LinkedIn’s Hidden Code Secretly Scans Searches Your
Hidden JavaScript embedded within LinkedIn silently scans for installed software on a user’s computer whenever the platform is opened in a Chrome-based browser. This operation proceeds without...
Hidden JavaScript embedded within LinkedIn silently scans for installed software on a user’s computer whenever the platform is opened in a Chrome-based browser. This operation proceeds without the user’s knowledge, consent, or any disclosure within LinkedIn’s privacy policy.
Table Of Content
A revealing investigation conducted by the European advocacy group Fairlinked e.V., under the campaign name “BrowserGate,” has uncovered what researchers describe as one of the largest corporate espionage and data breach scandals in digital history.
Microsoft’s LinkedIn, the world’s largest professional networking platform with over one billion users, is running covert code that probes visitors’ browsers for thousands of installed extensions, compiles the results, encrypts them, and transmits everything back to LinkedIn’s servers and to third-party companies.
What the Hidden Code Actually Does
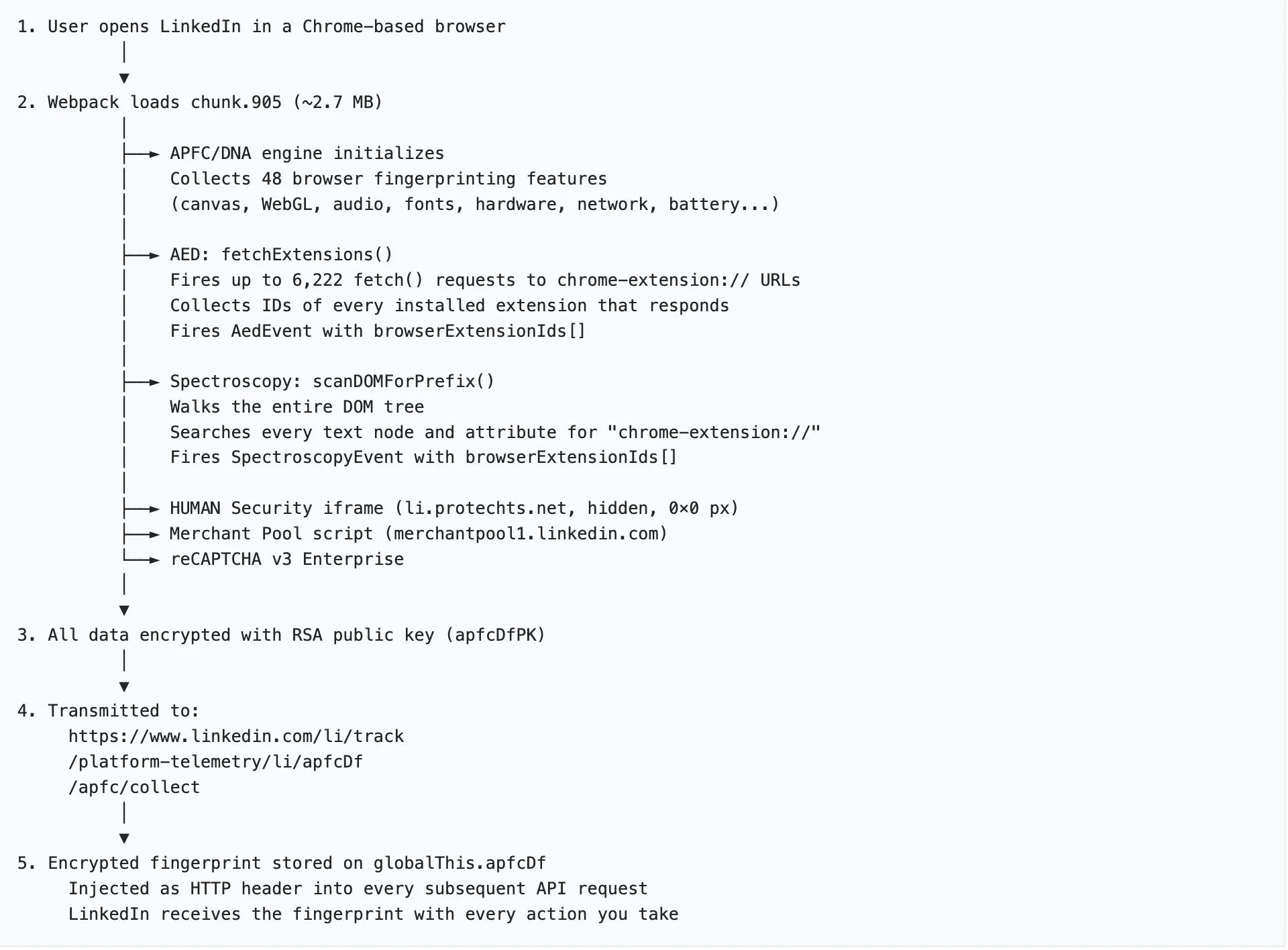
The mechanism is technically precise and deliberately invisible. Each time a user loads a LinkedIn page, a fingerprinting script executes silently, probing for known browser extension identifiers by attempting to access files that extensions can optionally expose to websites. If a file loads, the extension is confirmed present. If not, it isn’t. The entire scan takes milliseconds, and the user sees absolutely nothing.
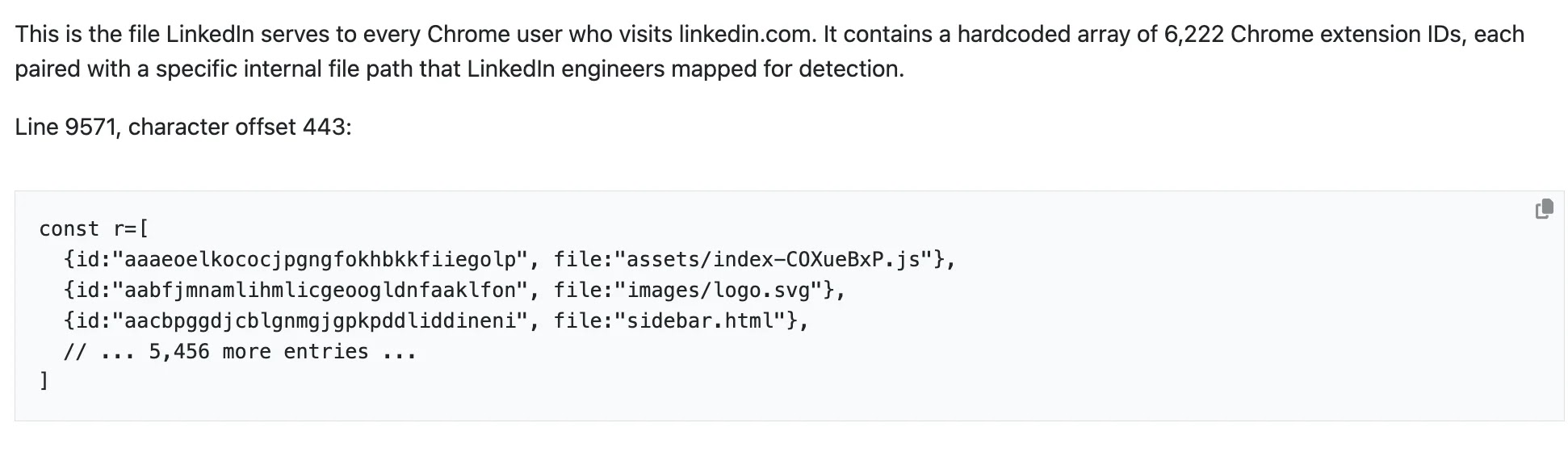
LinkedIn’s JavaScript bundle contains identifiers for over 6,167 browser extensions. The scan is exclusively triggered on Chromium-based browsers Chrome, Edge, Brave, Opera, and Arc — through a built-in isUserAgentChrome() function check. Firefox and Safari users are not currently affected.
