macOS textutil & KeePassXC Vulnerable Researchers Warn
Security researchers are warning that two widely trusted applications, macOS textutil and KeePassXC, can become dangerous attack primitives when integrated into automated pipelines that process...
Security researchers are warning that two widely trusted applications, macOS textutil and KeePassXC, can become dangerous attack primitives when integrated into automated pipelines that process attacker-controlled input. Their detailed
The issue is not about broken code. There is no memory corruption, no authentication bypass, and no code execution involved in either case. The risk lives at the system design level, not inside the binary.
Automated pipelines commonly treat local utilities as safe, offline, and bounded by default. When those assumptions turn out to be wrong, they open the door to unexpected network requests, resource exhaustion, and exposure of trusted backend infrastructure to outside influence without triggering any visible alert.
Cipher Security Labs researchers identified both behaviors during controlled testing on macOS 26.3 (Build 25D125) using a local KeePassXC 2.8.0-snapshot build alongside repeatable differential command-line workflows.
Their findings made it clear that neither tool is defective. The real issue, as they explained, is that engineers and system builders routinely assume a safer behavior model than reality actually provides. The vulnerability is not the tool itself but the assumptions teams construct around it.
The first case involves macOS textutil, a system binary at /usr/bin/textutil used in scripts, CI jobs, and backend workers to convert or normalize documents. Engineers commonly treat it as offline-safe since it is a local, mature utility that only processes files already on the system.
The problem is that when textutil converts an HTML file containing remote references such as images or linked stylesheets, it silently fetches those resources over the network. A pipeline that assumes document conversion is a purely local, bounded operation does not account for this side effect at all.
The tests confirmed that plain HTML with no remote references produced zero outbound requests, while HTML containing remote image and stylesheet links triggered live HTTP fetches.
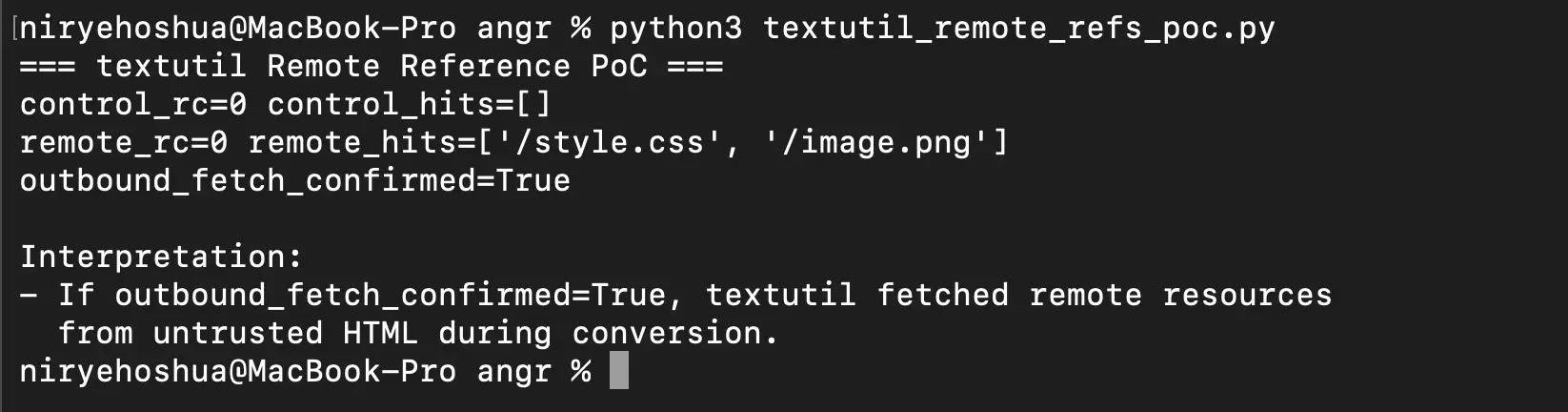
In a backend environment where an attacker supplies the HTML and the conversion worker has network access, this behavior functions as a server-side request primitive, similar in effect to server-side request forgery (SSRF), even though textutil operates exactly as intended.
Inside the KeePassXC KDF Boundary Problem
The second case focuses on how KeePassXC handles key derivation function (KDF) parameters stored inside KDBX database files.
Password managers are intentionally slow at key derivation because each unlock attempt must be computationally expensive enough to resist offline brute-force attacks. This is a security feature by design, not a software defect.
