Hackers Steal User Data Using 108 Mal Chrome Extensions
A widespread cyber espionage campaign is actively leveraging 108 malicious Google Chrome extensions. According to a recent report from Socket, these extensions are explicitly designed to steal...
A widespread cyber espionage campaign is actively leveraging 108 malicious Google Chrome extensions. According to a recent report from Socket, these extensions are explicitly designed to steal sensitive user data and hijack active web sessions.
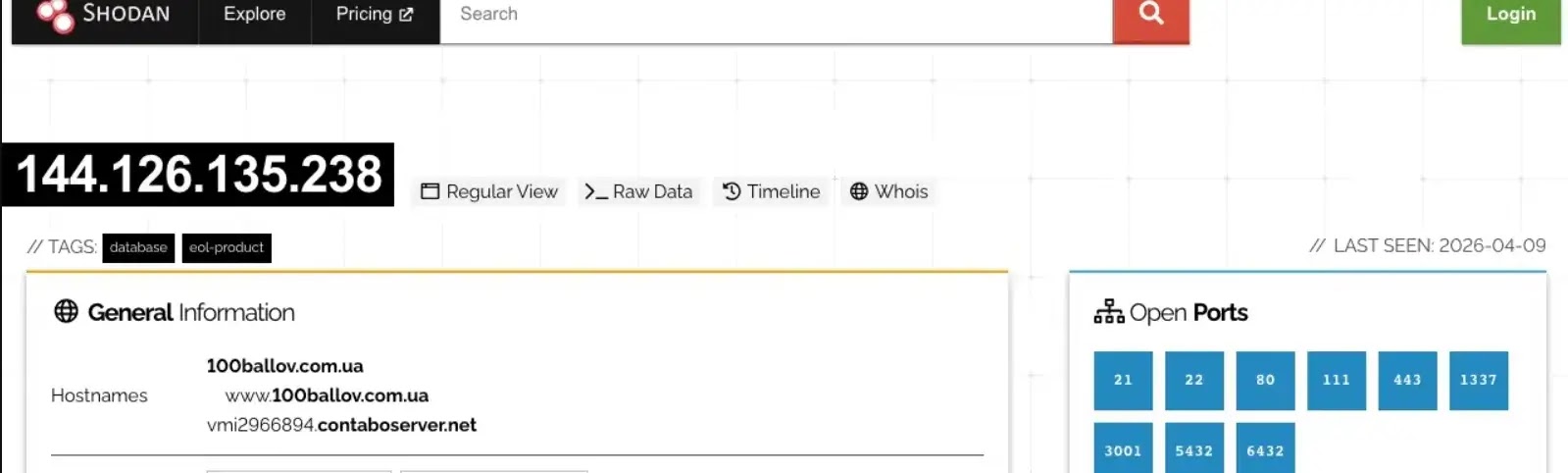
The attackers manage this extensive operation through a highly organized, shared Command and Control (C2) infrastructure.
This centralized setup makes it significantly easier for threat actors to scale their data theft efforts across thousands of potential victims without needing to build new backends for every tool.
Rogue Extensions Funnel User Data
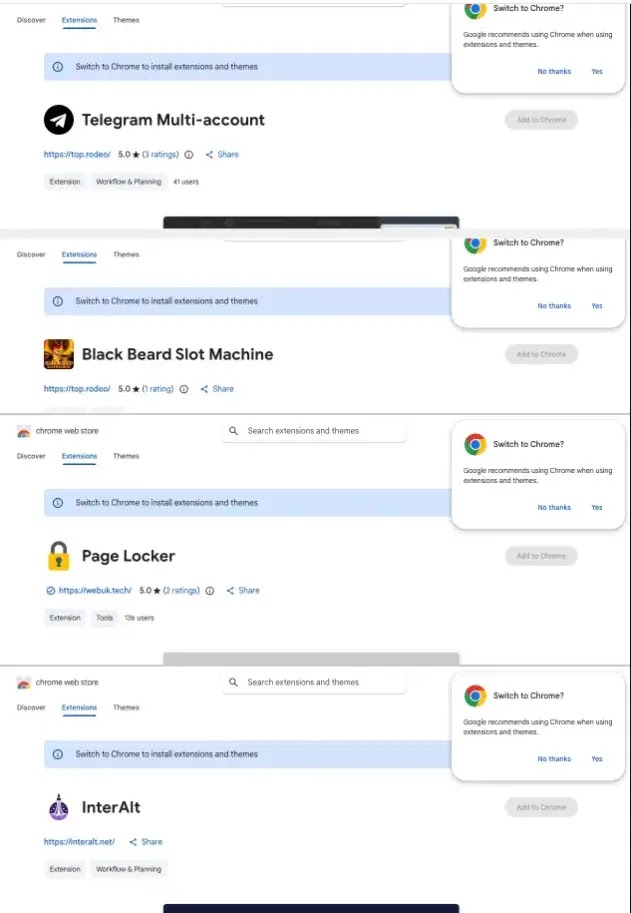
Often disguised as legitimate productivity tools, utility apps, or browser enhancements, these rogue extensions trick users into downloading them.
