Hackers Use PlugX DLL Sideloading in PlugX-Like Chain
Cybercriminals are deploying increasingly sophisticated tactics to distribute malware, as evidenced by a new campaign detailed in a recent report. This campaign, which raises serious concerns,...
Cybercriminals are deploying increasingly sophisticated tactics to distribute malware, as evidenced by a new campaign detailed in a recent report. This campaign, which raises serious concerns, leverages a fake version of Anthropic’s Claude AI assistant to lure victims into downloading malicious software. A full analysis of this threat is available for review here:
![The claude-pro[.]com front page (Source - Sophos)](https://hackersradar.com/wp-content/uploads/2026/05/content_1778515229_8984.jpg)
Researchers from Sophos X-Ops identified the campaign after investigating reports of the fake Claude website actively distributing malware. While the attack chain initially looked like a classic PlugX operation, a closer look revealed something unexpected beneath the surface. The team uncovered a previously undocumented backdoor they have named “Beagle,” alongside a first-stage loader known as DonutLoader.
The campaign appears to be spreading through malvertising, where attackers pay to place malicious links in search engine ads and sponsored results. Unsuspecting users searching for the Claude AI tool could easily land on the fake site without realizing anything is wrong. Threat actors may have also used SEO poisoning to further boost the site’s visibility in organic search results.
Hackers Use PlugX-Like DLL Sideloading Chain
What makes this campaign especially notable is how it blends older, well-documented attack methods with a freshly crafted payload. The reuse of a shared XOR key across multiple samples from earlier in 2026 suggests this is not a one-off effort. Related samples show different payloads and infection chains, pointing to ongoing development spread over several months.
![A website that may be linked to the threat actor behind claude-pro[.]com (Source - Sophos)](https://hackersradar.com/wp-content/uploads/2026/05/content_1778515233_1549.jpg)
The infection begins once the user runs the Claude.msi installer, which drops three files: NOVupdate.exe, NOVupdate.exe.dat, and avk.dll. NOVupdate.exe is a legitimate, signed updater from G DATA antivirus, but the attackers swap out the real avk.dll with a malicious version, tricking the trusted executable into loading it. This technique, known as DLL sideloading, is a hallmark of PlugX campaigns dating back over a decade.
The malicious DLL decrypts the payload hidden inside NOVupdate.exe.dat using a hardcoded XOR key and runs the result entirely in memory. This in-memory approach makes detection much harder for traditional security tools. The decrypted content turns out to be DonutLoader shellcode, an open-source loader previously linked to sophisticated attacks on government organizations.
This combination of a signed legitimate binary, a sideloaded malicious DLL, and an encrypted data file closely mirrors known PlugX attack setups. However, despite the nearly identical structure, the final payload here is not PlugX. It opens the door to a different and newly identified threat entirely.
Beagle Backdoor and C2 Infrastructure
