Salat Malware Uses QUIC & WebSocket for Stealth Channels Stealthy
Salat, a recently identified malware, is drawing significant concern within the cybersecurity community. Its sophisticated design and broad capabilities are notable. Developed in the Go programming...
Salat, a recently identified malware, is drawing significant concern within the cybersecurity community. Its sophisticated design and broad capabilities are notable. Developed in the Go programming language, Salat functions as a full remote access trojan (RAT), providing attackers with deep, persistent control over infected systems.
Unlike simpler tools that focus on one task, Salat is engineered to do everything from stealing passwords to giving attackers live visibility into a victim’s screen and webcam.
What makes Salat particularly concerning is how it manages communication with its operators. It uses modern protocols, specifically QUIC and WebSocket, to blend its traffic into normal internet activity, making it much harder for security tools to flag anything suspicious.
The malware is designed not just to attack a target but to remain completely hidden while doing so, which sets it apart from most known threats.
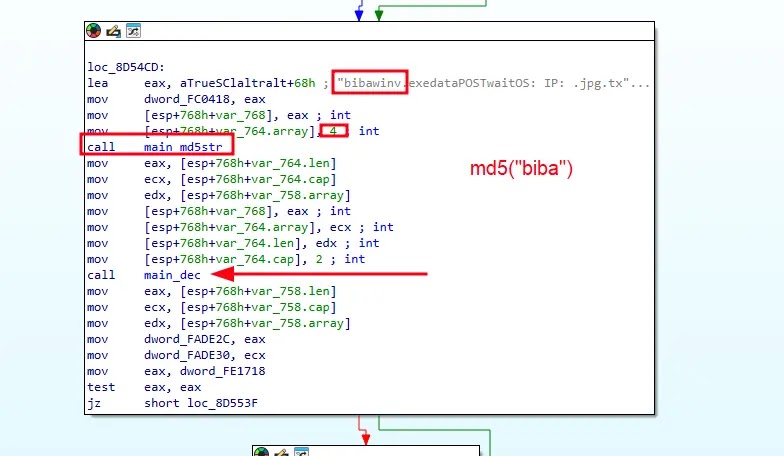
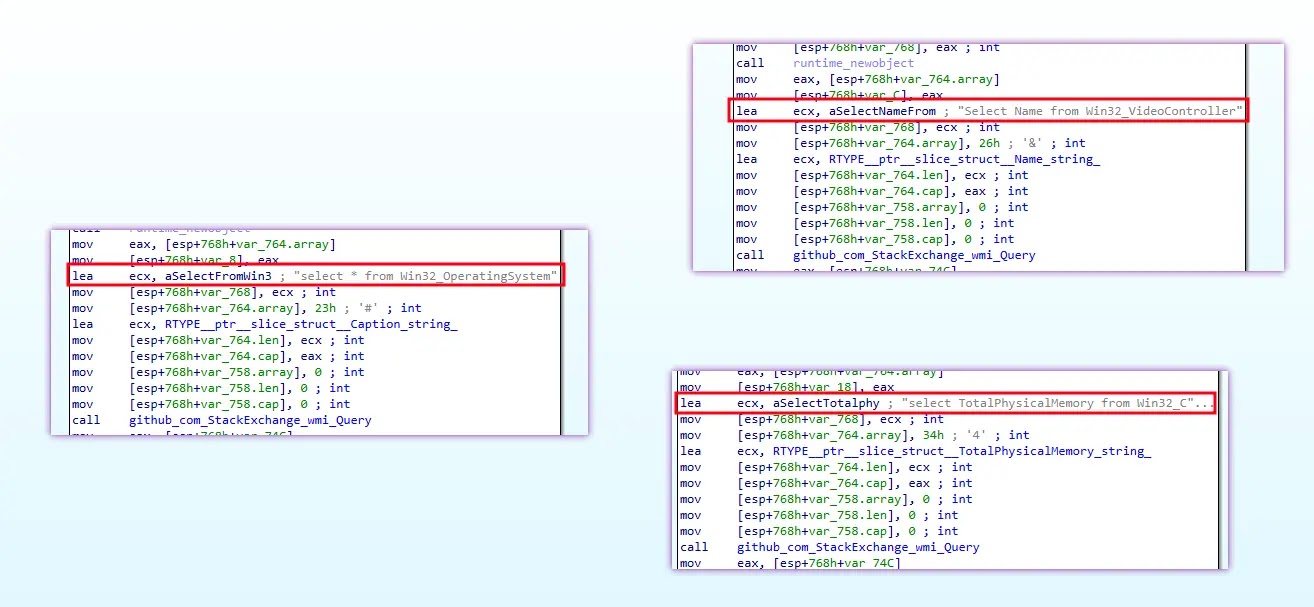
Researchers from DarkAtlas identified and analyzed the malware in detail, publishing their findings on May 6, 2026. The team noted that Salat reflects careful and professional planning, including six different methods for concealing its internal strings and a system that generates a unique identity for each infected machine based on the device’s hostname and hardware profile.
