Leak Bazaar Structures Stolen Corporate Data as Criminal Market
Threat actor “Snow” of SnowTeam launched a new criminal service, Leak Bazaar, on March 25, 2026. The announcement appeared as an advertisement on the Russian-speaking TierOne (T1)...
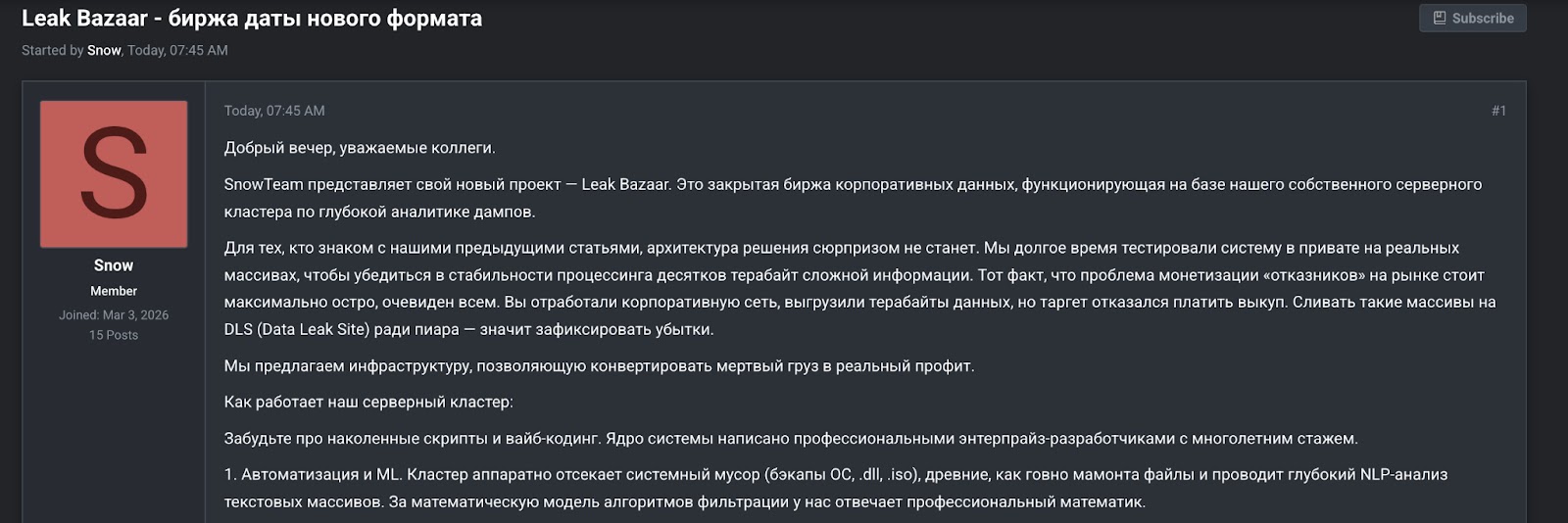
Threat actor “Snow” of SnowTeam launched a new criminal service, Leak Bazaar, on March 25, 2026. The announcement appeared as an advertisement on the Russian-speaking TierOne (T1) cybercrime forum.
The platform is not a traditional data leak site. Instead, it presents itself as a post-exfiltration processing service — one that takes raw stolen corporate data and converts it into organized, sellable intelligence for criminal buyers.
The timing of Leak Bazaar’s emergence matters because it reflects a growing frustration within criminal ecosystems. When a ransomware victim refuses to pay, the stolen data often loses its immediate leverage.
Raw data dumps tend to be large, disorganized, and full of noise — system files, duplicate records, malformed exports, and unreadable database archives.
Leak Bazaar claims to solve that exact problem by cleaning, parsing, and packaging stolen data into something buyers can actually use.