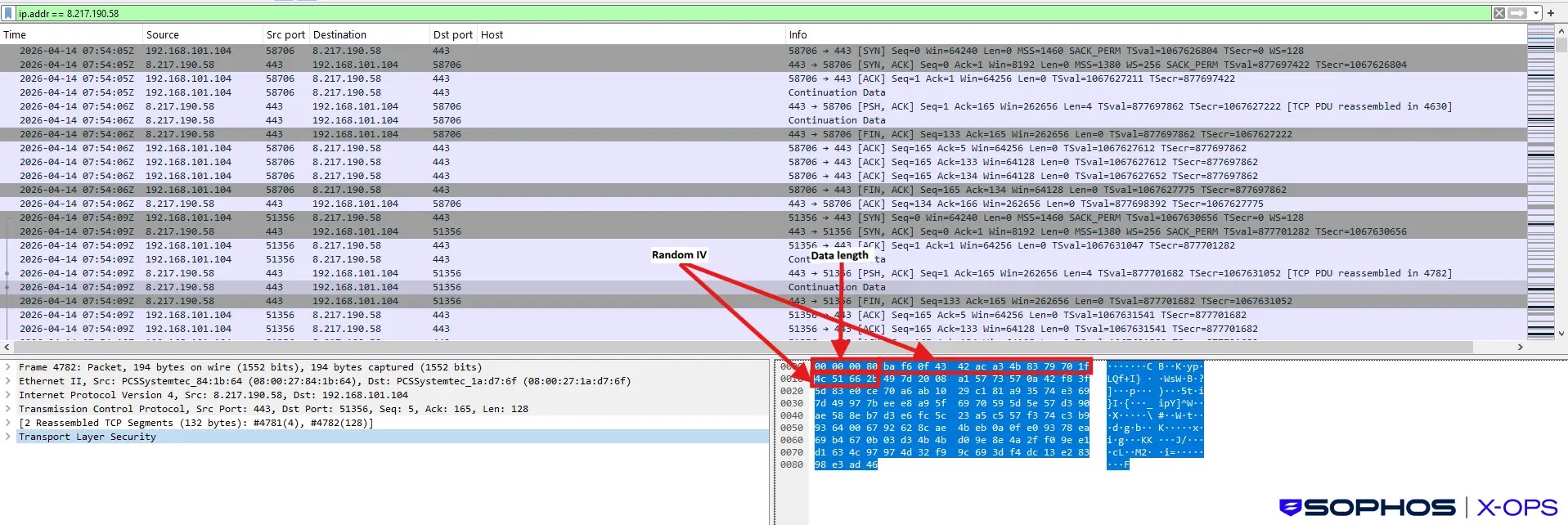
Once DonutLoader executes, it delivers the final payload: the Beagle backdoor. Beagle connects to a command-and-control server at license[.]claude-pro[.]com (IP: 8.217.190.58) over TCP port 443 and UDP port 8080, using a hardcoded AES key to encrypt all traffic. Through this connection, an attacker can upload and download files, run commands, manage directories, and maintain persistent access on the compromised machine.
Sophos researchers also found related samples on VirusTotal dating back to February 2026. One variant used a Microsoft Defender utility as the trusted host binary, while a March 2026 sample led to the deployment of AdaptixC2, an open-source red team framework tied to ransomware activity. These findings suggest the underlying infrastructure may be serving multiple campaigns or threat actors simultaneously.
To stay protected, users should only download Claude from the official Anthropic website and avoid clicking on sponsored search result links. Checking startup folders for the files NOVupdate.exe, avk.dll, and NOVupdate.exe.dat is a practical first step for anyone who may have visited the fake site. Monitoring outbound connections to claude-pro[.]com and license[.]claude-pro[.]com is also strongly advised.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| Domain | claude-pro[.]com | Fake Claude AI website used for malware distribution |
| Domain | license[.]claude-pro[.]com | Command-and-control (C2) server domain |
| IP Address | 209.189.190.206 | Possible hosting server (CloudFlare origin, set up March 2026) |
| IP Address | 178.128.108.89 | Second linked hosting server |
| Domain | vertextrust-advisors[.]com | Domain linked to a secondary hosting server associated with the threat actor |
| IP Address | 8.217.190.58 | IP address associated with C2 domain license[.]claude-pro[.]com |
| File Name | Claude-Pro-windows-x64.zip | Malicious ZIP archive (~505MB) distributed via fake site |
| File Name | Claude.msi | Windows installer contained within the malicious ZIP archive |
| File Name | NOVupdate.exe | Legitimate G DATA signed executable used in DLL sideloading |
| File Name | avk.dll | Malicious DLL sideloaded to replace the legitimate G DATA DLL |
| File Name | NOVupdate.exe.dat | Encrypted data file containing the DonutLoader shellcode payload |
| Encryption Key (XOR) | SGkGHumNrDbt1OEHV3y2dVh5bQby2R | XOR decryption key used to decrypt the first-stage shellcode |
| Encryption Key (AES) | beagle_default_secret_key_12345! | Hardcoded AES key used by the Beagle backdoor for C2 communications |
| Domain | gouvvbo[.]top | C2 server used by March 2026 variant sample |
| Domain | update-treix[.]com | C2 domain used by GoddTV.msi sample |
| Domain | update-crowdstrike[.]com | Domain hosted on same IP as update-treix[.]com (192.252.186.62) |
| Domain | update-sentinelone[.]com | Domain hosted on same IP as update-treix[.]com (192.252.186.62) |
| IP Address | 192.252.186.62 | Shared IP hosting update-treix[.]com and thematically linked domains |
| File Name | MpCopyAccelerator.exe | Legitimate Microsoft Defender utility used in February 2026 variant |
| File Name | MpClient.dll | Malicious sideloaded DLL in February 2026 variant |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.