The concern researchers raised is that a crafted KDBX file can embed extreme transform-round values in its own metadata. When any system opens or processes that file, it must complete all the derivation work the file defines before moving forward.
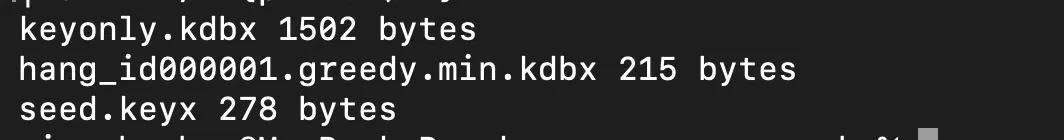
A standard KDBX file with roughly 1,000,000 transform rounds took about 0.06 seconds. A crafted file with 353,321,536 rounds took approximately 7.35 seconds, a slowdown factor of 119 times.
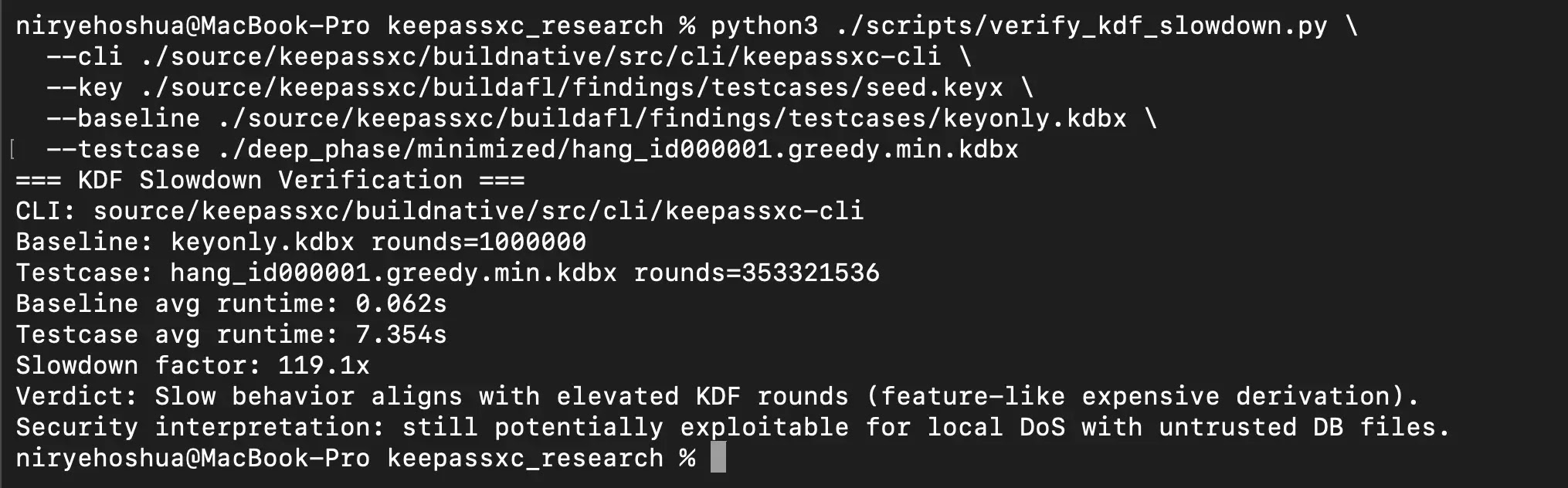
While this confirms this cost comes entirely from metadata, not file size. For a single user manually opening one personal database, this delay is manageable at most.
For automated systems that scan, validate, or batch-process many KDBX files at once, the same behavior can exhaust CPU resources, stall workers, and degrade overall service availability.
The researchers were clear that no passwords were exposed and no cryptographic primitive was broken in this process. The risk is entirely about resource-consumption driven by attacker-supplied metadata embedded inside the file.
Researchers recommend that teams using textutil in untrusted-input pipelines apply the -noload flag, run conversion workers inside sandboxed environments, sanitize remote-bearing HTML before processing, and enforce deny-by-default egress filtering.
For KeePassXC deployments, recommendations include applying maximum KDF parameter thresholds, displaying explicit warnings before processing extreme values, enforcing bounded processing time per file, and isolating untrusted file handling from critical operational paths.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.