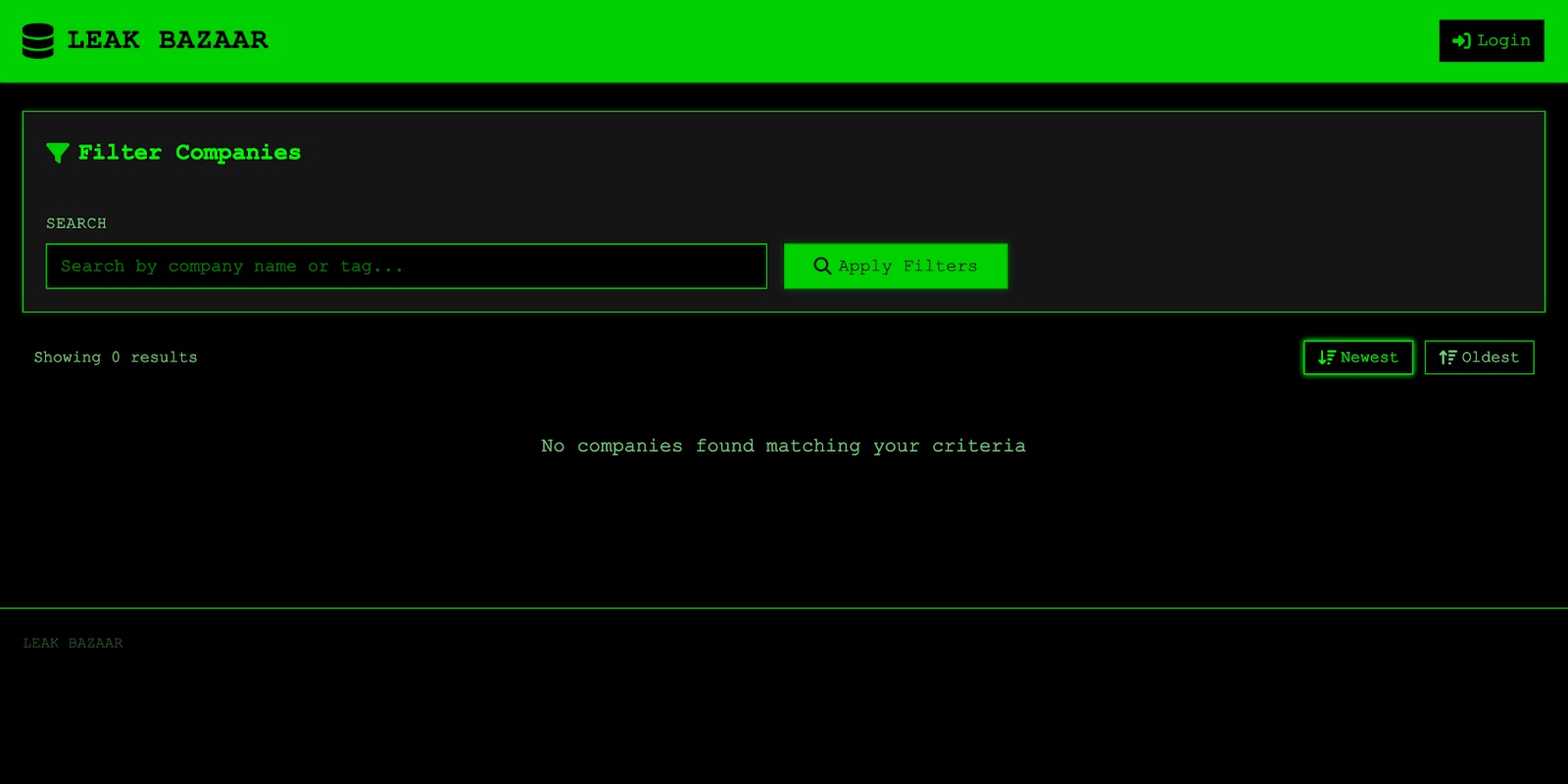
The platform’s hidden service went live on the same day Snow’s advertisement appeared on the forum.
Flare researchers noted that this advertisement stands out not because of its branding, but because it identifies a specific operational gap in the extortion economy and builds an entire business model around filling it.
Rather than simply hosting stolen archives, the platform describes a server infrastructure designed for deep analytics of large corporate dumps — using ML-assisted text analysis, automated removal of system debris, database reverse engineering, ERP parsing, and human analyst validation before any material reaches buyers.
This combination of machine processing and human review positions Leak Bazaar as a managed intelligence service rather than a raw data warehouse.
The platform targets corporate data from organizations with annual revenues above ten million dollars, requiring volumes of at least 100 GB and preferring one terabyte or more.
Snow specifically requests unpublished, predominantly English-language material — a clear quality filter that signals the platform’s focus on commercially valuable, resalable content.
All transactions are reportedly conducted through the Exploit guarantor service, adding transactional discipline to the marketplace.
Leak Bazaar offers a seventy-thirty revenue split in favor of the data supplier, with two sales formats available: an exclusive one-time purchase that removes data from the market permanently, and a multi-buyer model that allows repeated sales to multiple buyers over time.
Organizing Stolen Data Around Criminal Demand
One of the most significant aspects of Leak Bazaar is how it categorizes stolen material around buyer demand rather than around the original structure of the victim’s data.
Snow describes dividing processed content into high-value segments including quarterly financial reporting, mergers and acquisitions data, research and development files, and personal data records.
This market segmentation approach turns what would otherwise be an unwieldy archive into targeted products aimed at different criminal consumers — financial traders, corporate competitors, and identity fraud operators. Groups like Anubis have taken a comparable approach, producing detailed investigative breakdowns of victim datasets.
Leak Bazaar appears to be formalizing and commercializing that same logic at a much larger scale. A typical database dump sitting in SQL, SAP, or Oracle export formats holds limited usable value unless someone can restore and interpret it.
By converting complex archives into clean spreadsheets and structured extracts, Leak Bazaar claims it can unlock value that would otherwise remain buried inside raw exfiltrated material.
The platform’s human analyst validation step adds a final layer of credibility to processed outputs, making the product more attractive to buyers who cannot afford to sift through terabytes of noise.
Security teams should treat Leak Bazaar’s emergence as a clear signal that a failed ransom negotiation no longer marks the end of data exposure risk.
Once corporate data enters a platform like this, it can be disassembled, priced by segment, and repeatedly sold to multiple buyers over a long period.
Organizations are strongly advised to implement continuous dark web monitoring for exposed data, conduct regular data classification audits to understand exfiltration risks, and build incident response protocols that extend well beyond the initial breach event.
The long tail of data exposure has now become a structured, repeatable criminal operation.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.