What makes this surveillance uniquely dangerous is context: LinkedIn accounts are tied to real names, employers, and job titles. Every detected extension is instantly matched to an identified individual.
Because LinkedIn also knows where each user works, these individual scans aggregate into detailed corporate intelligence profiles revealing which software tools entire organizations use, without those organizations’ knowledge or consent.
The Sensitive Data Being Harvested
The scope of what LinkedIn can infer from scanned extensions goes far beyond software preferences. BrowserGate researchers identified the following high-risk categories among the 6,222 tracked extensions:
- 509 job search tools — including extensions for Indeed, Glassdoor, and Monster — exposing users secretly looking for work on the very platform where their current employer can see their profile.
- Religious belief indicators — extensions that identify practicing Muslims and other faith communities.
- Political orientation markers — news source selectors and partisan fact-checking tools revealing users’ political leanings.
- Disability and neurodivergent tools — ADHD management apps, autism support extensions, and screen readers.
- 200+ direct competitor products — including Apollo, Lusha, ZoomInfo, and Hunter.io, which LinkedIn uses to map which companies use rival sales intelligence platforms.
Under the EU’s General Data Protection Regulation (GDPR), data revealing religious beliefs, political opinions, and health conditions is classified as Special Category Data, not merely regulated, but prohibited from processing without explicit consent. LinkedIn has no consent, no disclosure, and no legal basis for collecting it.
The surveillance extends beyond LinkedIn’s own servers. BrowserGate researchers identified an invisible tracking element loaded from HUMAN Security (formerly PerimeterX), an American-Israeli cybersecurity firm, a zero-pixel-wide element hidden off-screen that sets cookies without user knowledge.
A separate fingerprinting script runs from LinkedIn’s own servers, and a third script from Google executes silently on every page load. All of it is encrypted. None of it is disclosed.
HUMAN Security’s technology is embedded on hundreds of major websites, ostensibly to distinguish real users from bots, but BrowserGate contends the data flows back to third-party servers, building detailed device profiles of every visitor.
The BrowserGate investigation further alleges that LinkedIn is leveraging its covert scanning capability for competitive enforcement. LinkedIn has already sent legal threats to users of third-party tools, using data obtained through this hidden scanning to identify and target those users.
Simultaneously, LinkedIn dramatically expanded the scale of its surveillance. The scan list grew from roughly 461 products in 2024 to over 6,000 by February 2026 — a 1,252% increase — targeting precisely the tools the DMA was designed to protect.
The company also alleged that the BrowserGate campaign was driven by someone whose account had been banned for violating LinkedIn’s Terms of Service.
Independent researchers, however, note this practice dates back to at least 2017, when LinkedIn was scanning for just 38 extensions. By February 2026, that number had grown to nearly 3,000, and has since more than doubled.
Fairlinked e.V. states the practice is illegal and potentially criminal in every jurisdiction it has examined. The combination of undisclosed special-category data collection, covert third-party transmission, and alleged regulatory deception presents serious exposure under GDPR, the ePrivacy Directive, and the DMA.
The combined user base of the scanned extensions amounts to 405 million people — making BrowserGate one of the largest undisclosed data collection operations in the history of the commercial internet.
Regulators across the EU have been notified. Legal proceedings are being organized. For now, every LinkedIn user on a Chromium browser remains a subject of this silent, daily scan.
How to Protect Yourself
Users concerned about the scanning have several immediate options:
- Switch to Firefox or Safari for LinkedIn access — the detection method relies on Chrome’s extension architecture, which Firefox’s design prevents
- Create a LinkedIn-only Chrome profile with zero extensions installed, breaking the surveillance chain
- Use Brave browser with fingerprinting protection enabled, which blocks the detection mechanism
- Audit your installed extensions using BrowserGate’s searchable public database to check if your tools are being tracked
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.