite explicit administrative restrictions.
Compounding the issue, AWS silently patched the flaw without notifying customers or issuing a public advisory, categorizing the risk severity as “none.”
Amazon Quick Bug Exposed
The vulnerability stems from a classic architectural failure: missing server-side authorization (CWE-862).
Access to Amazon Quick, AWS’s business intelligence service, differs from that of standard cloud resources.
Administrators cannot use standard AWS Identity and Access Management (IAM) policies or Service Control Policies (SCPs) to govern the AI chatbot.
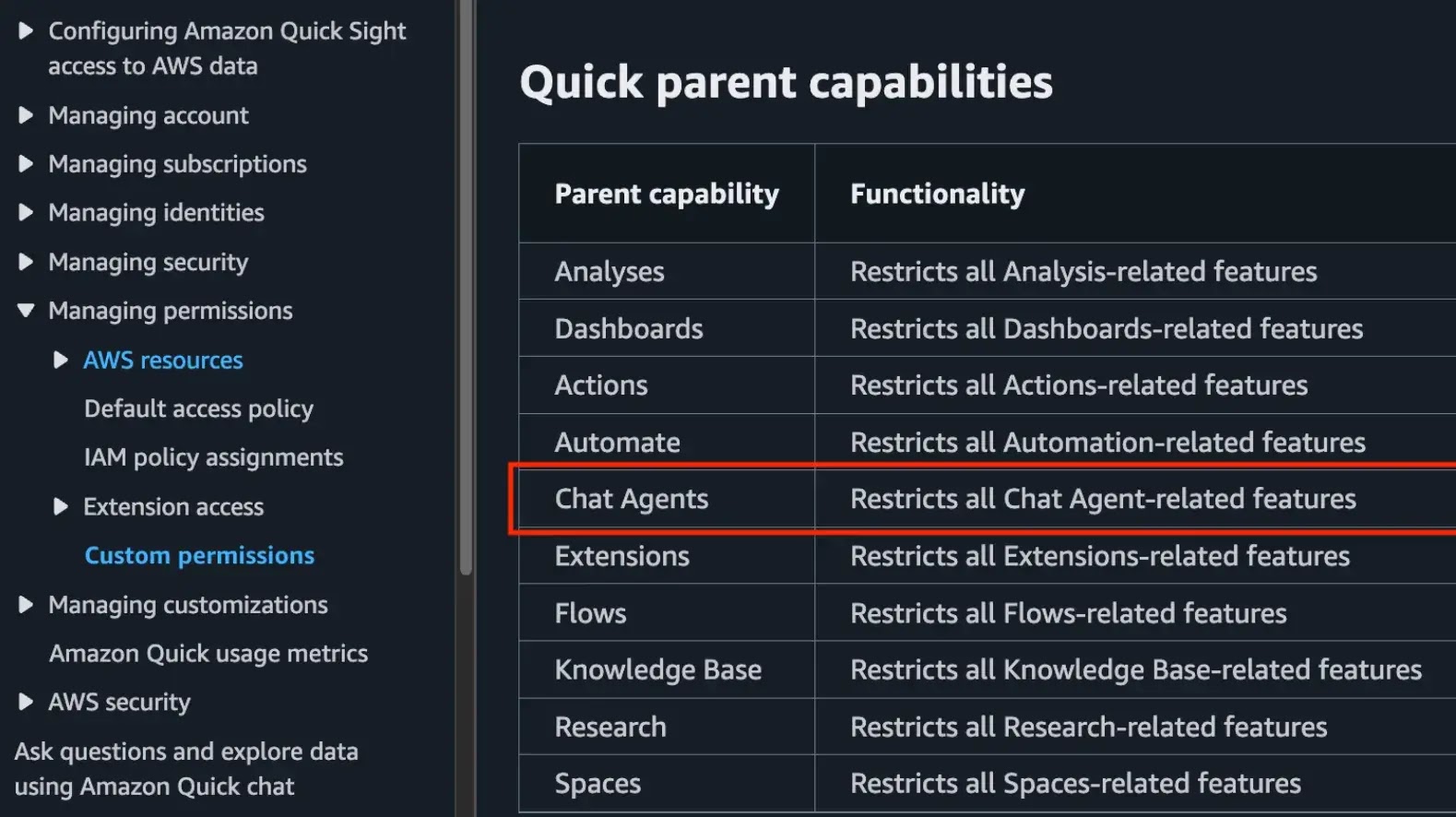
Instead, they must rely entirely on custom permission profiles to restrict granular Access.
