Hackers Deploy Modular RAT for Credential Theft With Screenshot
A recently uncovered malware campaign is actively targeting senior executives and government investigators across Southeast Asia. This operation leverages a modular Remote Access Trojan (RAT)...
A recently uncovered malware campaign is actively targeting senior executives and government investigators across Southeast Asia. This operation leverages a modular Remote Access Trojan (RAT) designed to steal credentials, capture screenshots, and establish deep persistence on compromised systems. For a detailed technical analysis of this threat, refer to the
What makes this threat especially alarming is how it reaches victims. Attackers are not guessing or fabricating stories. In one case, they harvested real legal documents from an ongoing data breach lawsuit, including signed police reports, corporate admission letters, and personal medical records.
Victims who opened the archive received a completely authentic document on screen, with no sign that anything had gone wrong behind the scenes.
Researchers at Seqrite Labs identified and named the campaign, noting that the entire system compromise completes in under 10 seconds with zero visible indicators to the victim. The malware arrives inside a nested compressed archive delivered through a targeted spear phishing email, and its infection chain is engineered to bypass most conventional security tools.
The operation targets two groups simultaneously. The first campaign focuses on senior executives at Viettel Group, Vietnam’s largest telecom operator running under the Ministry of National Defence, as well as cybercrime investigators from Thanh Hoa Provincial Police.
The second targets compliance and audit staff at St. Luke’s Medical Center in the Philippines, using a fabricated whistleblower complaint that invokes alleged financial fraud and accreditation violations worth over PHP 1.5 million.
Both campaigns use the same underlying infrastructure and payload, confirming a single threat actor running a coordinated, modular attack operation across two countries at the same time.
Modular RAT With Credential Theft and Screenshot Capture
At the technical core of this campaign sits a sophisticated modular RAT acting as a multi-purpose implant. Once loaded into memory through a layered execution chain, it harvests credentials from web browsers including Chrome’s stored login data, cookies, and history. It also targets FTP client configurations, remote access tools like Sunlogin and ToDesk, and SSH session files from Xshell, making it a serious threat to anyone who manages privileged system access.
The screenshot capture module retrieves full screen dimensions, accounts for multi-monitor setups, and dynamically adjusts image resolution based on network conditions before transmitting a reconstructed BMP image to the attacker’s command-and-control server. The malware also scans all running processes to build a profile of installed security products, then adjusts its behavior accordingly to reduce detection.
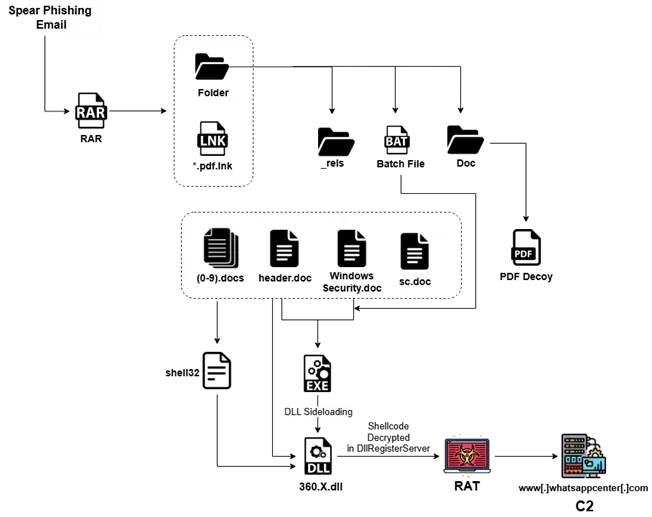
The payload is never stored as a complete file inside the archive. Binary chunks disguised as ordinary document files are assembled at runtime using Windows’ native copy command, and a time-based mechanism randomizes the payload hash on every execution to defeat signature-based scanning. The final executable is then injected into a trusted Windows process, making it appear as normal system activity to most forensic tools.
Infrastructure, Attribution, and Defensive Measures
The malware communicates with a hardcoded command-and-control domain, whatsappcenter[.]com, hosted on IP address 38[.]54[.]122[.]188. This server sits within KAOPU-HK, a Hong Kong-based network with a documented history of providing abuse-resistant hosting to threat actors across Asia-Pacific. Passive intelligence tags the host as bulletproof infrastructure, a strong indicator of deliberate operational security.
Seqrite researchers assess with moderate-to-high confidence that this campaign is linked to a China-nexus threat cluster. Supporting indicators include the use of bulletproof Chinese hosting, an embedded security detection list that enumerates vendors such as 360Safe, Qianxin, and Sangfor, direct targeting of WeChat data within the credential harvesting module, and a broader Southeast Asian footprint spanning military telecom and healthcare.
Organizations in telecom, government, and healthcare across Southeast Asia should treat this as an active and evolving threat. Security teams are advised to block the known C2 domain and IP, monitor for LNK file executions that invoke ftp.exe, flag any process dropping chunked doc files into the Public directory, and audit systems for signs of explorer.exe being respawned under a restricted security context. Because this attack weaponizes genuine legal documents and trusted system binaries, standard user awareness training alone will not stop it.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| File Hash (SHA256) | 35af2cf5494181920b8624c7b719d39590e2a5ff5eaa1a2fa1ba86b2b5aa9b43 | LNK dropper — Viettel-themed lure (Campaign 1) |
| File Hash (SHA256) | bc090d75f51c293d916c40d4b21094faaec191a42d97448c92d264875bf1f17b | LNK dropper — Whistleblowing_Report_SLMC lure (Campaign 2) |
| File Hash (SHA256) | 197f11a7b0003aa7da58a3302cfa2a96a670de91d39ddebc7a51ac1d9404a7e6 | LNK — Philippine National ID decoy file |
| File Hash (SHA256) | f34f550147c2792c1ff2a003d15be89e5573f0896c5aa6126068baa4621ef416 | LNK — iPad_Pro_Display_Spec_Final_CONFIDENTIAL.docx decoy |
| File Hash (SHA256) | bc83817c6d2bf8df1d58eac946a12b5e2566b2ffe15cf96f37c711c4b755512b | 360.8.dll — multi-stage shellcode loader |
| File Hash (SHA256) | 61e9d76f07334843df561fe4bac449fb6fdaed5e5eb91480bded225f3d265c5f | th5znehec.exe — malicious executable |
| File Hash (SHA256) | ee6330870087f66a237a7f7c115b65beb042299f12eae1e9004e016686d0c387 | a.dll — malicious DLL component |
| File Hash (SHA256) | 91a15554ec9e49c00c5ca301f276bd79d346968651d54204743a08a3ca8a5067 | SlULIRDJOiq — unnamed payload artifact |
| File Hash (SHA256) | a49155df50963d2412534090bbd967749268bd013881ddb81d78b87f91cdc15b | Batch script — payload assembly (variant 1) |
| File Hash (SHA256) | 7f80add94ee8107a79c87a9b4ccbd33e39eccd1596748a5b88629dd6ac11b86d | Batch script — payload assembly (variant 2) |
| Domain | whatsappcenter[.]com | C2 domain masquerading as legitimate service |
| IP Address | 38[.]54[.]122[.]188 | C2 server hosted on KAOPU-HK bulletproof infrastructure |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.