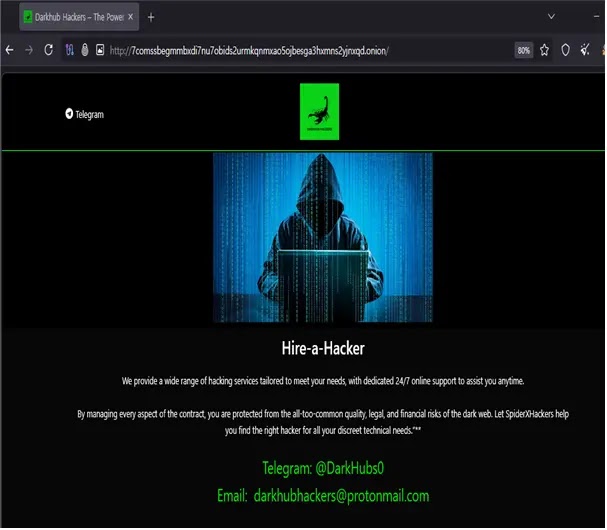
Darkhub Hacking-for-Hire Portal: Crypto Advertises Fraud
A new dark web platform, Darkhub, has surfaced on the Tor network, openly advertising a comprehensive suite of hacking-for-hire services. As detailed in a recent security analysis, this illicit...
A new dark web platform, Darkhub, has surfaced on the Tor network, openly advertising a comprehensive suite of hacking-for-hire services. As detailed in a recent security analysis, this illicit portal specifically promotes sophisticated
The platform targets everyday people and organizations alike. Darkhub’s listed services include unauthorized access to Instagram, Telegram, and WhatsApp accounts, along with email compromise, mobile phone monitoring, and real-time location tracking of individuals.
It also claims to offer cryptocurrency-related fraud services, unauthorized bank account access, and the ability to alter credit scores, covering a surprisingly wide range of criminal intent in a single storefront.
Researchers at Oasis Security identified and analyzed the platform, revealing details about its infrastructure and the true nature of its advertised offerings.
Their investigation found that Darkhub is not just hiding behind the anonymity of the Tor network. A publicly accessible IP address was linked to the service, suggesting that parts of its backend are exposed beyond the encrypted Tor environment, a notable detail for any service that depends on staying hidden.
One aspect of Darkhub’s catalog drew particular attention from analysts. Categories like fund recovery and credit score manipulation are well-known hallmarks of advance-fee scam operations.
Darkhub’s Service Scope and Crypto Fraud Angle
These schemes prey on prior fraud victims, promising to recover lost money in exchange for an upfront payment that is never returned. Their presence in the service listing suggests Darkhub may be targeting two groups at once: outside victims and its own paying clients.
This kind of layered deception is not uncommon in the dark web services space. Many platforms advertising offensive hacking capabilities are, in practice, scam operations that collect payment without ever delivering anything real. While Darkhub’s true technical capability cannot be confirmed through external observation, the warning signs throughout its service catalog are very hard to overlook.
The range of services advertised by Darkhub covers nearly every recognizable form of digital intrusion. Beyond social media hacking and phone surveillance, the platform explicitly lists cryptocurrency-related services, which in this context almost certainly involves facilitating theft or large-scale fraud involving digital assets.

Crypto fraud is one of the fastest-growing areas of cybercrime, and platforms like Darkhub lower the barrier to entry for people with no technical background. By offering these capabilities as a paid service, the platform makes it possible for anyone to commission a digital crime. Its contact channels include a Telegram handle and a ProtonMail address, keeping interactions deliberately anonymous.

The inclusion of “recover stolen funds” alongside cryptocurrency services is especially revealing. People who have already lost money to crypto scams are among the most vulnerable targets for follow-up fraud, making them ideal marks for a platform openly promising recovery services it may never actually deliver.
Infrastructure Exposure and Bulletproof Hosting Links
A key finding from the Oasis Security investigation was the identification of a publicly routable IP address tied to Darkhub.
Using the dark web intelligence platform Arthur, researchers traced the site’s infrastructure to a U.S.-based hosting provider operating under ASN AS44259. This provider has previously been flagged in third-party reports for exhibiting bulletproof hosting characteristics.
Bulletproof hosting providers are known for ignoring abuse complaints, making them a favored infrastructure choice for cybercriminal operations.
The provider has also been the subject of an ICANN compliance notice related to phishing-related domain abuse, and its marketing materials reportedly emphasize permissive content policies, which is precisely the kind of environment dark web operators seek out.
The IP address associated with Darkhub has not always been stable. Historical data shows it changed multiple times before settling at its current value as of January 12, 2026.
Whether those changes reflect provider migrations or operational adjustments remains unclear. Organizations monitoring dark web threats should treat any traffic linked to this infrastructure with serious caution.
| Type | Indicator | Description |
|---|---|---|
| Onion URL | 7comssbegmmbxdi7nu7obids2urmkqnmxao5ojbesga3hxmns2yjnxqd.onion |
Darkhub hacking-for-hire Tor hidden service address |
| IP Address | 38.127.***.*** |
Public IP address associated with Darkhub backend infrastructure |
| ASN | AS44259 | Autonomous System Number for ULTAHOST, the identified hosting provider |
[email protected] |
Operator contact email advertised on the Darkhub platform | |
| Telegram Handle | @DarkHubs0 |
Operator Telegram contact advertised on the Darkhub platform |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.








No Comment! Be the first one.