While the Amazon Quick user interface properly respected these custom permissions by hiding the chat feature, the backend API completely failed to verify them.
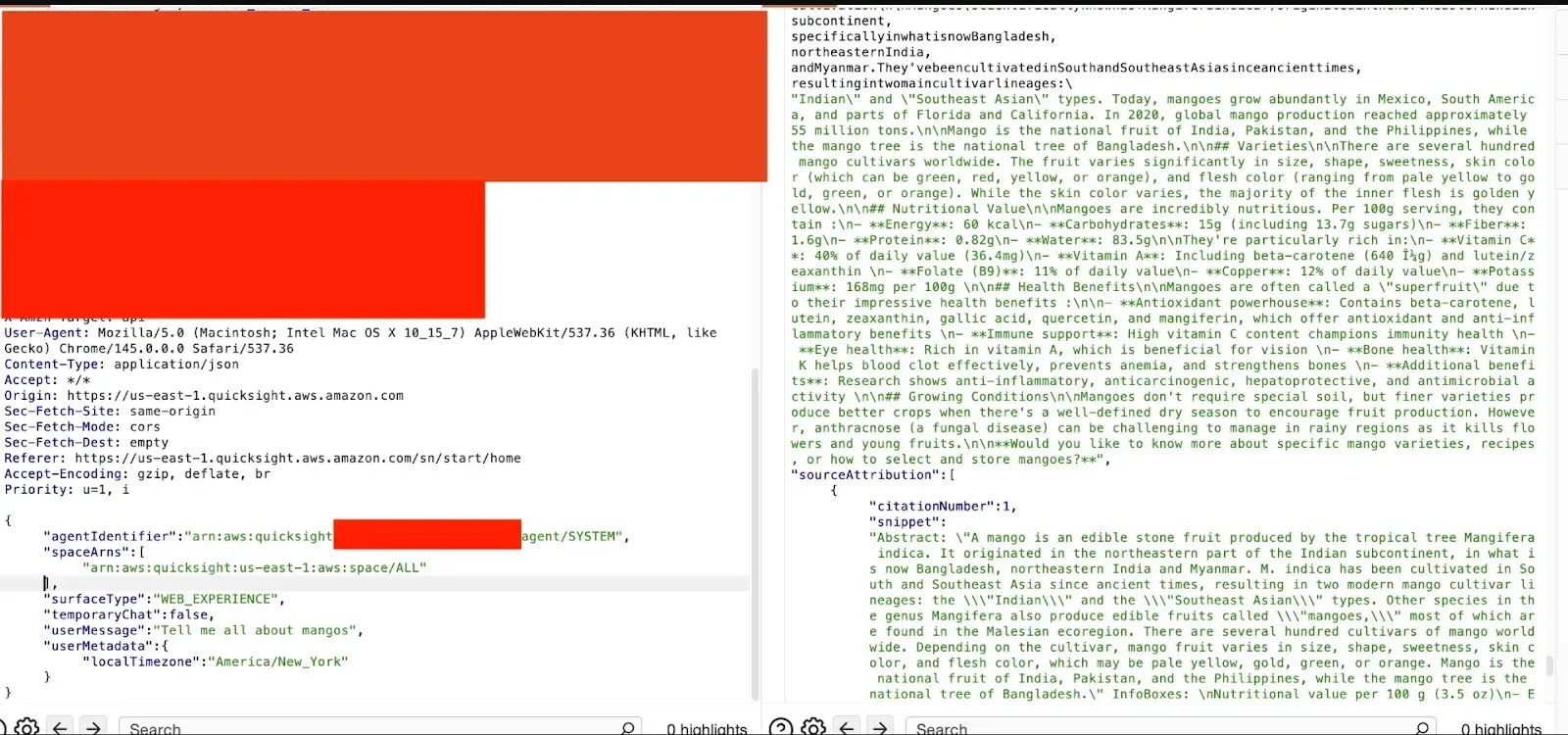
Researchers applied organization-wide blocks on all AI features and then logged in as a restricted user.
By intercepting network traffic and sending direct HTTP API requests, they successfully queried the bot.
A simple, unauthorized prompt asking the agent to “Tell me about mangoes” returned a successful response instead of the expected Access Denied error.
This flaw created a significant blind spot for enterprise security teams trying to control unauthorized shadow AI usage.
