New Malware Evades Detection via Obfuscation & St Uses Staged
A newly uncovered malware campaign is actively targeting government employees in Pakistan. Threat actors are deploying carefully crafted spear-phishing emails that combine obfuscation and staged...
A newly uncovered malware campaign is actively targeting government employees in Pakistan. Threat actors are deploying carefully crafted spear-phishing emails that combine obfuscation and staged payload delivery, tactics designed to help the malicious code remain hidden from security tools.
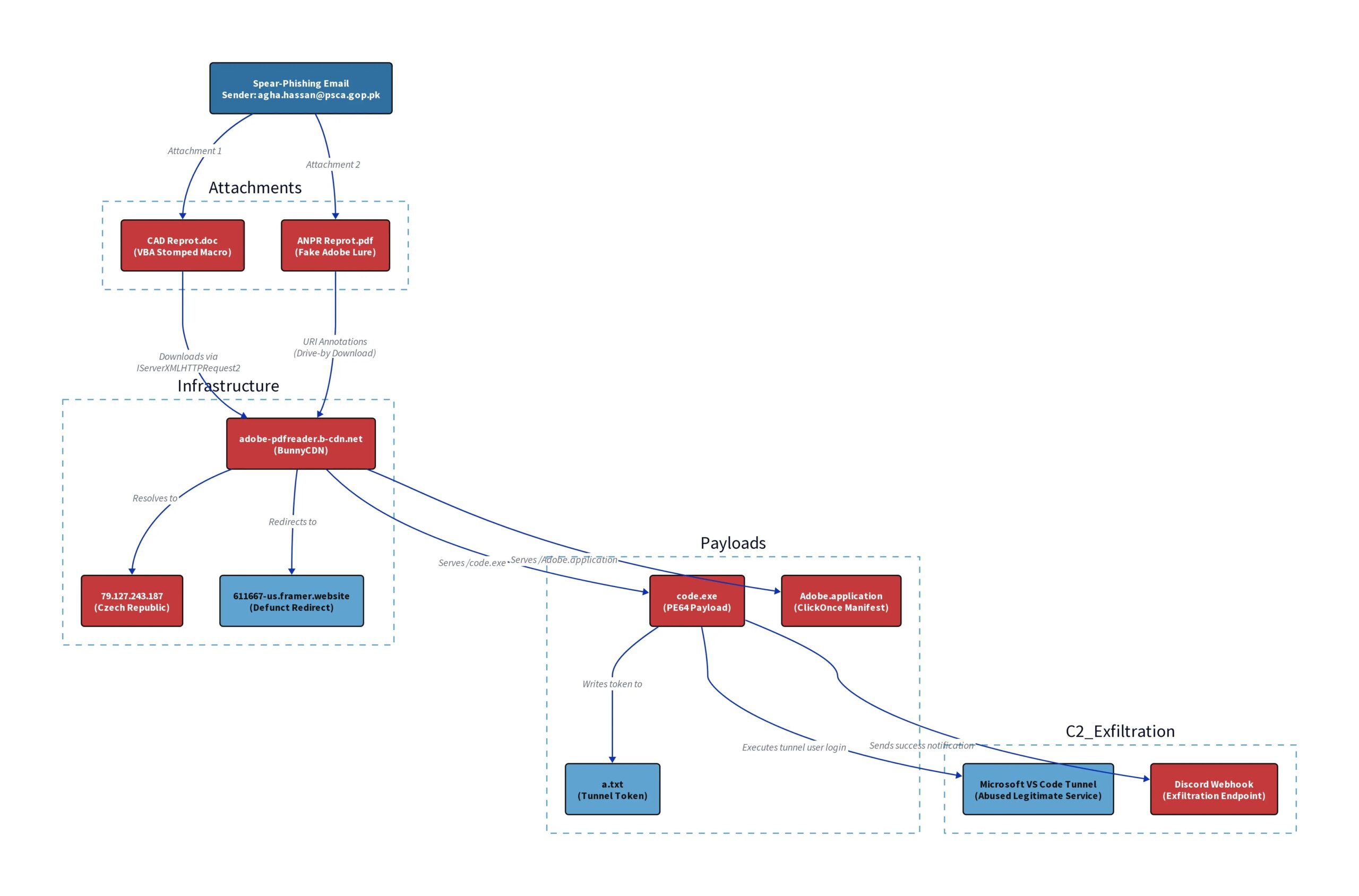
The attack was directed at staff from the Punjab Safe Cities Authority (PSCA) and PPIC3, with the threat actor impersonating an internal consultant and referencing a government project called the “Safe Jail Project.” This approach reflects a growing tactic where attackers use trusted institutional names to gain credibility.
