RansomHouse Claims Access to Trellix Source Code Breach Parts
Global cybersecurity firm Trellix, formed from the merger of McAfee Enterprise and FireEye, has confirmed unauthorized access to a portion of its source code repository. The RansomHouse ransomware...
Global cybersecurity firm Trellix, formed from the merger of McAfee Enterprise and FireEye, has confirmed unauthorized access to a portion of its source code repository. The RansomHouse ransomware group formally claimed responsibility for the attack.
Trellix reported a data breach involving unauthorized access to a portion of its source code repository, which was disclosed publicly around May 2, 2026.
Upon discovering the intrusion, Trellix immediately engaged leading forensic experts to investigate and has notified law enforcement authorities.
In an official statement published on its website, the company said: “Based on our investigation to date, we have found no evidence that our source code release or distribution process was affected, or that our source code has been exploited”.
The RansomHouse ransomware group formally named Trellix on its dark web leak site, claiming the compromise occurred on April 17, 2026.
The group published multiple screenshots reportedly demonstrating access to Trellix’s internal services and management dashboards, though they have not specified the volume of data exfiltrated or its nature.
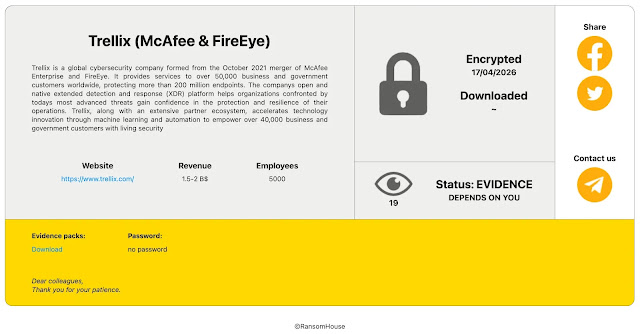
Notably, RansomHouse listed the breach status as “Evidence Depends on You,” a hallmark tactic used to pressure victims into negotiations before releasing stolen data publicly.
RansomHouse is a sophisticated ransomware-as-a-service (RaaS) group known for deploying a unique ransomware variant called Mario ESXi, whose code shares lineage with the leaked Babuk ransomware source code, alongside a tool called MrAgent to target both Windows and Linux-based virtualized environments.
The group typically targets VMware ESXi infrastructure and exploits weak domain credentials and monitoring systems to gain privileged access.
RansomHouse distinguishes itself by positioning itself as a “professional mediator community,” often seeking payment for data deletion rather than decryption.
The full extent of the data exposure remains unspecified, and Trellix has not confirmed whether corporate or customer data beyond source code was accessed.
Preliminary investigations indicate no evidence that the software distribution pipeline or customer-facing products were tampered with.
The incident highlights the growing trend of ransomware groups targeting cybersecurity vendors themselves, organizations whose proprietary source code, if weaponized, could have far-reaching consequences for enterprise defenses globally.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.