AWS automatically provisions a default chat agent when Amazon Quick is activated in an environment.
Because the platform deeply integrates with corporate data sources such as CRMs, databases, and communication tools, organizations often mandate strict controls on which employees can use AI analytics.
Administrators believed they had disabled the feature, but the backdoor API access remained wide open.
While the researchers confirmed that the vulnerability did not permit cross-tenant data exposure, it thoroughly compromised intra-account security boundaries.
Internal users could interact with the AI model unchecked, bypassing the very controls relied upon for access management and strict corporate compliance enforcement.
Fog Security disclosed the vulnerability to AWS via their HackerOne vulnerability disclosure program on March 4, 2026.
The cloud provider acted quickly, deploying an initial patch to select regions by March 11 and completely fixing all production environments the following day.
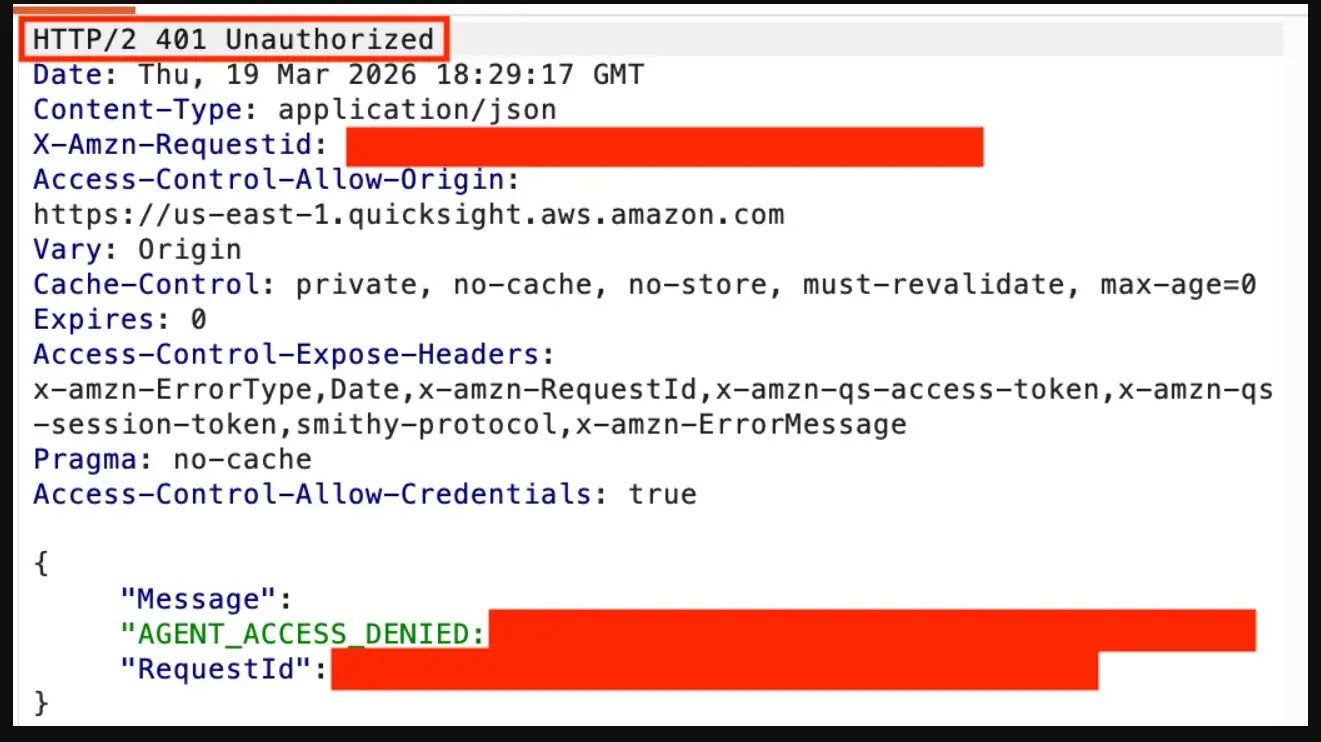
When restricted users attempt the same API bypass today, the server correctly issues a 401 Unauthorized response.
Despite the rapid patch deployment, the lack of transparency has alarmed security professionals.
AWS classified the vulnerability’s impact as “none” and bypassed their standard public communication protocols.
This gap between the published scope of vulnerability reporting and actual communication leaves organizations unaware of their historical exposure to internal AI use.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.