Once inside a system, Salat begins collecting information right away. It gathers details about the operating system, CPU, GPU, memory, and the application the user currently has open. All of this is packaged and sent to the attacker’s server in encrypted form, giving them a full and detailed picture of the machine they now control.
The malware’s reach extends to browsers, cryptocurrency wallets, messaging applications, and clipboard contents. It can record keystrokes, take screenshots, stream the desktop live, and open a remote shell for direct command execution. Salat essentially hands full operational control of an infected machine to whoever is running it from the other side.
QUIC and WebSocket for Silent Communication
Salat is engineered to select the best available method for talking to its command server, and it strongly favors QUIC and WebSocket channels above all others.
These protocols are widely used by legitimate web services, which helps the malware’s traffic blend naturally into everyday network activity. Only if both are unavailable does it fall back to standard HTTP/2.
The addresses of its command servers are stored in a doubly encrypted format inside the binary, making them very difficult to extract during analysis. Once decoded, five separate server addresses were recovered, all sharing the same path structure. If the malware fails to connect after five consecutive attempts, it automatically rotates to the next server on its list.
What is especially notable is Salat’s backup plan using the TON blockchain. If every hardcoded server becomes unreachable, the malware queries the TON network through Cloudflare’s encrypted DNS service to retrieve a fresh server address. This makes the malware nearly impossible to fully cut off, since the blockchain itself cannot simply be taken offline.
Data Theft and Persistence on Infected Machines
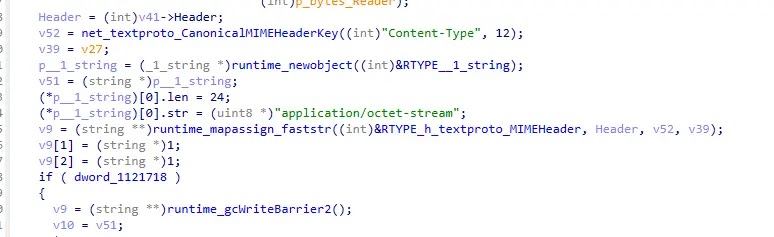
Salat’s ability to steal data goes well beyond most malware tools. It targets saved passwords and cookies from Chromium and Firefox browsers, pulls tokens from Discord and Steam, and raids cryptocurrency wallet files. Everything collected is compressed into a ZIP archive before being sent out, keeping transfers small and harder to detect.
To survive reboots, Salat uses three separate persistence methods. It copies itself to a folder under a disguised name, such as explorer.exe or svchost.exe, and marks the file as hidden from view. It also creates a scheduled task that runs at every user login and repeats every 30 minutes, and it adds a registry key to launch itself each time Windows starts.
Security teams are advised to monitor for unusual outbound connections over QUIC or WebSocket protocols, especially to unfamiliar domains. Watching for hidden system files that share names with legitimate Windows processes is equally important.
Keeping endpoint tools updated to detect Go-based malware and auditing unknown scheduled tasks will significantly reduce the risk of a Salat infection going undetected.
Indicators of Compromise (IoCs):-
| Type | Indicator | Description |
|---|---|---|
| SHA-256 | 25802493e7ef64523d6ab13ad6e5555b2b08fd4576ae2edd905ad939d256aa3a | Salat malware sample hash |
| SHA-1 | b8f4a8c2e7d1f3a9b5c6d8e0f1a2b3c4d5e6f7a8 | Salat malware sample hash |
| MD5 | 25802493e7ef64523d6ab13ad6e5555b | Salat malware sample hash |
| URL | https://salator[.]es/sa1at/ | Salat C2 server endpoint |
| URL | https://wrat[.]in/sa1at/ | Salat C2 server endpoint |
| URL | https://websalat[.]top/sa1at/ | Salat C2 server endpoint |
| URL | https://salat[.]cn/sa1at/ | Salat C2 server endpoint |
| URL | https://wrat[.]in:992/sa1at/ | Salat C2 server alternate port endpoint |
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.







No Comment! Be the first one.