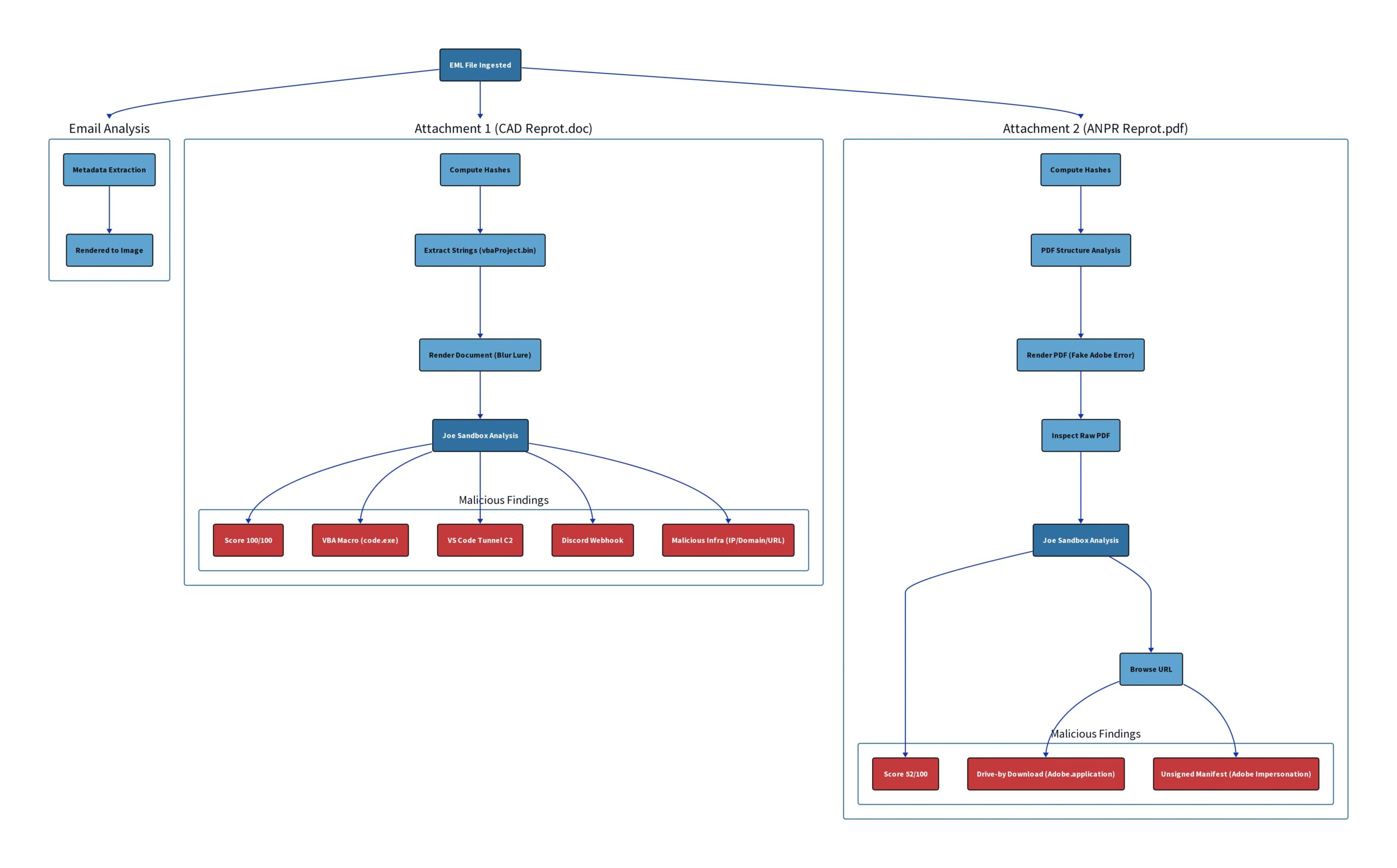
The campaign delivers two malicious attachments through the same email. The first is a Word document named “CAD Reprot.doc,” a deliberate misspelling often seen in threat-actor-crafted files.
The second is a PDF named “ANPR Reprot.pdf,” which shows a fake Adobe Reader error designed to push users into downloading a harmful file. Both attachments pull payloads from the same infrastructure hosted on BunnyCDN, a legitimate content delivery network, making the traffic harder for security tools to flag.
JoeReverser analysts identified the full scope of this campaign after a thorough sandbox analysis, assigning the Word document a perfect score of 100 out of 100 for malicious behavior.
Working at a 95% confidence level, analysts confirmed the campaign was built to establish persistent remote access on compromised machines.
Detection signals from Suricata, Sigma, YARA, ReversingLabs at 52%, and VirusTotal at 56% all supported the same verdict, leaving no reasonable doubt about the attack’s intent.
What makes this campaign especially concerning is its use of Microsoft’s legitimate VS Code tunnel service as a hidden command-and-control channel.
Once the payload code.exe is dropped into the victim’s temporary folder and executed, it routes traffic through Microsoft’s own infrastructure, making the connection look like routine developer activity.
The threat actor also used Discord webhooks to receive instant notifications whenever a system was compromised, a low-profile method that bypasses most network-level monitoring tools.
The attack scored a perfect malicious rating across all sandbox tests, and no known malware family match was found in Malpedia, confirming this is a custom-built toolset made for a specific target.
Joe Sandbox confirmed the full chain through Web IDs 1903908, 1903907, and 1903906, each covering a different part from the email to the final PDF.
Multi-Stage Delivery and VBA Stomping
The most technically significant aspect of this campaign is how the attacker engineered each delivery step to pass through security defenses without being caught.
The Word document relies on a technique called VBA stomping, where the visible macro source code is completely removed, leaving only the compiled p-code behind.
Most antivirus tools that check macro content in Word documents scan the readable portion and find nothing, letting the hidden logic run without triggering an alert.
Once the victim clicks “Enable Content” on the blurred document, the macro’s DownloadAndExfil function activates quietly in the background.
It uses a COM-based HTTP object to pull code.exe from the domain adobe-pdfreader.b-cdn.net and writes it to the system’s temp folder through ADODB.Stream.
The PDF runs a parallel path, where clicking the fake “Update PDF Reader” button starts an automatic download of an unsigned .NET ClickOnce manifest that impersonates Adobe software. Both paths feed from the same infrastructure, giving the attacker two independent chances to compromise the target.
Security teams are advised to treat any document that asks users to enable macros or install software updates as a potential threat, particularly when arriving from unfamiliar senders.
Blocking CDN domains not linked to approved services, monitoring unusual VS Code tunnel activity on enterprise endpoints, and flagging Discord webhook connections from non-browser applications are practical steps that can help detect or stop similar attacks early.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.