Once installed, their true malicious intent is activated, hidden within the background scripts. The malware silently monitors web browsing activity and harvests critical personal and corporate information.
Because the attackers rely on a shared C2 network, all 108 extensions funnel their stolen data back to the same group of malicious servers.
This shared backend allows the hackers to efficiently update their malicious payloads, issue new commands, and process massive amounts of stolen information simultaneously.
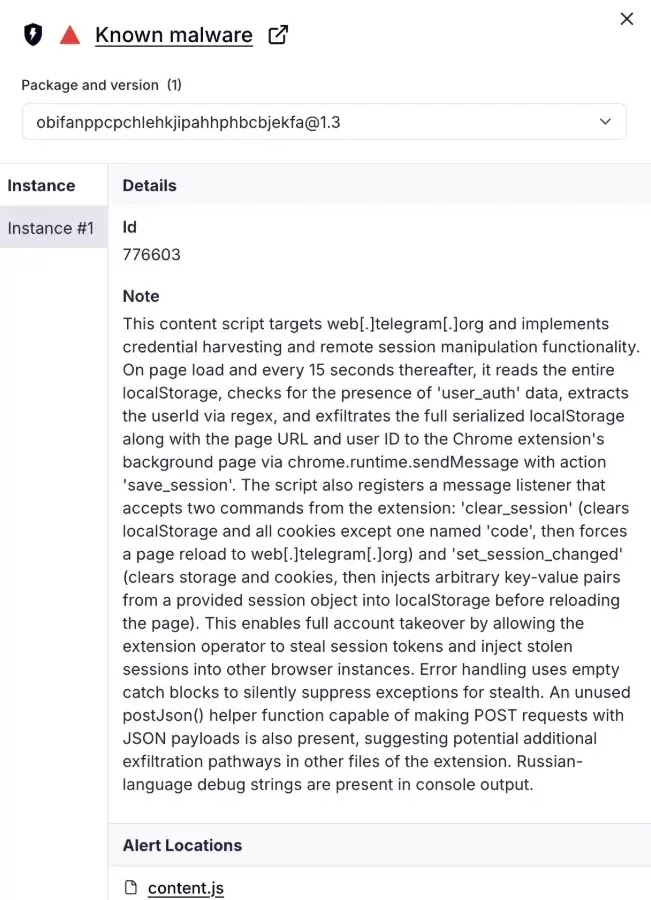
The primary objective of this coordinated campaign is data exfiltration and session theft. The extensions are programmed to copy browser cookies and active session tokens silently, and to save login credentials.
Stealing session tokens is a particularly dangerous and highly effective tactic because it allows hackers to bypass multi-factor authentication (MFA) completely.
Armed with a valid session token, an attacker can directly access secure accounts, including corporate email, financial dashboards, and internal company portals, without ever needing the user’s actual password.
This presents a critical risk to enterprise environments, where a single compromised browser can lead to a devastating network breach.
To evade detection, the hackers behind these extensions utilize various stealth techniques. The malicious code is often heavily obfuscated to hide its true purpose from automated security scanners.
In many cases, extensions delay the execution of their data-stealing functions to bypass initial security checks during installation.
Furthermore, the shared C2 infrastructure frequently changes its domain names and IP addresses, complicating security teams’ efforts to block malicious network traffic permanently.
Mitigating this browser-based threat requires proactive security management.
According to Socket research, organizations should immediately audit all Chrome extensions installed on corporate devices and enforce strict enterprise policies that only allow pre-approved, vetted extensions.
Individual users must regularly review their browser add-ons and delete any suspicious or unused ones.
Additionally, network administrators should actively monitor outbound network traffic for connections to unrecognized servers and deploy endpoint protection solutions that detect abnormal data exfiltration from web browsers.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.